Videokatalog
http://bit.ly/1iLhdqv
http://goo.gl/9h6btY
Videos on USB
Remarkable Videos
Interview with Jutta Hipp
Ehsan Khoshbakht
"At 11 A.M. on November 18, 1955, a nervous figure stepped off the gangplank of the S.S. New York at Pier 88 in Manhattan and gazed around with myopic eyes at the unfamiliar landscape of a strange new country. Jutta Hipp had arrived in America," remembers Leonard Feather of the arrival of the person whose life and jazz recordings is the subject of this post.
Before Miss Jutta Hipp's arrival in New York, she was a professional painter and musician in Germany. Born in February 4, 1925 in Leipzig, she started playing jazz in the war years, and not long after the war, she was leading her own combos. Feather discovered her "in the crowded cellar club in Duisberg," and invited her to go to US.
We have to wait for the publishing of the first English language book about her (will come out soon) to explain why she suddenly stopped playing jazz and apparently became a seamstress! But some say, she was always nervous of playing with American jazz musicians, in a male dominated environment.
Hipp's American experience was shortly ended up in obscurity, and she returned to her first interest, painting. Though she stayed in New York, and died there in 2003.
This audio file is a radio programme, with interviews and music clips, in German.
Jutta moved to New York City in 1955, and her first recordings were live at the Hickory House albums, now out-of-print and copies on the web, too expensive to afford. In July of the same year, she went to the studio with Zoot Sims to record probably her most famous LP, in a quintet format. 1956 was also marked by her appearance in Newport Jazz Festival.
LEXAR 8GB - Surveillance
Edward Snowden, Interview, 26.1.2014
Transcript
"There are significant threats but I sleep very well. There was an article (im Cache) that came out in an online outlet called BuzzFeed where they interviewed officials from the Pentagon, from the National Security Agency and they gave them anonymity to be able to say what they want, and what they told the reporter was that they wanted to murder me. These individuals - and these are acting government officials - they said they would be happy, they would love to put a bullet in my head, to poison me as I was returning from the grocery store and have me die in the shower." (Edward Snowden, Dezember 2013, Quelle: ndr)
Laura Poitras, Surveillance Teach-In (YouTube)
Laura Poitras
Whitney Museum of American Art, April 20, 2013
Award-winning filmmaker Laura Poitras explores issues of war, justice, and power. Her current film trilogy, focusing on America post 9/11, documents the Iraq War, secret state surveillance, and the suspension of the rule of law in the "war on terror". Here, Poitras gives the floor to Jacob Appelbaum, computer security researcher, privacy advocate, hacker, and human rights activist, and Bill Binney, National Security Agency whistleblower. Appelbaum and Binney discuss domestic surveillance and the ways in which technological innovations have allowed for increasingly ubiquitous access into what was once private information. (Source)
Thomas Drake Ntl Press Club 2013
Thomas Drake, a former Senior Executive at NSA who was charged under the espionage act after he blew the whistle on waste and fraud and illegal activity at the intelligence agency, spoke at a March 15, 2013 National Press Club luncheon. Drake's event was part of the club's celebration of Sunshine Week, a national initiative to underscore the importance of open government and freedom of information.
LEXAR 8GB - 29C3
Enemies of the State: What happens When Telling the Truth about Secret US Government Power Becomes a Crime
Jesselyn Radack, Thomas Drake, William Binney
Blowing the Whistle on Spying, Lying and Illegalities in the Digital Era.
Panel presented at 29C3, 27 Dec. 2013. Q&A afterward is not included in this video.
Published on Dec 27, 2013
Quotes from Thomas Drake's presentation
- "I have done nothing wrong, having nothing to hide..."
In a secret surveillance state, you don't get to define what's wrong or hidden - the government does!
- Democracies die behind closed doors.
Judge Damon J. Keith in a ruling declaring that the Bush administration acted unlawfully in holding deportation hearing in secret on August 27, 2002
- When government begins closing doors, it selectively controls information rightfully belonging to the people.
Selective information is misinformation. The Framers of the First Amendment did not trust any government to separate the true from the false for us. They protect the people against secret government.
- In my recently concluded past the government wanted to put me in prison for telling the truth as a whistleblower and exposing government wrongdoing and illegalities. Government [in his speech: "decided to find out"] found out everything they could about me and turned me into an enemy of the state. It was the truth that kept me free.
- 9/11 opened up Pandora's Box: Subversion of the Constitution, privacy and ALL data became fair game.
- Bottomline:
- Sold out national security to big business and also violated the Constitution
(all was so unnecessary)
- American ingenuity and the Constitution were quite sufficient to protect and defend the country with the best and under the Law.
- There was NO need to go to the dark side.
- Context Setting:
- Data absent context is data with no meaning and all data is value laden.
- Lose the context, make up the meaning - incredibly seductive to manage and manipulate data - and for other ends.
- The "Dark Side" of innovation:
- At best? - Pursuit of a fraudulent multi-billion dollar military congressional industrial intelligence complex.
- mulit-"buy versus make" program.
- At worst? - Blatant ignorance and disregard for policy under the Federal Acquisition Regulations and the 4th Amendment of the Constitution
Either way, same result: critical breakthrough IT, security and defense innovation and ingenuity denied to the American people with an incalculable loss of intelligence.
The great historical tragedy of what could have been - including the disruption, even the prevention, of 9/11.
What global commons do we want to keep?
- Consider this: Having the power to collect and analyze data - especially on people is seductively powerful - especially when done without the person's permission and particularly when done in secret - the ultimate form of control.
- The real problem is centralized government itself NO MATTER WHAT ITS POLICIES. The very Future of Liberty is at stake! Right here, right now.
- What Internet Do We Want to Keep?
- What can technology do to pir privacy and what happens to our very freedom, when placed in the wrong hands - hands that are increasingly recognized as a real threat to the Internet, but it is even more frightening and unconstrained when controlled by "secret " government hands.
- Orwell's 1984 is real and now already screamingly relevant.
- Only the government can create a police state, and our technology can now make that happen.
- How many want to live inside a virtual public prison surrounded by a digital fence?
- What Do We Do? Points to Ponder:
- Is it an advancement in our society to give up our privacy because we are so enamored with technology and want advertisers and firms to market and share us" with all the digital data we give them and they have on us - opted in or not?
- Is our privacy now "fair game" to commercial and government interests?
- There is an obvious and looming dark side to it as well. So let's not kid ourselves.
- With the surveillance State there is no compromise with respect to the political imperative of controlling the internet.
- Protection of personal privacy and anonymity masking becomes a red flag threat.
- Personal privacy and communications deserve anonymized encryption, need VPN, anonymized proxies, need more people using privacy-protective packages ...
LEXAR 8GB - 29C3
Certificate Authority Collapse:
Will the EU Succeed in Regulating HTTPS? [29c3]
Axel Arnbak
"Hypertext Transfer Protocol Secure (HTTPS) has evolved into the de facto standard for secure web browsing. But in the security community, it has long been known that HTTPS is fundamentally broken, and this has been confirmed by alarming hacks and security breaches at several Certificate Authorities (CAs). To tackle the global collapse of trust in these central mediators of HTTPS communications and to augment HTTPS security, the EU has launched a proposal for strict regulation. Will these efforts succeed?"
LEXAR 8GB - 29C3
Die Wahrheit, was wirklich passierte und was in der Zeitung stand [29c3]
Wie Medien unsere Wahrnehmung beeinflussen
In den vergangenen Jahren wurde vor allem die Sprache von Politikern auf dem Congress beleuchtet. Aber die schwurbelnde Politiker sind noch nicht die ganze Wahrheit. Wir möchten das Ganze daher um den zweiten wichtigen Mitspieler bei der Konstruktion von Realität ergänzen, um die Presse bzw. die Medien. Die Äußerungen von Politikern (zum Beispiel auf Pressekonferenzen) sollen dabei der Mediendarstellung gegenübergestellt werden. Dabei wird deutlich werden, dass es zwischen Politikern und Medien Rückkopplungseffekte gibt.
Die einen rauf, die anderen runter -- Politik will abwiegeln, Medien wollen das Neue, Aufregende, sie bauschen auf. Wie zeigen sich solche Mechanismen in der Sprache? Politik und Medien sollen dabei kontrastiv betrachtet werden. Sie kommunizieren das Gleiche, aber nicht immer auf gleiche Weise. Wir fangen mit den Kleinigkeiten an, mit Dingen, die jedem schnell mal unterlaufen können (wenn auch nicht sollten). Dann arbeiten wir uns vor zu den ersten richtigen, vielleicht aber manchmal noch fahrlässigen Manipulationen, gehen über zu absichtlichen Aufbauschungen und Verfälschungen und kommen schließlich zu den ernst gemeinten Lügen, die das Publikum verschaukeln sollen. Am Ende schließlich werfen wir einen kurzen Blick auf die traurigen Folgen dieser Manipulationen. Gezeigt werden Techniken des Zuspitzens, Vereinfachens, Verdichtens, Aufbauschens, des Aufbaus (pseudo-)logischer Zusammenhänge und Vieles mehr. Als Beispiele dienen netzpolitische Debatten, der Europäische Stabilitätsmechanismus und von der Leyens Familien- und Sozialpolitik, vielleicht aus aktuellem Anlass auch noch ein Politikerrücktritt.
Redner: Kai Biermann, Martin Haase
EventID: 5181
Event: 29. Chaos Communication Congress [29c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: 27.12.2012 12:45:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 29C3
Our daily Job: Hacking the law [29C3]
The key elements of policy hacking
Legal systems have a huge impact on what we do as hackers, but also on internet users in general. Laws can restrict our freedom to use the internet in ways we deem to be natural and it can impede the tools which we hackers use on a daily basis. Which is not to say that laws cannot also protect our freedom and ensure that all bits are treated equally. Most importantly, these laws can be hacked and tweaked to fit our needs - like most things in this world.
So, how do you hack and tweak the law to protect our freedoms on the internet? In this talk we want to share Bits of Freedom's insights. We will point out the key elements of a successful lobby on both a national and European level. We will describe our approach to the net neutrality discussion in the Netherlands, now being the second country in the world to have enshrined this important principle in law. We will explain how we convinced the members of Dutch parliament to speak out clearly against the provisions of ACTA. Our experience in this field may prove valuable to individuals and organisations pursuing similar goals.
In short: this talk is a "HOWTO Hack the law".
Speaker: Ot van Daalen, Rejo Zenger
EventID: 5395
Event: 29th Chaos Communication Congress (29c3) by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Start: 27.12.2012 14:00:00 +01:00
License: CC-by-nc-sa
Redner: Kai Biermann, Martin Haase
EventID: 5181
Event: 29. Chaos Communication Congress [29c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: 27.12.2012 12:45:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 29C3
The grand EU data protection reform [29C3]
A latest battle report by some key actors from Brussels
The current European data protection directive is from 1995, which was when the internet had not hit Brussels' decision-makers yet. Now, 17 years later, it is being completely re-writen. Will it meet the challenges of the age of big data? Will it have any effect on non-EU data hoarders? How will it deal with user-generated consent? What is this strange new "right to be forgotten"? And what about privacy by design?
The presentation will give you the latest insight into the substance and state of play, and a first glance of the upcoming political battles in Brussels. The presenters are working directly at the core of the reform, both in the European Parliament and in the European digital rights community.
Speaker: Jan Philipp Albrecht, Katarzyna Szymielewicz, Kirsten Fiedler
EventID: 5274
Event: 29th Chaos Communication Congress (29c3) by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Start: 27.12.2012 17:15:00 +01:00
License: CC-by-nc-sa
LEXAR 8GB - Surveillance
Raegan MacDonald - Surveillance by Design, re-publica 2013
Raegan MacDonald (Access)
"Law enforcement is now attempting to broaden the Communications Assistance for Law Enforcement Act (CALEA) by requiring communications service providers to design their networks to make it easy and fast for law enforcement to perform wiretaps, pen-register, and trap-and-trace surveillance on a large number of people. In other words, the FBI wants service providers and equipment manufacturers to design their networks to be surveillance-friendly from the ground-up and starting at the product design phase. CALEA would then serve as a technology mandate, imposing design or architecture duties upon communications technology itself to "guarantee" that surveillance will always be fruitful. This is a far cry from simply requiring communications service providers to assist law enforcement in retrieving information or content that is reasonably available given the current state of technology." (Source, in cache)
6 May, 2013, re:publica, Berlin, 2013
"While the collection, storage and analysis of our data becomes ever cheaper and easier, governments around the world are eager to make the surveillance of citizens the default setting. Therefore, it has never been more important to explore countermeasures that would protect our fundamental right to privacy."
"While the European Union continues to take positive steps to ensuring that public and private bodies protect the privacy of citizens (for example through the Data Protection Regulation), much work remains to be done in addressing issues of due process in how governments use, protect, and request user data. Specifically, government requests for so-called "lawful access" to user data are trending in both democratic and non-democratic nations, presenting one of the greatest challenges for the protection of fundamental rights."
"This talk highlights this issue as well as provides a brief overview of the main challenges facing citizens in protecting their privacy, including some recent proposed laws in the EU and the US, that will show that bit by bit, our freedoms are being chipped away. The second half of the talk focusses on the need for domestic and international jurisprudence that protects our fundamental rights, and more broadly what can to be done to counter the surveillance state."
"From solutions such as Privacy by Design and expanding the use of privacy enhancing technologies, to the importance of transparency for both public and private actors, as well as how citizens can get involved and fight for the protection of their rights in the digital environment."
Source: 13.re:publica
LEXAR 8GB - SIGIN13
Home Network Horror Stories [SIGINT13]
In unseren typischen Heimnetzwerken tummelt sich mittlerweile eine Vielzahl unterschiedlicher netzwerkfähiger Geräte. Angefangen vom einfachen Internetrouter über den WLAN Access Point bis hin zum netzwerkfähigen Speicher und dem Multimedia Center. Alles Geräte die meist zum Ziel haben sich überaus einfach über ein Webinterface konfigurieren und anschl. sofort und möglichst einfach nutzen zu lassen. Diese Geräte werden im Hintergrund immer mächtiger und dementsprechend immer komplexer. Gleichzeitig muss sie ein Otto normal Benutzer bedienen und konfigurieren können. Niedrige Preise und dementsprechend niedrige Gewinnspannen machen eine sicherheitstechnisch ausgelegte Entwicklung eher unwahrscheinlich. Dieser Talk umfasst die Ergebnisse der Research Arbeiten an über 20 Geräten unterschiedlicher Hersteller. Es konnten bei nahezu allen Geräten gravierende Schwachstellen erkannt werden. Angefangen von einfachen Design Fehlern über typische und häufig anzutreffende Schwachstellen in Webapplikationen bis zu kritischen Lücken die eine vollständige Kompromittierung des Gerätes und unter Umständen des dahinter liegenden Netzwerkes mit sich führt.
In unseren typischen Heimnetzwerken tummelt sich mittlerweile eine Vielzahl unterschiedlicher netzwerkfähiger Geräte. Angefangen vom einfachen Internetrouter über den WLAN Access Point bis hin zum netzwerkfähigen Speicher und dem Multimedia Center. Alles Geräte die meist zum Ziel haben sich überaus einfach über ein Webinterface konfigurieren und anschl. sofort und möglichst einfach nutzen zu lassen. Diese Geräte werden im Hintergrund immer mächtiger und dementsprechend immer komplexer. Gleichzeitig muss sie ein Otto normal Benutzer bedienen und konfigurieren können. Niedrige Preise und dementsprechend niedrige Gewinnspannen machen eine sicherheitstechnisch ausgelegte Entwicklung eher unwahrscheinlich. Dieser Talk umfasst die Ergebnisse der Research Arbeiten an über 20 Geräten unterschiedlicher Hersteller. Es konnten bei nahezu allen Geräten gravierende Schwachstellen erkannt werden. Angefangen von einfachen Design Fehlern über typische und häufig anzutreffende Schwachstellen in Webapplikationen bis zu kritischen Lücken die eine vollständige Kompromittierung des Gerätes und unter Umständen des dahinter liegenden Netzwerkes mit sich führt.
Wird eine kritische Schwachstelle, die eine Kompromittierung des Gerätes ermöglicht, erkannt, trifft der Angreifer im nächsten Schritt typischerweise nicht auf die überaus bekannte x86-Architektur. Meist handelt es sich um eine Ausprägung von MIPS auf der unsere vorhandene Toolbox nicht out of the box funktionsfähig sind. Versucht man auf das überaus bekannte Metasploit Framework zurückzugreifen erkennt man sehr schnell, dass dieses kaum Funktionalitäten für die vorgefundene Architektur bietet. Das bedeutet wir arbeiten auf einem unbekannten Gerät auf das wir häufig nur blinden Zugriff durch eine Schwachstelle in der Weboberfläche bekommen haben, auf einer nur teilweise bekannten Architektur mit nicht funktionsfähigen Tools. Und unter diesen Voraussetzungen werden diese Geräte dann durchaus spannend. Wir beschäftigen uns dann sehr schnell damit unterschiedliche Arten von Firmware Updates zu extrahieren, die Informationen aus den vom Hersteller zur Verfügung gestellten Quellen zu verstehen, Toolchains zu bauen und Zugriff zu diesen Geräten zu erlangen. Spätestens beim letzten Punkt müssen wir das Gerät öffnen und sind mitten im Hardware Hacking angelangt, womit wir von der Webapplikation bis zur Hardware alles in einem Gerät für wenige Euros angreifen können. Das klingt doch nach Spaß ...
Dieser Talk zeigt einen Überblick erkannter und veröffentlichter (http://www.s3cur1ty.de/taxonomy/term/218) Schwachstellen und unterschiedliche Ansätze und Wege wie ein weiterführender Angriff eingeleitet werden kann. Zudem wird dargestellt wie Hersteller solcher Geräte mit entsprechenden Schwachstellenreports umgehen und mit dem Ermittler der Schwachstelle zusammenarbeiten.
Redner: m-1-k-3
EventID: 5030
Event: SIGINT 2013 des Chaos Computer Club [CCC]
Ort: KOMED; Im Mediapark 7; 50670 Koeln; Deutschland
Sprache: deutsch
Beginn: 06.07.2013 11:00:00 +02:00
Lizenz: CC-by-nc-sa
LEXAR 8GB - SIGIN13
How to wiretap the Cloud without anybody noticing [SIGINT13]
lecture: How to wiretap the Cloud without anybody noticing
The US Foreign Intelligence Surveillance Amendment Act and implications for the new DP Regulation
Whatever happens next in the reform of EU Data Protection law, many Europeans will have little practical alternative to using US Cloud services, and businesses and governments will also be sending personal data into US Clouds without individuals' consent. The talk will explain why all data sent into Clouds outside Europe is at risk of purely political mass-surveillance, and that the EU Commission and many Data Protection Authorities know this but turn a blind-eye, and a law that is much worse than the notorious PATRIOT Act (if you are not American) but few people have ever heard of.
Transfers of personal data of EU citizens to Cloud processing providers (like Microsoft Office365/Azure, Google Apps, Amazon etc.) falling under US jurisdiction are commonly supposed to be protected from unlawful surveillance by the legal structures of EU Data Protection.
Speaker: Caspar Bowden
EventID: 5088
Event: SIGINT 2013 by the Chaos Computer Club [CCC] Cologne
Location: KOMED; Im Mediapark 7; 50670 Cologne; Germany
Language: english
Begin: 07.07.2013 15:00:00 +02:00
Lizenz: CC-by-nc-sa
LEXAR 8GB - SIGIN13
The Politics of Surveillance: Understanding the National Security Agency [SIGINT13]
ecture: The Politics of Surveillance: Understanding the National Security Agency
For years, the Electronic Frontier Foundation has been fighting against secret dragnet surveillance by the United States' National Security Agency. This talk reviews what we know about the NSA's spying programs and discusses the path forward to stopping reining in the spying -- from the courtroom to Washington DC. We'll talk specifically about the grassroots tactics that activists are using and the challenges we face.
Speaker: Rainey Reitman
EventID: 5125
Event: SIGINT 2013 by the Chaos Computer Club [CCC] Cologne
Location: KOMED; Im Mediapark 7; 50670 Cologne; Germany
Language: english
Begin: 05.07.2013 21:00:00 +02:00
Lizenz: CC-by-nc-sa
LEXAR 8GB - trnn
the Real news - Reality Asserts Itself
Pt.1: Hedges and Binney on Obama NSA guidelines
Chris Hedges and NSA whistle-blower William Binney tell Paul Jay that there should be accountability, including the President himself, for the criminal practices used by the NSA against the American people - January 10, 2014
Pt.2: Hedges and Binney on NSA Policy
Chris Hedges and William Binney answer the question: "What should the NSA policy look like?" - January 11, 2014
LEXAR 8GB - DemocracyNow
1 National Security Agency Whistleblower William Binney on Growing State Surveillance
In his first television interview since he resigned from the National Security Agency over its domestic surveillance program, William Binney discusses the NSA's massive power to spy on Americans and why the FBI raided his home after he became a whistleblower. Binney was a key source for investigative journalist James Bamford's recent exposé (Cache) in Wired Magazine about how the NSA is quietly building the largest spy center in the country in Bluffdale, Utah. The Utah spy center will contain near- bottomless databases to store all forms of communication collected by the agency, including private emails, cellphone calls, Google searches and other personal data. Binney served in the NSA for over 30 years, including a time as technical director of the NSA's World Geopolitical and Military Analysis Reporting Group. Since retiring from the NSA in 2001, he has warned that the NSA's data-mining program has become so vast that it could "create an Orwellian state". Today marks the first time Binney has spoken on national television about NSA surveillance.
In part two of our national broadcast exclusive on the growing domestic surveillance state, we speak with National Security Agency whistleblower William Binney and two targeted Americans: Oscar-nominated filmmaker Laura Poitras and hacker Jacob Appelbaum, who has volunteered for WikiLeaks and now works with Tor Project, a nonprofit organization that teaches about internet security. Binney left the NSA after the 9/11 attacks over his concerns about the agency's widespread surveillance of U.S. citizens. He describes how the FBI later raided his home and held him at gunpoint and notes there is still no effective way of monitoring how and what information the NSA is gathering on U.S. citizens and how that data is being used.
These interviews are parts of a 5-part special on state surveillance.
- National Security Agency Whistleblower William Binney on Growing State Surveillance
- Detained in the U.S.: Filmmaker Laura Poitras Held, Questioned Some 40 Times at U.S. Airports,
- We Don't Live in a Free Country - Jacob Appelbaum on Being Target of Widespread Gov't Surveillance,
- Whistleblower: The NSA Is Lying - U.S. Government Has Copies of Most of Your Emails,
- More Secrets on Growing State Surveillance: Exclusive with NSA Whistleblower, Targeted Hacker.
William Binney: Interview, April 20, 2012
LEXAR 16GB - 30c3s
Backdoors, Government Hacking and the Next Crypto Wars
Christopher Soghoian (ACLU)
30th Chaos Communication Congress (30C3) #5478, Hamburg, 22:00 Uhr, 29. Dezember 2013
Law enforcement agencies claim they are "going dark". Encryption technologies have finally been deployed by software companies, and critically, enabled by default, such that emails are flowing over HTTPS, and disk encryption is now frequently used. Friendly telcos, who were once a one-stop-shop for surveillance can no longer meet the needs of our government. What are the FBI and other law enforcement agencies doing to preserve their spying capabilities? The FBI is rallying political support in Washington, DC for legislation that will give it the ability to fine Internet companies unwilling to build surveillance backdoors into their products. Even without such legislation, the US government has started to wage war against companies that offer secure communications services to their users. As the FBI's top lawyer said in 2010, "[Companies] can promise strong encryption. They just need to figure out how they can provide us plain text." At the same time, law enforcement agencies in the United States and elsewhere are acquiring the tools to hack into the computers of their own citizens. The FBI has purchased custom-built software, while other law enforcement agencies in the US and elsewhere use off-the-shelf spyware from companies like Gamma and Hacking Team. Regardless of the software they use, the capabilities are generally similar: They can enable a computer's webcam and microphone; collect real-time location data; and copy emails, web browsing records, and other documents.
Speaker: Christopher Soghoian
EventID: 5478
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 21:45:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 30c3
To Protect And Infect, Part 2 - The Militarization of the Internet
Jacob Appelbaum
30th Chaos Communication Congress (30C3), #5439, Hamburg, 11:30 Uhr, 30. Dezember 2013
2013 will be remembered as the year that the Internet lost its innocence for nearly everyone as light was shed on the widespread use of dragnet surveillance by the NSA and intelligence agencies globally. With the uprisings of the Arab Spring where people raided the offices of their regimes to bring evidence to light, we've seen a tremendous phenomenon: a large numbers of whistleblowers have taken action to inform the public about important details. The WikiLeaks SpyFiles series also shows us important details to corroborate these claims. There is ample evidence about the use and abuses of a multi-billion dollar industry that have now come to light. This evidence includes increasing use of targeted attacks to establish even more invasive control over corporate, government or other so-called legitimate targets.
Everything transiting our network connections is under surveillance to some degree. It's also common for law enforcement and intelligence agencies to use exploits and malware to infect and monitor computers, mobile devices and to spy on networks. They're able to bug our rooms with our own telephones, read encrypted emails, log keystrokes - they invade the most personal spaces in the very core of a person's life with minimal economic impact to their budget. In this talk we'll discuss the nature of targeted and untargeted surveillance, exploitation and intelligence gathering. This active surveillance is produced and operated not only by governments but by corporations and mercenaries that provide their intrusion services to the highest bidders who often have the lowest respect for human rights. We'll introduce you to the players in the business of active, passive, tactical and strategic surveillance and the products they provide. We'll also discuss examples of specific attacks on journalists and human rights activists worldwide in the last couple of years. Surprises won't be missing.
Speaker: Claudio Guarnieri Morgan Marquis-Boire
EventID: 5439
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 21:05:00 +01:00
Lizenz: CC-by
Neue Dokumente: Der geheime Werkzeugkasten der NSA
Jacob Appelbaum, Judith Horchert, Ole Reißmann, Marcel Rosenbach, Jörg Schindler und Christian Stöcker
"Die NSA hat eine geheime Abteilung, die Spezialausrüstung herstellt: Spähsoftware für Rechner und Handys, Mobilfunk-Horchposten, manipulierte USB-Stecker und unsichtbare Wanzen. Hier sehen Sie Auszüge aus dem hausinternen Bestellkatalog der Abteilung ANT - Preise inklusive.
Jacob Appelbaum: Art as Evidence - Keynote, transmediale 2014, Berlin
LEXAR 16GB - 30c3s
Der tiefe Staat
Andreas Lehner
30th Chaos Communication Congress (30C3), #5415, Hamburg, 12:45 Uhr, 27. Dezember 2013
In diesem Vortrag soll das Konzept des tiefen Staates anhand der bundesrepublikanischen Geschichte aufgezeigt werden. Rechtliche Aspekte kommen ebenso zur Sprache wie der hohe Grad der Militarisierung und das Ausmaß der Überwachung. Auch die historischen Konflikte zwischen paranoidem Rechtskonservatismus und bürgerlichem Widerstand finden Erwähnung. Ein Ausblick soll die Debatte über die Zukunft des tiefen Staates nach draussen tragen.
Vortragszeitpunkt 32:50: "Was passiert, wenn wir eine Personengruppe haben, die demokratisch legitimiert eine Veränderung herbeiführen möchte, die aber bereits im Vorfeld in einem Maß ausgeforscht wird, dass sich diese staatlichen Strukturen gegen sie wenden können. ... Ich würde gern in den Dialog mit Euch eintreten, und mit Euch herausfinden, wie Eure Sicht ist auf diese Infrastrukturen. Denn wir haben diesen Umbau vor uns, das wird kommen, das ist das, was die aktuelle Regierung tun wird als Argument zur Beschwichtigung der Bevölkerung gegen die Überwachung aus dem Ausland. D.h. wir werden irgendeine Form von Konzentration von Datenverkehr im Inland haben, wir werden weniger Austauschpunkte haben, wir werden bei der Gelegenheit vermutlich eine Harmonisierung der dort vorhandenen Komponenten haben. Das Konzept in den USA "Buy American" führt schon dazu, dass keine ...-Router mehr gekauft werden. Ich weiß nicht, wie der Stand dazu gerade in der Bundesrepublik ist. Damit haben wir weniger Austauschpunkte, weniger Abhörpunkte, an denen aber konzentriert Daten anfallen, und weniger Umgehungsmöglichkeiten. Die Frage ist, was rettet uns aus diesem Konzept, um diesen Raum der Freiheit zu behalten. Das Bundesverfassungsgericht hat in ständiger Rechtsrechung erklärt: Es braucht einen unbeobachteten Raum, in dem die Information, die Entscheidungsfindung und Willensbildung des Bürgers stattfinden kann, der nicht überwacht werden darf, da die Überwachung eine Verhaltensveränderung vornimmt, bzw. das Gefühl der Überwachung."
Andreas Lehner: "Wir finden es erfreulich, dass die Richter die Gelegenheit genutzt haben, um eine sehr grundsätzliche Aussage zu treffen. Durch das neue Grundrecht auf Gewährleistung der Vertraulichkeit und Integrität informationstechnischer Systeme wird ein Schutzbereich für die private Lebensführung im digitalen Zeitalter geschaffen." Quelle: "Ein erfreulicher Richterspruch"
Redner: Andreas Lehner
EventID: 5415
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Fr. 27.12.2013 12:45:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Concepts for global TSCM: getting out of surveillance state mode
Andy
30th Chaos Communication Congress (30C3), #5495, Hamburg, 16:00 Uhr, 30. Dezember 2013
After studying the various levels of activities that come together in BuggedPlanet and realizing the scope and level of implementation of NSA's SIGINT theatre, it's propably time to step back, summarize the big picture and ask how to handle it properly.
This talk will be structured in three parts (Source):
- Part 1: Technical Abilities & Affected Areas
- Technologies of surveillance,
- telecommunication interception and SIGINT,
- cryptoanalytics, cryptocircumvention and what areas of data processing must be considered practically targeted and compromized.
- Part 2: What this means for governments, societies, citizens.
- How the theory of democratic governments, human rights, justice and legal frameworks are being affected by the interception and
- how this practically affects the processes of governments and its players.
- Here I will give examples which SIGINT material is used in the form of Kompromat and Intelligence Operations to influence decisions and decision makers from various countries and continents to show
- the principles and methods and
- how this impacts governmental and other businesses.
- Part 3: Concepts for global TSCM (Technical Surveillance Counter Measures)
- What are the necessary steps to "de-bug" our countries and
- how to immunize against intelligence propaganda in order to achieve data protection.
- This part shall be a framework showing some ideas and principles to act, as well as necessary relationships to understand. The idea is to invite the audience to participate in this part and come up with ideas to create a broader concept and agree on the next steps.
Speaker: andy
EventID: 5495
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Mon, 12/30/2013 16:00:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 30c3
Through a PRISM, Darkly: Everything we know about NSA Spying.
Kurt Opsahl, Senior Staff Attorney, Electronic Frontier Foundation,
30th Chaos Communication Congress (30C3), #5255, Hamburg, 14:00 Uhr, 30. Dezember 2013
From Stellar Wind to PRISM, Boundless Informant to EvilOlive, the NSA spying programs are shrouded in secrecy and rubber-stamped by secret opinions from a court that meets in a Faraday cage. The Electronic Frontier Foundation's Kurt Opsahl explains the known facts about how the programs operate and the laws and regulations the U.S. government asserts allows the NSA to spy on you.
The Electronic Frontier Foundation, a non-profit civil society organization, has been litigating against the NSA spying program for the better part of a decade. EFF has collected and reviewed dozens of documents, from the original NY Times stories in 2005 and the first AT&T whistleblower in 2006, through the latest documents released in the Guardian or obtained through EFF's Freedom of Information (government transparency) litigation.
EFF attorney Kurt Opsahl's lecture describes
- how the NSA spying program works,
- the underlying technologies,
- the targeting procedures (how they decide who to focus on),
- the minimization procedures (how they decide which information to discard),
and help you make sense of the many code names and acronyms in the news. He will also discuss the legal and policy ramifications that have become part of the public debate following the recent disclosures, and what you can do about it.
After summarizing the programs, technologies, and legal/policy framework in the lecture, the audience asked questions.
Speaker: Kurt Opsahl
EventID: 5255
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Mon, 12/30/2013 14:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Bullshit Made in Germany
Linus Neumann, 30th Chaos Communication Congress (30C3) #5210, Hamburg, 20:30 Uhr, 28. Dezember 2013
De-Mail ist ein unverschlüsseltes System, findet nur wenige Anbieter und darüber wird nur sensible Kommunikation abgewickelt. Mit dem De-Mail-Gesetz wurde es zum Standard gemacht gegenüber einer Reihe von ... evtl. überlegenen Methoden. (Transkript)
"So hosten Sie Ihre De-Mail, E-Mail und Cloud direkt beim BND!
Die technischen Probleme der De-Mail ließen sich juristisch lösen, und auch bei der E-Mail setzen deutsche Provider bald Sicherheitsstandards der Neunziger Jahre um. Auch für "die Cloud" hat das BSI einen feinen Standard parat -- natürlich ohne Verschlüsselung. Wofür bräuchten wir die auch im Schlandnet?
Die mediale Aufmerksamkeit auf die NSA-Leaks nutzen deutsche Unternehmen für PR-Kampagnen, in denen "made in Germany" als Gütesiegel für IT-Sicherheit etabliert werden soll. Aus Security-Perspektive reicht ein kurzer Blick, um zu erkennen, dass die Konzepte meist zumindest fahrlässig unsicher, wenn nicht sogar absichtliche Mogelpackungen sind. Im Vortrag werden die Design-Schwächen dargestellt und die Rollen der im Hintergrund wirkenden Behörden und Konzerne beleuchtet. [Logo: CC-BY-SA MathiasM ]
Quelle
Redner: Linus Neumann
EventID: 5210
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Sa. 28.12.2013 20:30:00 +01:00
Lizenz: CC-by"
Glenn Greenwald, Keynote Address, 27.12.13 [30C3]
LEXAR 16GB - 30c3s
Der Kampf um Netzneutralität - Wer kontrolliert das Netz? [30C3]
Markus Beckedahl, Thomas Lohninger
Seit Jahren nur in Fachzirkeln diskutiert gab es 2013 den Durchbruch für die Debatte um Netzneutralität. Mit der Ankündigung der Deutschen Telekom im Frühjahr, zukünftig auf Volumentarife umzusteigen und Partnerdienste priorisiert durchzulassen, wurde Netzneutralität eines der meistdiskutierten netzpolitischen Debatten des Jahres.
Auf nationaler Ebene startete das Bundeswirtschaftsminsiterium eine Diskussion über eine Verordnung und auf EU-Ebene legte die Kommission einen Verordnungsvorschlag vor. Worum geht es in dieser Debatte, und wer sind die Stakeholder mit welchen Interessen? Was sind die Argumentationen, und wie sehen die konkreten politischen Prozesse auf nationaler und EU-Ebene dazu aus? Wie geht die Debatte weiter und was kann man selbst tun?
Redner: Markus Beckedahl Thomas Lohninger
EventID: 5348
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Fr. 27.12.2013 21:45:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
How to Build a Mind - Artificial Intelligence Reloaded [30c3]
Joscha Bach
A foray into the present, future and ideas of Artificial Intelligence. Are we going to build (beyond) human-level artificial intelligence one day? Very likely. When? Nobody knows, because the specs are not fully done yet. But let me give you some of those we already know, just to get you started.
While large factions within the philosophy of mind still seem to struggle over the relationship between mind, world, meaning, intentionality, subjectivity, phenomenal experience, personhood and autonomy, Artificial Intelligence (AI) offers a clear and concise set of answers to these basic questions, as well as avenues of pursuing their eventual understanding. In the view of AI, minds are computational machines, whereby computationalism is best understood as the most contemporary version of the mechanist world view. In the lecture, I will briefly address some of the basic ideas that will underlie a unified computational model of the mind, and especially focus on a computational understanding of motivation and autonomy, representation and grounding, associative thinking, reason and creativity.
Speaker: Joscha Bach
EventID: 5526
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 16:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Keine Anhaltspunkte für flächendeckende Überwachung [30c3]
Martin Haase, maha khamacher
Die Diskussion um NSA, PRISM, Tempora sprachlich und logisch aufgearbeitet
Die Enthüllungen Edward Snowdens haben die deutsche Politik für kurze Zeit in Aufregung gebracht. Für eine Beruhigung reichte es bereits aus, die Enthüllungen in sprachlich-logisch cleverer Weise zu verarbeiten, sie teilweise in ein anderen Kontext zu stellen und so schließlich Entwarnung geben zu können: Die Bundesregierung hat "keine Anhaltspunkte für flächendeckende Überwachung".
Bei diesem Vorgehen handelt sich um ein Paradebeispiel dafür, wie mit einfachen sprachlich-rhetorischen Tricks die politisch Verantwortlichen die Öffentlichkeit und sich selbst so weit täuschten, dass es ihnen nicht mehr nötig erschien, sich mit den eigentlichen Problemen auseinanderzusetzen, und so das leidige Thema aus dem Wahlkampf herausgehalten werden konnte. Neben den mittlerweile zum Standard gehörenden "Basta"-Floskeln spielte das Phänomen der Modalisierung eine besondere Rolle, wie die genauere Analyse zeigt. Auch logische Fehler wie Zirkelschlüssel und (zu) strikte Einschränkung des thematischen Bezugs erlaubten diese "Flucht-nach-vorne"-Strategie. Die Häufung sprachlicher Tricks und des logisch-inhaltlichen Ausweichens legen eine Inszenierung nahe. Die im Bundestag vertretenen Parteien äußerten sich alle zu den Snowden-Enthüllungen. Erwartungsgemäß griff die Opposition die Regierung scharf an, während die Regierung sehr schnell dabei war abzuwiegeln -- zunächst eher ungeschickt. Dann trat eine überraschende Wende ein: Plötzlich waren sich alle einig, dass die NSA-Affäre vorbei sei. Selbst die Opposition beruhigte sich, die zunächst davon gesprochen hatte, Merkel habe ihren Amtseid gebrochen. Interessant ist, dass die Wende vor allem sprachlich vollzogen wurde, wie sich an den Äußerungen sehr schön zeigen lässt. Vor allem die Verwendung auffälliger Adverbien, von Zirkelschlüssen und die teilweise drastische Einschränkung der Bezüge sind entlarvend. Zu Wort kommen neben Angela Merkel, Ronald Pofalla, Thomas Oppermann und andere Protagonisten dieser besonderen Art von Imagepolitik.
Redner: Martin Haase/maha khamacher (neusprech.org)
EventID: 5281
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Fr. 27.12.2013 14:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Kryptographie nach Snowden [30C3]
Was tun nach der mittelmäßigen Kryptographie-Apokalypse?
Die Verwendung von mittelmäßiger Kryptographie scheint gegen Angreifer mit Milliarden-Etat komplett versagt zu haben. Namentlich RC4, MD5 und SHA1 scheinen praxisrelevant brechbar.
Der Vortrag beschreibt die aktuelle Bedrohungslage, gibt praktische Ratschläge für sichere Kryptographie und wagt einen Ausblick auf zwei kommende Kryptodesaster insbesondere im Bereiche "Trusted Computing".
Redner: ruedi
EventID: 5337
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: 27.12.2013 17:15:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 30c3
Nerds in the news [30c3]
Spending a year coding in a newsroom
Friedrich Lindenberg
Knight-Mozilla OpenNews sends coders into news organisations on a ten-month fellowship to make new tools for reporting and measuring the news. We believe that to remain relevant, journalism has to smarten up about tech and data. As a global community, we develop tools to datamine public data, news apps to make information accessible, and visualisations to break down complex stories. In my talk, I want to present the lessons about tech that I've learned in a newsroom and the things that still need to be built.
The internet is destroying the business of news. Not only does the web make it harder to sell advertising on dead trees, it also changes what it means to investigate and tell a good news story. Scoops aren't just researched on the phone anymore, but in scraped databases or leaked data dumps. Yet most journalists are missing the skills to access such information effectively. This means two things: we need training for journos and collaborations between hacks and hackers. Some news organisations are waking up to this fact: the New York Times has an interactive team that employs some of the best web developers, and the non-profit ProPublica has its own nerd team working as data-driven reporters. Working in a news organisation requires coders to change the way they do things and to focus on telling a good story, rather than building a beautiful application. After coding on open data applications for a few years, I applied to join OpenNews and to try and build data-driven news applications from inside a news organisation. After a year at Spiegel Online and visiting news orgs around the world, I've explored not just the weird space of online news, but also the kinds of systems that we need to build to enable journalists to run their investigations deeper, and to keep track of the knowledge they collect.
Speaker: Friedrich Lindenberg
EventID: 5494
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 16:45:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 30c3
The Internet (Doesn't) Need Another Security Guide [30c3]
Creating Internet Privacy and Security Resources That Don't Suck
evacide
As Internet privacy/security professionals and amateur enthusiasts, we are often asked to give advice about best practices in this field. Sometimes this takes the form of one-on-one advice to our friends, sometimes it's training a room full of people, and sometimes you may be asked to write a blog post or a brief guide or an entire curriculum. This talk will survey the current Internet privacy guide landscape and discuss the perils and pitfalls of creating this type of resource, using the Electronic Frontier Foundation's Surveillance Self Defense project as a case study.
As a result of the Snowden leaks, we are learning more and more about the capabilities of potential adversaries such as the NSA, GCHQ, and agencies within China, Russia, and Israel with every passing day. With each new revelation, there is greater uncertainty about privacy and security best practices, especially if your threat model includes a state-level adversary. This talk will discuss the following points: What resources already exist? How should best practices change in light of the Snowden leaks? What makes a good security/privacy resource? How did the Electronic Frontier Foundation confront these questions while rewriting their Internet privacy guide?
Speaker: evacide
EventID: 5538
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 20:30:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 30c3
Überwachen und Sprache [30C3]
Joachim Scharloth
Der Vortrag stellt fortgeschrittene linguistische Methoden des politisch motivierten Internetmonitorings vor. Er gibt keine Anleitung, wie man sich der Überwachung wirkungsvoll entziehen kann, denn das ist ohnehin zwecklos.
Nach den Enthüllungen von Edward Snowden träumten nicht wenige Netzaktivisten davon, mit Hilfe eines "Keyword-DDoS" das Überwachungssystem der NSA unbrauchbar machen zu können. Durch das wahllose Einfügen von Wörtern in E-Mails, die beim Monitoring als Indikatoren für relevante Inhalte verwendet werden, sollte das Überwachungssystem des amerikanischen Auslandsgeheimdienstes überlastet werden. Solche Pläne zeigen, dass die Vorstellung verbreitet ist, die Suche nach für die Nachrichtendienste Interessantem funktioniere vorwiegend über eine Schlagwortsuche. Dabei gibt es längst sehr viel mächtigere Methoden aus dem informatischen Information Retrieval und Text Mining, um große Textmengen effizient nach Inhalten zu durchsuchen. Einige davon möchte ich in meinem Vortrag vorstellen. Zunächst werde ich einige grundlegende computerlinguistische Analysekategorien einführen (Kollokationen, n-Gramme, semanitsche Taxonomien etc.) und dann an ausgewählten Beispielen ihre Anwendung zur Identifizierung von Personen, Themen, Ideologien und Überzeugungsgraden illustrieren.
Redner: josch
EventID: 5377
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Fr. 27.12.2013 12:45:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Warum die digitale Revolution des Lernens gescheitert ist [30c3]
Fünf Desillusionen
Jöran Muuß-Merholz
Der digitale Wandel hat uns grandiose Chancen für selbstbestimmtes, kreatives, kollaboratives, kritisches und demokratisches Lernen gebracht. Wir haben sie nicht genutzt.
Am Morgen nach der Erfindung des Internets stand der Erste auf, um die Revolution des Lernens auszurufen. Jahrzehnte später haben wir alles an Technologie, was für die Revolution nötig erschien. Und alle Ziele grandios verfehlt. Die Verheißungen blieben aus. Es kamen elearning anstelle von selbstbestimmtem Lernen, Friss-oder-Stirb-Apps anstelle von (De-)Konstruktionswerkzeugen, multimediale Vokabeltrainer anstelle von grenzenlosen Communities, elitäre Edu-Zirkel anstelle einer Demokratisierung des Lernens. Stattdessen haben wir bunte YouTube-Videos, die das Schulfernsehen der 1970er Jahre kopieren. Wir besuchen den Massen-Onlinekurs statt den Massen-Hörsaal, Google statt die Bibliothek. Mit digitalen Schulbüchern können wir praktisch weniger anfangen als mit den analogen Vorgängern. In das Lexikon kann man inzwischen reinschreiben - macht aber keiner. Graf Zahl heißt jetzt Salman Khan. Mario Sixtus ist unser Jean Pütz. Zeit für Ernüchterung. Oder?
Redner: Jöran Muuß-Merholz
EventID: 5467
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Mo. 30.12.2013 12:45:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
World War II Hackers [30c3]
Stalin's best men, armed with paper and pen
Anja Drephal
The use of encryption to secure sensitive data from unauthorized eyes is as old as human communication itself. Before the relatively new method of computerized encryption software converting data into a format unintelligible to anyone lacking the necessary key for its decryption, for a long time there was pen and paper and the human brain doing quite a bit of work. Up until the 20th century encryption had to be done literally by hand, to then be transmitted in paper form, via telegraphy or radio. In this context, encryption of data has always been of special importance during times of political conflict and war; subsequently, it saw its major developments during those times in history. This talk will examine and explain common hand encryption methods still employed today using the example of one very successful Soviet espionage group operating in Japan in the 1930s and 1940s: the spy ring centered around Richard Sorge, codenamed "Ramsay".
In the summer of 1938, the Japanese Secret Police started to notice mysterious radio transmissions emanating from somewhere in the Tokyo area. These transmissions, consisting of seemingly meaningless groups of digits, seemed to be directed towards the Asian mainland; neither the Secret Police nor the Japanese Communications Ministry and the Communications Bureau of the Governor General of Korea were able to pinpoint the where and from more precisely.
It wasn't until 1941 that Japanese authorities uncovered the full scope and meaning of these messages -- by accident and at first disbelieving what they had unearthed. The seemingly gibberish radio transmissions did indeed emanate from the heart of Tokyo and, as it turned out, were received in Vladivostok and passed on to Moscow, to be presented to Stalin himself. Decrypted, they contained vital information about secret German and Japanese plans, even the date of the German invasion of the Soviet Union.
This information had been gathered by Richard Sorge, a German citizen with a colorful personality who had infiltrated the small German community in Japan under the guise of a journalist and even gained the friendship and trust of the German ambassador, giving him access to any information available inside the embassy of Japan's ally.
In Japan since 1933, Sorge had built a spy ring around a small group of confidantes: a Japanese journalist with connections to powerful Japanese political circles, a French-Yugoslav communist, and a German radio technician, Max Clausen. Clausen's technical knowledge proved vital for the group's success: he was able to build a transmitter and receiver capable of reaching up to 4,000 km from scratch, using parts available in Tokyo shops without raising suspicion. His radio station was fully portable in a large briefcase and assembled in under 10 minutes.
The dispatches transmitted to the Soviet Union by Sorge's group were written in English and then converted into digits using a straddling checkerboard and, to scramble the content even more, a book cipher, using pages from a statistical yearbook as the key. The Japanese authorities were not able to decipher the messages, Sorge's encryption method remained unbroken until Max Clausen explained it himself after his arrest in 1941. The historical importance of Sorge's espionage material remains a controversial issue among historians; some call him the greatest spy of all times, some argue that since Stalin did not trust his information, Sorge had little influence on the outcome of World War II.
Instead of trying to settle this argument, my talk will examine the technical aspects of Sorge's work in Japan: I will describe the DIY radio station used to wirelessly transmit his dispatches over thousands of kilometers and show how these dispatches were manually encrypted using nothing but a pen, paper, and a book -- suggesting that this method is still valid today, offering low-tech ways of concealing information, be it private or politically delicate material.
Speaker: Anja Drephal
EventID: 5474
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Fri, 12/27/2013 21:45:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Against Metadata [30c3]
Twisting time and space to explore the unknown
Robert M Ochshorn
Using case studies of documentary film, Freedom of Information Law document dumps, soundbanks, and a hacker conference, I will demonstrate experiments and results of several years developing open source tools to reorient the idea of documentary around its documents. This is in opposition to a tendancy towards textual and machine-readable metadata, which unduly constrain our wonder, perception, and ability to navigate ambiguous and unknown material.
Snapping a photo captures more than just image data. Information about the camera and its lens, shutter speed and aperture, date and time, &c, have been bundled into the JPEG since the early days of digital photography. By now, that photo is likely to include a GPS trace as well, and as soon as it leaves your camera, computers are hard at work assisting you in identifying and tagging people and places, with auto-completing textual clarity and database precision. Meanwhile NSA spooks try to reassure us that they are only interested in the metadata of our communications--the who and the when, and maybe some keywords. Without denying a power and efficacy to machine-readable metadata, I argue that for humans to navigate and find meaning in unknown and unsorted material, this search will require multi-media tools that immerse us and augment our powers of perception, rather than reduce all navigation to textfields, transcripts, and tags. For temporal media (sound and video), codecs have given us greater and greater instantaneous fidelity, but leave us with few techniques to skim, seek, and survey. Using case studies of documentary film, Freedom of Information Law document dumps, soundbanks, and a hacker conference, I will demonstrate experiments and results of several years developing open source tools to reorient the idea of documentary around its documents.
Speaker: Robert M Ochshorn
EventID: 5453
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sat, 12/28/2013 16:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Amtliche Datenschützer: Kontrolleure oder Papiertiger? [30c3]
Peter Schaar
In dem Vortrag beschäftigt sich der Ex-Bundesdatenschützer mit der Rolle der Datenschutzbeauftragten: Welche Durchsetzungsmöglichkeiten haben sie? Wie ist ihr Verhältnis zur Zivilgesellschaft? Welchen Einfluss können sie auf europäischer und internationaler Ebene ausüben?
Redner: Peter Schaar (Bundesdatenschutzbeauftragter a.D.)
EventID: 5623
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Mo. 30.12.2013 16:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Beyond the Tech: Building Internet Freedom Tools for Real People [30c3]
Michael Brennan
Few hackers will disagree that users are not given enough consideration when building Internet Freedom Tools designed to circumvent censorship and surveillance. But how do we do it? This talk will outline a framework for a user-focused approach to the Development and Impact of Internet Freedom Tools through using ethnography, human-centered design, and the practice of research-based product definition. This talk is intended for developers, researchers, and journalists who seek to understand how better tools can be developed to protect anonymity and provide unfettered access to the Internet.
Internet Freedom Tools (IFTs) are developed to solve the technical challenges of anonymity, privacy, security and information access. Focus on these technical challenges rather than the user of an IFT can lead to overlooking the motivations, needs and usability issues faced by user communities. Further, IFTs may solve a technical challenge for users, and yet fall short when it comes to user experience. There is a disconnect that must be remedied for IFTs and the people who use them to realize their full potential. This talk seeks to provide new insights to developers and users in need of knowledge on how they can better address relevant problems, create appropriate solutions and help users with IFTs. This talk will explain to the audience what tools are available for user-focused design. It will also walk through a framework to guide the development of IFTs that is grounded in ethnographic methods and human-centered design, and how this framework is being used to conduct an IFT user community. This work is currently being conducted by SecondMuse and Radio Free Asia through the Open Technology Fund (www.opentechfund.org). ADDENDUM: But, what is "Ethnography"? What are "User Communities"? Ethnography is defined as the study of culture and human motivation through qualitative research. Ethnographic practices complement usability studies by tapping into needs and motivations of people and users to give the "why" behind certain actions observed solely through conducting usability research. This method includes interviews, observing specific behaviors and understanding the material culture and surrounds of a target group. A community is defined as a group of users that can be defined by geography, culture, shared experiences, or shared challenges. User is defined as someone who is currently utilizing a particular IFTs such as Tor, RedPhone, CryptoCat, and/or other privacy, security, anonymity and access enhancing technologies and methodologies created by developers or users themselves. A user may also be defined as a potential user of such technologies and tools.
Speaker: Michael Brennan
EventID: 5550
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Mon, 12/30/2013 11:30:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Basics of Digital Wireless Communication [30c3]
Introduction to software radio principles
Clemens Hopfer
The aim of this talk is to give an understandable insight into wireless communication, using existing systems as examples on why there are different communication systems for different uses.
Although wireless communication systems, like Wifi, GSM, UMTS, Bluetooth or DECT, are always surrounding us, radio transmission is often seen as "Black Magic". Digital wireless communication systems differ significantly from analog system designs, although actuall transmission is still analog. Digital modulations, coding, filtering etc. enable highly scalable and adaptive wireless systems, making it possible to design quad-band LTE/UMTS/CDMA/GSM radios on a single chip. The talk briefly describes system concepts, modulation and coding basics, along with the challenges of mobile communication systems. This will include the following topics:
- System concepts
- Digital Modulations
- Shannon-Hartley theorem
- Channel coding principles
- Channel Access
- High Frequency basics
- Radio Propagation
Speaker: Clemens Hopfer
EventID: 5527
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Fri, 12/27/2013 17:15:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Chelsea Manning
07KINGSTON JAMAICA: Malaria Update Dispatches from Fort Meade [30c3]
Reporting on the secret trial of Chelsea Manning
Alexa O'Brien
At Fort George "Orwell" Meade, home of the NSA and the US Defense Information School, managing the message of Chelsea Manning's trial was facilitated by a lack of public access to most of the court filings and rulings until 18 months into her legal proceeding.
While Manning disclosed approximately 750,000 documents to WikiLeaks, only 226 documents of those documents were charged against her under the Espionage and Computer Fraud and Abuse Acts. Only now, three months after being convicted to thirty-five years in prison on twenty counts (including seven containing the Espionage Act language), do we know the identity of most of those 226 charged documents. Do you want to know what put Manning away for 35 years? The truth is stranger than fiction.
Speaker: Alexa O'Brien
EventID: 5634
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Fri, 12/27/2013 16:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
CounterStrike - Lawful Interception [30c3]
FX
Lawful Interception is a monitoring access for law enforcement agencies, but also one of the primary data sources of many surveillance programs. (Almost?) every Internet service provider needs to provide LI functionality in its routers. However, LI exposes a larger attack surface to the one being surveilled than any router should. Could this be a mistake?
This short talk will cover the standards, devices and implementation of a mandatory part of our western Internet infrastructure. The central question is whether an overarching interception functionality might actually put national Internet infrastructure at a higher risk of being attacked successfully. The question is approached in this talk from a purely technical point of view, looking at how LI functionality is implemented by a major vendor and what issues arise from that implementation. Routers and other devices may get hurt in the process.
Speaker: FX
EventID: 5304
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 23:15:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
DLF-Diskussion "Braucht die Informatik Hacker?" [30C3]
Diskussion mit Peter Schaar, ehem. Datenschutzbeauftragter der Bundesregierung, Tim Pritlove (@timpritlove), Podcaster und CCC-Mitglied, Professor Dr. Oliver Günther, Präsident der Uni Potsdam & Präsident der Gesellschaft für Informatik
Moderation: Peter Welchering
LEXAR 16GB - 30c3s
DLF-Diskussion "Big Data & Dual Use" [30C3]
Diskussion mit Karl-Heinz Land, Neuland, Professor Rolf Schwartmann, Uni Köln und Jan Gierlig, Sprecher CCC,
Moderation: Peter Welchering
Weitere Interviews, Sendungen, Informationen Podcasts und Videos zum 30c3 finden Sie unter:
LEXAR 16GB - 30c3s
Drohnenkriege - Kriegführung der Zukunft? [30C3]
Norbert Schepers
Die Drohnenkriege sind Ausdruck einer rasanten Entwicklung: vom "Krieg gegen den Terror" nach 9/11 zur Kriegsführung der Zukunft. Einer Zukunft, die gelegentlich der Science Fiction der späten Achtziger zu entstammen scheint, in der Roboter die schmutzigen Kriege der Menschen kämpfen und sich schließlich gegen ihre Schöpfer erheben. Letzteres liegt noch längst nicht im Bereich des Möglichen, aber Wege zur Erschaffung autonomer Kampfroboter werden bereits beschritten. Der Vortrag will das Phänomen des Drohnenkrieges politisch einordnen und einen Ausblick versuchen.
Das Original dieses Videos stammt vom CCC-TV, der Mediathek des Chaos Computer Clubs (CCC), siehe http://media.ccc.de/browse/congress/2...
Ankündigung zur Veranstaltung im Konferenz-Wiki, siehe https://events.ccc.de/congress/2013/F...
Dort stehen auch die Slides zum Vortrag als PDF bereit (gegenüber dem Vortrag um die Bildquellen ergänzt), siehe https://events.ccc.de/congress/2013/F...
Norbert Schepers, Kontakt etc. siehe http://norbert.schepers.info
LEXAR 16GB - 30c3s
Drones [30c3]
Piotr Esden-Tempski
Autonomous flying vehicles, where are we and where are we going?
During the last 10 years the technology that was formerly only available to the military, reached the hands of thousands. Researchers, hackers, enthusiasts and hobbyists helped drive the technology further and higher than anyone had imagined just a few years ago. We will recap what the civilian airborne robot community has achieved in the last decade and what the next frontiers are that need to be addressed.
Over the last decade, projects and companies like Paparazzi, Microdrone, AscTec, Mikrokopter, UAVP-NG and others have made small unmanned vehicles (aka. drones) what they are today. Through innovation and hard work, autonomous drones are now affordable and accessible enough that most of us can build one at home. While the companies inspired, the Open-Source projects advanced and shared these multidisciplinary technologies with many engineers and hackers thereby building a collaborative community of innovators from the ground up.
Though many challenges have been overcome, we are only at the very beginning of the private UAV revolution. Consider a comparison with the personal computer, which has evolved in ways that could not be foreseen in the beginning. Those working on this platform need space and time to discover the beneficial possibilities. There are many challenges that we are still facing and they are as exciting and basic as the technology itself.
Let me take you through a brief history of the developments and advances in Open-Source UAV and try to envision what is still in front of us.
LEXAR 16GB - 30c3s
Ecuador and hope for global privacy [30C3]
Jacob Appelbaum
At the conclusion of the Tor presentation at 30C3 in Hamburg, Dec. 27 2013, Jake Appelbaum talks about what gives him hope for the future of global privacy: the power of an organized and militant civil society, fighting for their rights. He uses Ecuador, the FLOK Society project and the people involved with the Minga Tec as a positive example of that.
Links to organizations involved in that effort in Ecuador:
http://floksociety.org/
http://www.usuariosdigitales.org/
http://www.asle.ec/
http://www.apc.org/
LEXAR 16GB - 30c3s
Electronic Bank Robberies [30c3]
Stealing Money from ATMs with Malware
This talk will discuss a case in which criminals compromised and robbed an ATM by infecting it with specially crafted malware. The successful compromise of an ATM can easily result in the loss of several hundred thousand dollars.
Most automated teller machines (ATMs) run regular Windows systems and can be controlled like any other computer. The first public demonstration of an ATM hack was given in 2010 - but how bad is this threat really? It turns out there is a multi-million dollar business behind ATM hacks. This talk reveals how these criminal gangs operate by disclosing information obtained through forensic analysis of a real compromise. In the analyzed case some malware was used to control the hacked machine that was written specifically for the targeted ATM brand. By reverse-engineering this malware, we gained unique insights into the technologies used by the intruders. The malicious features range from balance monitoring over cash-out commands to the wiping of the machine to cover up traces of the attack. They can be accessed through special number codes that are entered directly via the machine's number pad. Hooking techniques and overlay windows are used to display the status of the system on the ATM monitor. We will further discuss that operations of this scale can only be performed by professional crime groups that not only have the technical capabilities to develop such special malware, but also have access to insider information about the design of ATMs and who know how the targeted banks operate.
Speaker: tw sb
EventID: 5476
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Fri, 12/27/2013 16:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Europe, the USA and Identity Ecosystems [30c3]
Christoph Engemann
Talk introducing NSTIC and COM 238, i.e. the current digital identity policy proposals in the USA and European discussing their similarities, differences and possible conflicts.
In the past two years both the US Government as well as the European Commission have declared their intend to create "Identity Ecosystems" and are actively pursuing the creation of regulatory and technical frameworks for digital authentication of their citizens. Both the USA and the European Union expect the implementation of state-recognized digital identities in the coming three to five years. The American initiative is called "National Strategy for Trusted Identities in Cyberspace (NSTIC), its European counterpart "electronic identification and trust services for electronic transactions in the internal market" (COM(2012) 238). Given the scope of these programs, the number of people affected and the fact that identity technologies necessarily have to negotiate conflicting values of individual liberty and social control, it is reasonable to expect that the developments around NSTIC and COM (2012) 238 will become dominant in the debate on the future of the Internet. In my talk I will introduce the basics of the White Houses NSTIC initiative and the European Unions COM(2012) 238, explaining the common traits as well as the conflicting aspects of the electronic identity programs of two of the worlds largest and most influential state entities. I will outline how both programs share the assumption that providing "secure" and "trusted" identities is essential for the future development of the Internet, is necessary to fully realize citizenship status on the Net as well as to foster further economic growth. I will also scrutinize the importance and function of the term "transaction" that is prominent in both NSTIC and COM (2012) 238. Subsequently I will show that NSTIC and COM (2012) 238 differ fundamentally in their view on the role of the state, of the private sector and of civil society in providing and controlling the standards, protocols and infrastructures of digital identities. Here I will outline how the NSTIC employs a neoliberal market rhetoric, declaring that "the Identity Ecosystem should be market- driven" while the European Union follows an etaistic vision of governmental identity provision. In this context I will show the importance of the different approaches between Europe and the USA concerning the relation of existing offline and online identity solutions. The goal of the talk is to raise awareness to the importance of these programs, to enable an understanding of the paradoxes of digital identity provision and its function in both enabling and sustaining statehood and capitalism. The talk will close with a statement locating the differences between the European and the United States approach in the larger conflict on the question of means and legitimacy of intervening and regulating capitalism. Duration 40 mins + 20 min discussion, presentation style will be slides and accompanying talk, discussion afterwards.
Speaker: Christoph Engemann
EventID: 5483
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 11:30:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Fnord News Show 2013 [30c3] mit Frank & Fefe
Der schonungslose Realitätsabgleich mit Birzarrometer-Rekalibrierung [The harsh reality check and recalibration of the bizarre-o-meter]
Im Format einer lockeren Abendshow werden wir die Highlights des Jahres präsentieren, die Meldungen zwischen den Meldungen, die subtilen Sensationen hinter den Schlagzeilen. Kommen Sie, hören Sie, sehen Sie! Lassen Sie sich mitreißen!
Redner: Frank Rieger, Felix von Leitner alias Fefe
EventID: 5490
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Mo. 30.12.2013 00:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Google Glass Hacks [30c3]
Stephen Balaban
Fun and frightening uses of always-on camera enabled wearable computers
A one hour technical lecture that covers everything from machine learning and AI to hardware design and manufacture. Includes demonstrations of applications enabled by an always-on image capturing wearable computer. You'll leave with a clear understanding of the field's status quo, how we got here, and insight into what's around the corner.
Always-on camera enabled wearable computers, like Google Glass and Lambda Hat, enable a variety of slightly creepy, but undeniably useful applications. For the past few months, I've worn a computing device that takes pictures every few seconds. I run facial detection over the image stream, pulling out every face I have seen. Soon, we'll be able to conduct mass facial recognition using this data. Other applications include detecting license plates and automatically uploading them to a public GPS tagged website. This talk will cover the history, state of the art, and future of wearable computing, machine learning, and the privacy implication of this technology.
Speaker: Stephen Balaban
EventID: 5537
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sat, 12/28/2013 12:45:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Hacker Jeopardy 2013 [30c3]
Zahlenraten für Geeks [Number guessing for geeks]
Sec Ray
The Hacker Jeopardy is a quiz show.
The well known reversed quiz format, but of course hacker style. It once was entitled "number guessing for geeks" by a German publisher, which of course is an unfair simplification. It's also guessing of letters and special characters. ;) Three initial rounds will be played, the winners will compete with each other in the final. The event will be in german, we hope to have live translation again.
Speaker: Sec Ray
EventID: 5577
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sat, 12/28/2013 00:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Hardware Attacks, Advanced ARM Exploitation, and Android Hacking [30c3]
Stephen A. Ridley
In this talk (which in part was delivered at Infiltrate 2013 and NoSuchCon 2013) we will discuss our recent research that is being rolled into our Practical ARM Exploitation course (sold out at Blackhat this year and last) on Linux and Android (for embedded applications and mobile devices). We will also demonstrate these techniques and discuss how we were able to discover them using several ARM hardware development platforms that we custom built. Where relevant we will also discuss ARM exploitation as it related to Android as we wrote about in the "Android Hackers Handbook" which we co-authored and will be released in October 2013.
Lastly, we will also discuss some of our most recent related hardware research (to facilitate the above) which will include bus protocol eavesdropping/reverse engineering, demystifying hardware debugging, and surreptitiously obtaining embedded software (firmware) using hardware techniques. We will demonstrate and show the supportive tools used and techniques developed to perform this work and deploy them against Apple MFI iAP devices, and multimedia devices using OEM implemented USB stacks. (Which will briefly include our experiences around starting http://int3.cc where we sell a fully assembled modified version of a hardware USB fuzzer.) Along the way we will inevitably share some of the lessons we also learned while completely designing the hardware (from scratch), writing the firmware, and mobile apps for an embedded security device called Osprey that we hold the patent for and have been publicly about publicly as a hardware vulnerability assessment swiss-army-knife for researchers.
Speaker: Stephen A. Ridley
EventID: 5193
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sat, 12/28/2013 17:15:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Hillbilly Tracking of Low Earth Orbit [30c3]
Repurposing an Inmarsat Dish
Travis Goodspeed
Satellites in Low Earth Orbit have tons of nifty signals, but they move quickly though the sky and are difficult to track with fine accuracy. This lecture describes a remotely operable satellite tracking system that the author built from a Navy-surplus Inmarsat dish in Southern Appalachia.
The entire system is controlled through a Postgres database, fed by various daemons spread across multiple machines. So when I click on a satellite on my laptop or cellphone, it runs "UPDATE target SET name='Voyager 1';" and the motor daemon then begins to track the new target while the prediction daemon maintains accurate estimates of its position in the sky. Additional daemons take spectral prints or software-defined radio recordings of the targeted object for later review.
Speaker: Travis Goodspeed
EventID: 5463
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sat, 12/28/2013 14:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Julian Assange - Sysadmins of the world, unite! [30c3]
a call to resistance
Julian Assange (wikileaks) Jacob Appelbaum (ioerror) Sarah Harrison
Finally, the world is aware of the threat of mass surveillance and control, but we still have a fight on our hands, and that fight is both technical and political. Global democracy is not going to protect itself. There has never been a higher demand for a politically-engaged hackerdom. Jacob Appelbaum and Julian Assange discuss what needs to be done if we are going to win. The first part of this talk will discuss the WHAT? and the WHY?: the historical challenge we face, and how we are called to resistance. We are living in a defining historical moment. In recent years, the network has created an unprecedented capacity for parallel communication and action. This has changed the world. For decades hackers have known of the growth of a surveillance state at the heart of Western democracies. Now, everyone knows, and we are left with a single question, how do we stop this? Hackers, sysadmins, developers and people of a technical persuasion are neither neutral parties nor spectators to this. We built the internet and we keep it running. We live there. We write the code. We manage the networks. Communications hegemony is impossible without the obedience of the people who build and run the system. Our network has become the nervous system of the world.
We must wake up to this. We must realize the power and responsibility we hold for the great structural problems of our time. This year, Edward Snowden showed that we are not powerless. We all face a moral choice whether to collude or to resist. We say, resist! Sysadmins of the world, unite! In the second half of this talk we will discuss the HOW?: the medium term and long term modes of action around which we must organize, if we are to see meaningful resistance against the global counterintelligence state, and meaningful progress towards emancipation.
Speaker: Julian Assange (wikileaks) Jacob Appelbaum (ioerror) Sarah Harrison
EventID: 5397
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 22:45:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Making machines that make [30C3]
rapid prototyping of digital fabrication and instrumentation machines
Nadya Peek
For more information and to download the video visit: http://bit.ly/30C3_info
Playlist 30C3: http://bit.ly/30c3_pl
Making a new control system for a machine is often a slow and tedious task. Maybe you already have a 3 axis stage, and you already know how to move it around. But what if you want to add a camera and use it for position feedback? You'd have to redesign the whole hardware layer. I'll talk about some ways I've built modularity into control systems for machines so that you can quickly iterate on different kinds of machine systems without getting stuck in hardware land forever. This includes connecting synchronized nodes across a network and importing legacy nodes for things like, say, an old pressure box you found in the trash and has rs232 in. Down with gcode! Long live machine control.
My journey into FM-RDS [30c3]
Oona Räisänen
How I discovered mysterious hidden signals on a public radio channel and eventually found out their meaning through hardware hacking, reverse engineering and little cryptanalysis.
....
Speaker: Oona Räisänen
EventID: 5588
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sat, 12/28/2013 16:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
THE DATABASE NATION a.k.a THE STATE OF SURVEILLANCE [30c3]
houndbee
23rd of December 2008 was a sad day in India for civil liberties. On this day, The Indian Parliament passed the "The Information Technology (Amendment) Act" with no debate in the House, which effectively means is that the government of India now has the power to monitor all digital communications in the country without a court order or a warrant. The "world's largest democracy" strongly leaning towards becoming a surveillance state raises many questions and poses severe challenges for free speech and economic justice in India and globally. This talk will map and review the current political, socio-cultural and legal landscape of mass-surveillance, data protection and censorship in India and analyse how it ties in to the global landscape of surveillance and censorship. It will also aim to create a discussion space to investigate the deeper effects of these so called "welfare" projects and how citizen-led movements can drive the state towards stronger data protection and privacy laws.
....
Speaker: houndbee
EventID: 5421
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Mon, 12/30/2013 14:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
The Four Wars - Terror, whistleblowers, drugs, internet [30c3]
Annie Machon
Based on her own experiences as an Intelligence Officer for MI5 (the UK domestic security service) and a whistleblower, Annie Machon will talk about the relationships between the wars on 'terror', drugs, whistleblowers, and the internet, and suggest some ideas about what we can do.
Drawing on her experiences as an MI5 intelligence officer-turned-whistleblower who had to go on the run around Europe, as well as her current work as a writer, commentator, and a Director of Law Enforcement Against Prohibition, Annie will be discussing the four current global wars: on terror, drugs, whistleblowers and the internet, and suggesting ways that we, as concerned citizens, can resist. After World War 2 the peoples of the world, collectively reeling from the violence and barbarity, drew up the Universal Declaration of Human Rights. This is a high water mark in civilisation. Since then, at least in the west, we have enjoyed an unprecedented degree of freedom and prosperity. In the subsequent decades further victories were won around equal rights on issues of race, gender, or sexuality. By the 1990s peace appeared to be breaking out around the world, the Cold War was over, and we all lived in an increasingly connected, globalised village. Or did we.... President Eisenhower coined the phrase "the military-industrial complex". He recognised that conflict was good for business, and this had implications for future security. He was prescient. After the racial war was won in the USA, they announced the "war on drugs" which has disproportionately hit ethnic communities in America; as the Soviet threat receded, so the Islamist threat came to prominence; and as the free flow of information spread over the internet, so the fight-back began with the copyright wars, surveillance, and the crackdown on whistleblowers and organisations such as Wikileaks. We are now facing the "military-security complex" and an unending, if nebulous, war on concepts. What can we do about it?
Speaker: Annie Machon
EventID: 5295
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sun, 12/29/2013 20:30:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
The Tor Network [30c3]
We are living in interesting times
(with Jacob Appelbaum)
Roger Dingledine and Jacob Appelbaum will discuss contemporary Tor Network issues related to censorship, security, privacy and anonymity online.
The last several years have included major cryptographic upgrades in the Tor network, interesting academic papers in attacking the Tor network, major high profile users breaking news about the network itself, discussions about funding, FBI/NSA exploitation of Tor Browser users, botnet related load on the Tor network and other important topics. This talk will clarify many important topics for the Tor community and for the world at large.
Speaker: Jacob arma
EventID: 5423
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Fri, 12/27/2013 20:30:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Seeing the Secret State - Six Landscapes [30c3]
Trevor Paglen
Although people around the world are becoming increasingly aware of the United States' global geography of surveillance, covert action, and other secret programs, much of this landscape is invisible in our everyday lives.
The drone war, for example, seems to happen "somewhere else" while surveillance programs take place among the (largely) invisible infrastructures and digital protocols of the internet and other communications networks. Moreover, the state agencies responsible for secret programs strive to make them as invisible as possible. In this talk, artist Trevor Paglen discusses his work attempting to "see" the various aspects of the secret state. In examples ranging from tracking spy satellites to foraging through the bureaucratic refuse of CIA front companies, Paglen will discuss methods used to identify and exploit structural contradictions in classified programs which render them visible, and comment on the aesthetics and politics of attempting to "see" secrecy.
Speaker: Trevor Paglen
EventID: 5604
Event: 30th Chaos Communication Congress [30c3] by the Chaos Computer Club [CCC]
Location: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Germany
Language: english
Begin: Sat, 12/28/2013 23:00:00 +01:00
Lizenz: CC-by
LEXAR 16GB - 30c3s
Wie wehrt man sich gegen Überwachung [30C3]
Tim Pritlove
CCC für Desinteressierte: Zu Besuch auf dem 30. Chaos Communication Congress #30c3 -
Alle Folgen vom 30c3 als Playlist http://bit.ly/1g0SNGC
Folge 102 mit Podcaster Tim Pritlove, der auf dem CCC die Eröffnungsrede gehalten hat. Worum es beim CCC geht, warum sich auch Nicht-Hacker dafür interessieren sollten und was der Chaos Computer Club überhaupt mit Politik zu tun hat, erklärt Tim.
http://die-sondersendung.de/blog/auth...
Abonniert den Youtube-Kanal. Ihr könnt auch Fan von "Jung & Naiv" auf Facebook werden https://www.facebook.com/jungundnaiv
LEXAR 16GB - 30c3s
Zwischen supersicherer Verschlüsselung und Klartext liegt nur ein falsches Bit [30C3]
Ein Streifzug durch die Fehler in der Kryptografie
qbi
"Lange Schlüssel sind sicherer als kurze."
"RSA und/oder AES sind einfach zu implementieren."
"Für Zufallszahlen reicht es, java.util.Random zu nehmen."
Solche oder ähnliche Aussagen hört man immer mal wieder. Doch was ist da dran? Welche Fehler werden bei der Benutzung und Implementierung von Kryptografie gern gemacht?
Kryptografie vermittelt oft den Eindruck, ein mathematisch abgesichertes Verfahren zu sein. Wenn man den Algorithmus wie im Standard implementiert, kann nichts passieren. In der Praxis zeigt sich, dass kryptografische Produkte leicht kaputt gehen. Wenn das passiert, sind die Schäden extrem. Dabei reichen schon einzelne Bits, die falsch gesetzt sind, oder Spezifika der Architektur. Der Vortrag zeigt einige Fehler bei der Benutzung oder Implementierung von Krypto. Die Beispiele rangieren von einfachen oft gemachten Fehlern bis hin zu exotischen. Es soll euch die Augen öffnen, nicht blind einer Implementierung zu vertrauen. Wie immer gilt: "Use the source, luke." :-)
Redner: qbi
EventID: 5502
Event: 30. Chaos Communication Congress [30c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: So. 29.12.2013 23:00:00 +01:00
Lizenz: CC-by
LEXAR 8GB - 29C3
Trojaner-Blindflug: Spionage-Software von Staats wegen [29c3]
Ulf Bühlmeier, Constanze Kurz
"Wir wissen seit ein paar Jahren, dass der Staat technisch in der Lage ist, die Computer einiger seiner Bürger zu infiltrieren. Aber soll er das auch dürfen? Was hat sich in den letzten Monaten beim Staatstrojaner getan?
Seit der Veröffentlichung der Untersuchungen des CCC zum Staatstrojaner hat sich erneut eine Diskussion um den Einsatz der Spionagesoftware entspannt. Die Quellen-Telekommunikationsüberwachung (Quellen-TKÜ) und die Online-Durchsuchung sind im letzten Jahr Gegenstand von Untersuchungsberichten und parlamentarischen Anfragen gewesen. Deren Ergebnisse wollen wir im Vortrag betrachten. Und wir sparen nicht an Ratschlägen für den zukünftigen Gesetzgeber."
Redner: Constanze Kurz, Ulf Buermeyer
EventID: 5380
Event: 29. Chaos Communication Congress [29c3] des Chaos Computer Club [CCC]
Ort: Congress Centrum Hamburg (CCH); Am Dammtor; Marseiller Straße; 20355 Hamburg; Deutschland
Sprache: deutsch
Beginn: Sat, 29.12.2012 14:00:00 +01:00
Lizenz: CC-by-nc-sa
INTENSO#1 - re:publica 2014
24. netzpolitischer Abend des Digitale Gesellschaft e.V.
Leonhard Dobusch,
Kirsten Fiedler,
Thomas Lohninger,
Volker Tripp,
Alexander Sander
KURZTHESE:
Vor drei Jahren wurde auf der re:publica'11 die Digitale Gesellschaft als Verein für digitale Grundrechte gestartet. Seitdem ist viel passiert.
BESCHREIBUNG:
Am ersten Dienstag im Monat lädt Digitale Gesellschaft immer zum netzpolitischen Abend in Berlin ein, um über aktuelle Kampagnen und Debatten zu diskutieren. Im Mai findet dieser auf der #rp14 statt. DIGIGES-Mitglieder geben einen kurzen Überblick zu aktuellen Initiativen, laufenden Kampagnen und Debatten wie Netzneutralität, Exportkontrollen für Überwachungs- und Zensursoftware, Vorratsdatenspeicherung sowie der Kampf gegen unkontrollierbare Handelsabkommen wie ACTA/CETA/TTIP.
Außerdem feiern wir den 1. Geburtstag unserer Initiative Recht auf Remix mit der Eröffnung eines online Remix.Museums, das die Kulturtechnik Remix auch denjenigen näher bringen soll, die sich über das Netz vor allem im Feuilleton informieren.
INTENSO#1 - re:publica 2014
Sprachpolizeiliche Ermittlungen
Anatol Stefanowitsch,
KURZTHESE:
Wo, wie im Internet, Gruppen mit unterschiedlichen Wertvorstellungen aufeinander prallen, wird nicht nur um Inhalte, sondern auch um Sprachregelungen gekämpft. Diese Kämpfe werden schnell zu Grabenkriegen, weil alle Beteiligten einer Reihe von Fehlschlüssen über die Funktionsweise von Sprache unterliegen.
BESCHREIBUNG:
Im Internet prallen Gruppen mit unterschiedlichen Wertvorstellungen aufeinander, die sich offline nie begegnen würden. Diese Wertvorstellungen beinhalten auch Auffassungen über einen sprachlichen Umgang mit der Welt und miteinander, die (unabhängig von inhaltlichen Differenzen) ein hohes Konfliktpotenzial haben. Wo die einen ein Wort als diskriminierend empfinden, beharren andere darauf, dass es eine völlig neutrale Bezeichnung sei. Wo die einen ein Wort in seiner herkömmlichen Bedeutung verwenden, stellen andere diese Bedeutung als nicht mehr zeitgemäß infrage. Wo die einen sich um alternative Ausdrucksweisen bemühen, sehen andere Denkverbote und Sprachwahnsinn. Die metasprachlichen Grabenkämpfe, die sich an diesen Konflikten entzünden, bleiben oft selbst dort frustrierend und fruchtlos, wo auf beiden Seiten ein Wille zur Verständigung besteht. Das liegt daran, dass beide Seiten einer Reihe von (teilweise gemeinsamen) Fehlschlüssen über die Funktionsweise von Sprache unterliegen, die jeden Fortschritt in der Diskussion blockieren. In meinem Vortrag werde ich die schwerwiegendsten dieser Fehlschlüsse aufdecken und eine Grundlage für einen progressiven Umgang mit sprachlichen Entwicklungen und Fehlentwicklungen legen.
INTENSO#1 - re:publica 2014
Das Digitale Quartett analog und live on stage
Ulrike Langer, Richard Gutjahr, Thomas Knüwer, Daniel Fiene,
KURZTHESE:
Das Internet kann mehr als langweilige Talkrunden für ein Massenpublikum. Oder wie Zeit Online schreibt: "Seit einiger Zeit wächst im Internet eine Form der Graswurzel-Talkkultur heran, die weder illustre Gäste benötigt, noch fernsehtaugliche Themen bedienen muss." Seit September 2012 beweist das Digitale Quartett mit relevanten Gästen und spannenden Themen für ein interessiertes Nischenpublikum, dass diese These stimmt.
BESCHREIBUNG:
Was eint Gunter Dueck und Dorothee Bär? Marcel Jansen und Nicole Simon? Jeff Jarvis und Julia Probst? Sie alle waren schon zu Gast im Digitalen Quartett. Die wöchentliche Talkrunde ist nach mehr 50 Folgen mittlerweile zu einer eine Instanz im Netz geworden. Im Digitalen Quartett geht es nicht nur um Netzpolitik und Nerdkram, sondern um alle Bereiche der Gesellschaft, die von der Digitalisierung erfasst werden. Die CSU macht Wahlkampf im Netz, digitale Nomaden leben und arbeiten im Netz, über das Netz werden Autos, Wohnungen oder Werkzeuge getauscht und gemeinsam genutzt, Bücher werden kollaborativ im Netz geschrieben, der "Tatort" macht mehr Spaß mit Twitter, Netzkampagnen finanzieren Hilfsprojekte und Gadgets, Heizungsthermostaten und Autoradios übermitteln Daten an Google und die NSA überwacht nicht nur Merkels Handy, sondern sogar "Angry Birds" Spieler. Kurzum: Neuland ist immer und überall und betrifft jeden. Und darüber wird geredet, montags um 21 Uhr per Hangout on Air.
Das Digitale Quartett - das sind Franziska Bluhm, Daniel Fiene, Richard Gutjahr, Thomas Knüwer und Ulrike Langer. Wir diskutieren nicht nur mit geladenen Gästen, sondern auch mit unseren Zuschauern, die sich jeweils live per Twitter unter dem Hashtag #Quartett in die Diskussion einschalten können. Und ab zu verlassen wir sogar das Netz und gehen auf die Bühne. Nach dem erfolgreichen Einstand bei der #rp13 wollen wir auch in diesem Jahr live von der #rp14 ins Netz senden. Seid gespannt auf Überraschungsgäste, analoge und digitale Tweets und aktuelle Themen.
INTENSO#1 - re:publica 2014
Data in international development: how even the best of intentions can pave the road to surveillance
Zara Rahman, Becky Kazansky
KURZTHESE:
The use of technology in development and humanitarian work is seen as the solution to many of the world's most pressing issues around poverty reduction, allowing international organisations to deliver services efficiently where they are most needed. But increasingly, development projects in the "Information Communication Technology for Development (ICT4D) space may involve the indiscriminate collection of data, which can have all sorts of unintended consequences.
BESCHREIBUNG:
Data is used in international development for all sorts of purposes; to ensure better delivery of aid, to promote transparency and accountability, to ensure that funds are distributed and used in the most effective way possible, with the ultimate aim of alleviating poverty around the world. It's undeniable that the use of this technology has had significant successes; but with data driving development more than ever, to what extent are the privacy rights of vulnerable communities being respected, or even considered?
We'll look at why data is being collected and the current state of privacy rights within development projects, including case studies from Jordan, looking at recent social media activities in Cuba, as well as from the crisis mapping community. We'll consider various actors within the development and humanitarian space; those who are acting with the best interests of their target communities in mind, and those who are prioritising their own interests above those of the communities they are involving.
Ultimately - what are the ways in which data can be used responsibly in the development sphere? Bringing together recommendations and discourse from the open development + privacy community, we'll consider how the two communities can work together to ensure protection of the human rights of the world's most vulnerable communities.
INTENSO#1 - re:publica 2014
Heroes - A Brief History of Whistleblowing.
Elmar Geesen
KURZTHESE:
This lecture will entertain and tell you about whistleblowing people and events we should not forget. The truth needs heroes to be a driver of change. Regarding media coverage, we seem to know everything about whistleblowing. But in fact we don't, the more we leave the well-known paths, we explore a wolrd of thousands of whistleblowers, most of them unknown.
BESCHREIBUNG:
Whistleblowing is an ethical important activity. Together we will make a speedy tour through the last decades, explore known or forgotten events, uncover myths, look into the past and the future of net driven transparency. What we need is rememberance being persistent, to avoid that our heroes getting "heroes just for one day", lost in our daily media and information overload buzz. What can we do to achieve this? This talk is an attempt and starting point to create a place of commemoration, to help and motivate current & future whistleblowers.
I, I can remember
Standing, by the wall
And the guns shot above our heads
And we kissed, as though nothing could fall
And the shame was on the other side
Oh, we can beat them, for ever and ever
Then we could be Heroes. Just for one day?
INTENSO#1 - re:publica 2014
European Parliament: The Zombie Apocalypse
Kirsten Fiedler, McNamee Joe
KURZTHESE:
Over the past five years, the EU faced many challenges concerning digital policy. We successfully stopped ACTA, the CleanIT project, we fought against web blocking and filtering, we advocated for data protection and privacy. Now we must make sure that the proposals which were defeated do not return in a zombie apocalypse.
BESCHREIBUNG:
In Europe and elsewhere, citizens' fundamental are frequently being undermined by governments and corporations: through the disproportionate storage of data by governments and corporations, through access to websites or applications being blocked and through restrictions that are increasingly being implemented on an ad hoc basis by private actors, undermining due process and the rule of law. NGOs and activists had to react to a great number of EU proposals that threatened our rights and freedoms.
This talk will give an overview of what we have been fighting for over the past five years and look at how the upcoming elections can be used as a unique opportunity for action instead of reaction. In order to prevent the zombie apocalypse and the return of bad proposals, EDRi, a network of 36 civil rights organisations, has launched We Promise.
After the next elections, parliamentarians will be confronted with new proposals
- on copyright,
- on civil enforcement of IP rights,
- on criminal enforcement of IP rights,
- on data retention,
- "trade secrets"...
and those are only the ones we know about already! This year's European election is a crucial moment to ensure that digital rights are pushed to the forefront of the political agenda.
INTENSO#1 - re:publica 2014
"Überwachung macht impotent!" - Neue Narrative gegen Überwachung
Friedemann Karig
KURZTHESE:
Was könnte die große wirkmächtige Geschichte sein, die wir gegen Überwachung erzählen müssen, damit die Menschen sich endlich wehren?
BESCHREIBUNG:
Überwachung ist böse, das wissen wir alle, und doch existiert sie: Massenhaft, global, übermächtig. Leider scheinen das die meisten Menschen in diesem Land anders zu sehen - oder ihr Haustier ist ihnen wichtiger. Eine Mehrheit wählt die Parteien, die Überwachung forcieren. Sie dulden und ertragen, was sie nicht verstehen und nicht spüren. Denn sie glauben die Geschichten von Terroristen, die man fangen muss. Sie glauben, dass wer nichts zu verbergen, auch nichts zu befürchten hat.
Es braucht also neue Narrative, gestützt von kraftvollen taktischen Argumenten, um zu überzeugen und zu mobilisieren. Denn sind nur genug Menschen dagegen, reagiert sogar die Politik. Veränderung ist eine Espressokanne: Der Druck muss hoch genug sein. Sonst kommt nichts raus.
Was kann man also aus der Geschichte, aus psychologischer und soziologischer Forschung gegen Überwachung ins Feld führen? Was ist empirisch belegt? Macht Überwachung krank, dumm, impotent? Zerstört sie Gesellschaften, schädigt sie das Rückenmark? Welche narrativen Hebel haben frühere Aktivisten genutzt, um die öffentliche Meinung zu beeinflussen?
Was könnte die große wirkmächtige Geschichte sein, die wir gegen Überwachung erzählen müssen, damit die Menschen sich endlich wehren?
Die Session soll Handreichung für Überwachungsgegner sein, für Aktivisten, Journalisten und Bürger, denen auf "ich habe nichts zu verbergen" und "was schadet es schon?" simple, aber effektive Entgegnungen fehlen. Inklusive einer kleinen Kulturgeschichte des Phänomens Überwachung, ein paar saftigen Horrorstorys von Überwachungsdystopien, den plakativsten Studien, den schlimmsten Negativbeispielen, den noch schlimmeren Zukunftsabschätzungen. Um eine offene Diskussion zu erreichen, welches taktische Argument gegen Überwachung am wirksamsten ist. Welche Geschichte wirkt.
(Die Diskussion läuft schon, siehe bspw. meinen Text und Kommentare "Neue Narrative")
Und nicht zuletzt ist der Vortrag auch sarkastisches Unterhaltungsformat: Mit den besten Überwachungs-Memes, Videoschnipseln, Zitaten und Gags. Denn zusammen über die Bedrohung lachen ist ein erster ziviler Ungehorsam. Aufklärung ist zuerst Aufheiterung. Oder mit Billy Wilder: "If you tell the truth, make them laugh. Or they will kill you."
INTENSO#1 - re:publica 2014
"From ACTA to TTIP - Global trade agreements
Jamie Love
KURZTHESE:
This talk will be about the trade agreements from ACTA to TTIP - but with the wider scope: why are there all these bilateral trade agreements being negotiated now? And what effect do/will they have on access to knowledge.
INTENSO#1 - re:publica 2014
Let's talk about sex baby, let's talk about PGP
Jillian York, Jacob Appelbaum
KURZTHESE:
Using evidence from a stack of historical movements, including safer sex and harm reduction, this talk will address how advocates of liberty and privacy can ensure that their work touches the mainstream.
BESCHREIBUNG:
"I have nothing to hide." "Crypto is hard." These common refrains, as a response to the security and advocacy communities' promotion of anti-surveillance measures, must be acknowledged. The purpose of this session is to address how, as advocates for liberty and privacy - and for the use of encryption as a means to those twin goals - we can learn from successful social movements of our past to bring our efforts to the mainstream. By taking lessons from the safer sex movement, labor movements, harm reduction advocacy and more, we will demonstrate how advocates can bring complex concepts to the general public.
INTENSO#1 - re:publica 2014
Dezentrale Social Networks. Warum sie scheitern und wie es gehen könnte
Michael Seemann
KURZTHESE:
Der Traum von erfolgreichen, dezentralen Social Networks wurde bisher regelmäßig enttäuscht. Ein Blick auf die ökonomische Eigendynamik von Vernetzungsprozessen und die sie beherbergenden Plattformen, zeigt auf warum das so ist. Die Antworten bergen aber ebenfalls einen möglichen Ausweg.
BESCHREIBUNG:
Schon lange - aber vor allem seit den Snowden-Enthüllungen - ist der Ruf nach Dezentralisierung überall zu vernehmen: Wir brauchen dezentrale Infrastruktur und wir dürfen das Netz nicht den wenigen Konzernen überlassen. So richtig diese Forderung auch ist, scheitern die konkreten Projekte mit einer vorhersehbaren Regelmäßigkeit. Dieses Scheitern hat Gründe, die tief in den ökonomischen Gesetzmäßigkeiten von Plattformen und der Eigendynamik von digitaler Vernetzung liegen.
Im Zuge meiner Arbeit an theoretischen Konzepten wie der Ökonomie von Plattformen und der Queryologie (der Lehre von Query), glaube ich, die Hauptgründe des Scheiterns so vieler Projekte wie Diaspora, FreedomBox und status.net verstanden zu haben. Anhand von Google, WhatsApp und anderen Beispielen möchte ich zeigen, wie digitale Vernetzung oft von dezentralen Datenstrukturen aus startet, aber am Ende der Entwicklung doch wieder in zentralistischen Silos landet.
Ich glaube aber auch einen Ausweg aus dem Dilemma aufzeigen zu können, der die wichtigsten Eigenschaften dezentraler Netzwerke (wie den Entzug zentraler Kontrolle der Infrastruktur) auf Dauer bewerkstelligen kann und trotzdem die notwendigen Vernetzungsfeatures bietet, um erfolgreich zu sein. Vor allem kann ich zeigen, auf welche Faktoren zu achten ist, um dem Zentralismus nicht wieder anheim zu fallen.
INTENSO#1 - re:publica 2014
Stimmen der Revolution - Zeitreise durch 200 Jahre Widerstand
Martin Fischer, Cornelis Kater
KURZTHESE:
Historische Überwachung braucht historische Antworten! Wir nehmen Euch mit auf eine Audio-Zeitreise durch 200 Jahre Widerstand gegen staatliche Überwachung. Zitate, Artikel, Reden, Lieder, Gedichte: In einer Mischung aus Vortrag und Hörspiel lassen wir Menschen zu Wort kommen, die sich ohne Netz und doppelten Boden trauten, für Bürger- und Freiheitsrechte einzustehen. Wir möchten Euch Mut machen, indem wir mutige Zeitzeug_innen aus der Geschichte vorstellen.
BESCHREIBUNG:
Ironie der Geschichte: Vor einem Vierteljahrhundert fiel die Mauer und aus dem geteilten Deutschland wurde wurde wieder ein Staat. SED-Diktatur und Stasi-Totalüberwachung der DDR waren ebenso überwunden wie die in Jahre gekommene Bonner Republik. Doch die Feierstimmung des Jubiläums wird getrübt: Noch kein Jahr ist es her, dass Edward Snowden uns eindrucksvoll vor Augen geführt hat, wie es um mühsam erkämpfte Freiheits- und Bürgerrechte mittlerweile bestellt ist.
Aber wir sind nicht machtlos. Kreativer und erfolgreicher Widerstand gegen staatliche Willkür und Eingriffe in den persönlichen Schutzraum war und ist zu allen Zeiten möglich. Auch wenn die Lage schon öfters aussichtslos erschien, möchten wir Euch Mut machen: Unsere Geschichte ist voller Beispiele für das das Aufbegehren von Bürger_innen gegen Zensur und Überwachung.
Wir nehmen Euch mit auf eine Zeitreise und lassen Menschen aus fast 200 Jahren zu Wort kommen. Und das meinen wir ernst!
In einer Mischung aus Vortrag, Hörspiel und Audio-Collage präsentieren wir Zitate, Zeitungsartikel, Reden, Lieder und Gedichte von unterschiedlichen Zeitzeug_innen. Wir sind dicht dran an ihrem Kampf für Bürgerrechte und zeigen dadurch Ihre Aktualität für unsere Zeit auf. Von den Karlsbader Beschlüssen (die bereits 1819 den "Beschluß betreffend die Bestellung einer Centralbehörde zur nähern Untersuchung der in mehreren Bundesstaaten entdeckten revolutionären Umtriebe" beinhalteten), der Revolution 1848, der Zeit der NS-Diktatur bis hin zum geteilten Deutschland und der wiedervereinigten Bundesrepublik geht unser Streifzug. Auf der Bühne ordnen wir das Gehörte zeitlich ein, zeigen Beispiele des Widerstands auf und diskutieren mit Euch über die Implikationen für unsere digitale Gegenwart 2014 nach Snowden. Historische Überwachung braucht historische Antworten!
INTENSO#1 - re:publica 2014
Networking [European] Democracy
Antony Zacharzewski, Karen Melchior
KURZTHESE:
Can you create decentralised, networked democracy in a big government world? At the European level, where there is no single political space, does networked democracy give the opportunity of a networked demos? How should the next European Commission and Parliament do better. Let us make some suggestions.
BESCHREIBUNG:
This workshop will hear about approaches to opening up decision making on three very different levels - the local, the national and the European.
Politics needs to be a network and not just broadcasting. We need all voices to be heard. On a European level the European Parliament can make a difference when the national politicians fail. How do we open up European politics to have an open and inclusive political debate? How to allow voters to be heard and make politicians listen and cooperate. Workshop will discuss suggestions for the new European Commission and Parliament on creating an open democratic debate across Europe for the next 5 years so our voices can be heard.
Anthony Zacharzewski from the Democratic Society in the UK will share experience from two developing projects in England, "NHS Citizen" which is trying to build a citizen participation mechanism for the 50 million users of England's National Health Service, and "Lewes Civic Platform" which is trying to connect local civic activist networks in Sussex on the South Coast.
Karen Melchior, a Danish European Parliamentary candidate will share her campaign experience, and her ideas for building a connected European politics.
INTENSO#1 - re:publica 2014
Black to Grey to Black: Lessons From Two Decades of Online Activism
Parker Higgins
KURZTHESE:
There's no museum of online activism; its history is told as a series of disconnected events. Without perspective, we are left to guess what will work next, while scrambling to recreate elements of earlier successes. What can we learn from two decades of online protests? What has made these campaigns work where so many others have failed? And how can the bloggers, activists, and others at re:publica take these lessons and apply them to the wild web of today-and tomorrow?
BESCHREIBUNG:
There's no museum of online activism; its history is told as a series of disconnected events. Without perspective, we are left to guess what will work next, while scrambling to recreate elements of earlier successes. This talk aims to provide some of that perspective by focusing on three keystone events in the battle for online free speech: 1996's Black World Wide Web protest and the subsequent Blue Ribbon Campaign; 2004's Grey Tuesday to protest censorship by copyright; and 2012's SOPA Blackout protests and ACTA street actions. What can we learn from two decades of online protests? What has made these campaigns work where so many others have failed? And how can the bloggers, activists, and others at re:publica take these lessons and apply them to the wild web of today-and tomorrow?
INTENSO#1 - re:publica 2014
Where Old-World Meets New-Era: Creating Solution Processes for Global Change
Jonathan Henning, Jonathan Imme
KURZTHESE:
Individuals and organizations need smart and sustaibable solution processes to cope with today's global challenges.
BESCHREIBUNG:
Finding innovative yet tenable solutions is imperative in business and in society in general. Solutions can be big and bold leaps forward or small daily steps which move a project or enterprise gradually into the right direction. Now more than ever, profit and nonprofit-actors require sophisticated methods and tools which help them take these steps. They need to make sense of myriad datasets, balance competing priorities, and decide on efficient implementation. Setting-up a sound environment and process for doing so is a big prize but also a huge challenge for them.
In this session, speakers from different fields of business (consulting, app development, and conference organization) and in different kinds of organizations will illustrate how they arrive at solutions in their daily work. In order to give participants a chance to experience the challenges and benefits of different solution processes themselves, we will run a short case study centred on a focal challenge of Global Economic Sympoisum (GES, the session co-organizer) during the hour. The GES is an annual solution-oriented conference. The 2014 GES will take place in Kuala Lumpur on September 6 to 8, 2014.
More information on the conference
INTENSO#1 - re:publica 2014
Automated profiling in law enforcement? What can we know about the actual practice in Germany?
Daniel Guagnin
KURZTHESE:
Profiling technologies have impact on societal norms and practices. A research team at Technische Universität Berlin conducted a case study on the role of profiling technologies in the field of law enforcement and monitoring of political activism. In this talk, first outcomes will be presented.
BESCHREIBUNG:
The Snowden revelations rise questions about which data is used and how it is used by governmental bodies and how this changes societal norms, normativity and judgement. How close did we come in replacing human judgement by data based probabilities calculated by algorithms - which was already feared in the early days of computers?
The Profiling Project (the project is funded by the European Union's Fundamental Rights and Justice Programme) investigates the impact of automated profiling on fundamental rights. Recently the research team at Technische Universität Berlin conducted a case study on the role of profiling technologies in the field of law enforcement and monitoring of political activism.
About 10 long term qualitative interviews with different actors in the realm of political activism have been conducted, such as technology providers, lawyers, legal experts, governmental bodies, activists. The analysis gives insights into the practice of law enforcement activities and shows the range from what can be known about it and what can be assumed regarding the experiences of scrutinized citizen. It thus sheds some light on the factual practices and the impact of new profiling technologies to policing practices in Germany.
INTENSO#1 - re:publica 2014
Just the facts or all the propaganda? Reporting from and about Ukraine
Alena Popova, Oksana Romaniuk
KURZTHESE:
The battle to control the media narrative coming out of Ukraine and Russia has moved online.
BESCHREIBUNG:
"Wahrheit und Verzerrung - Berichterstattung aus und über die Ukraine" Oksana Romaniuk aus der Ukraine und Alyona Popova aus Russland, zwei Jurymitglieder des Deutsche Welle Preises für Online-Aktivismus "The Bobs", diskutieren die mediale Berichterstattung aus und über die Ukraine. Der Kampf um die Meinungshoheit wird längst auch im Netz geführt. Haben die westlichen Medien in ihrer Berichterstattung ein schiefes Bild der Ukraine geliefert? Brauchen wir einen Propagandafilter als Add-on für den Browser?
Presented by The Bob's - Best of Online Activism by Deutsche Welle.
INTENSO#1 - re:publica 2014
Pledge, Turn, Prestige - The Snowden Pitch
Marcus John Henry Brown
KURZTHESE:
Building on his 2013 re:publica talk "I Palindrome I - you life is mine", Marcus takes a look at how Edward Snowden has become one of the most evocative fictional characters of our time. Set in 2008, "The Snowden Pitch" takes the form of a formal presentation in which Marcus presents a narrative and strategic framework to senior members of the NSA and explores how using models such as "Pledge, Turn, Prestige", "Limited Hangout Operations" and "Worked Shoots" the NSA could win the Internet.
BESCHREIBUNG:
"Come in closer because the more you think you see, the easier it'll be to fool you" .Now you see me.
Espionage is like magic. It's full of deception and things happening in other places whilst you're looking somewhere else. Like a good magic trick, good espionage will pull it's audience in, show as many cards as possible and just when the audience thinks it knows what is going on the magician/spy will make something disappear.
"Now you're looking for the secret... but you won't find it, because of course you're not really looking. You don't really want to know. You want to be fooled. But you wouldn't clap yet. Because making something disappear isn't enough; you have to bring it back. That's why every magic trick has a third act, the hardest part, the part we call "The Prestige". The Prestige.
On the last weekend of 2013 Marcus was writing a list of things that had really annoyed him during the past 12 months. At the top of the list was Edward Snowden. Confused as to why this might be, he let his mind wander a little and found himself in a managed solutions office in Munich airport. He found himself in a meeting room with a beamer, notepads and a plate of biscuits.
It was 2008 and he'd been given a brief.
Four middle-aged gentlemen in suits enter the room, hands are shook, the door is locked and coffee is served. The senior man in the room repeats the terms of the meeting and then Marcus is asked to begin.
"The Pledge, The Turn, The Prestige - The Snowden Pitch" is a fictional pitch presentation that approaches the NSA as if it were a client with unlimited budget, an image problem within the espionage community and explores Edward Snowden as the protagonist of the biggest worked shoot the world has ever seen.
The talk explores why the NSA would have done this, what they would have to gain and, more importantly, it considers that which we have not yet seen - The Prestige.
INTENSO#1 - re:publica 2014
Media Freedom Under Pressure - Global Trends and Perspectives
Solana Larsen, Erol Önderoglu, Andrei Soldatov, Sally Broughton Micova
KURZTHESE:
Today freedom of the press and freedom of expression are under serious threat in numerous countries. This threat is present in authoritarian states as well as in democracies generally considered to be well established and stable. Can new online media and much-touted grassroots journalism offer a way out?
BESCHREIBUNG:
In countries all around the world, government surveillance, repression and influence are posing new challenges for the media and civil society. More and more frequently, we are seeing an arms race between journalists, Internet activists and governments, with governments attempting to protect their monopoly on information by monitoring and blocking websites and communication channels through intimidation and condemnation.
Can new online media and much-touted grassroots journalism offer a way out? Or do developments like the restrictions imposed on freedom of expression on the Internet in places like Vietnam and Turkey show that not even the Internet can stop this trend? Why are civil society organizations so active online, especially in countries with underdeveloped Internet infrastructure? And why is media freedom developing so diversely in Eastern Europe, with positive tendencies in Poland and dramatic declines in Hungary?
"Media Freedom Under Pressure - Global Trends and Perspectives" is an opportunity for bloggers, journalists and media experts from various countries to join us in a discussion of these developments. The session is presented by two of the Bertelsmann Foundation's projects: the Sustainable Governance Indicators and the Bertelsmann Transformation Index.
LEXAR_8GB - re:publica 2014
Why should you know who has been asking about you?
Katarzyna Szymielewicz
KURZTHESE:
If you want to know what state knows about you and why so much, then we have something in common. In the post-Snowden world we became well aware that data we store on servers belonging to private companies tends to have a second life. It is where secret services and law enforcement meet the Internet. How to prevent bulk transfers from private to public data bases? How to make sure that due process is in place? What do we know about disclosures of our data and how can we learn more?
BESCHREIBUNG:
Shedding more light on private-public data flows seems to be one objective on which citizens and companies could work together. It is the question of getting the incentives right and reaching some consensus on what "transparency" really means. Do we care more about numbers (i.e. how many times our data was disclosed) or purposes of surveillance? Can we control both? I will suggest answers to these questions on the basis of my own research.
Building on what was triggered by Snowden's revelations and recent research that Panoptykon Foundation carried out in Poland, I will look at:
- What sorts of data we "leave behind" in the Net and what can be inferred from these data sets?
- Who can access this wealth of information and for what purposes?
- How much can we learn about that just by talking to companies?
- What are the problems to be solved and possible solutions?
LEXAR_8GB - re:publica 2014
Lights on the Wild! (Ist das Netzpolitik oder kann das weg?)
Maximilian Hösl, Julia Krüger
KURZTHESE:
Auch wenn die Netzpolitik komplex, grenzenlos oder schwer voraussehbar zu sein scheint: Es lassen sich Muster ihrer Struktur und Entwicklung erkennen, deren Kenntnis für die weitere Gestaltung einer digitalen Gesellschaft nützlich ist.
BESCHREIBUNG:
Die Netzpolitik wächst heran. Zumindest was Themen, Akteure und Institutionen angeht. Bedeutet das eine Entstehung von Ordnung, von Berechenbarkeit und Struktur? Wenn ja, warum gibt es dann beispielsweise noch keine Internetministerin? Wir wollen versuchen, Pfade durchs wilde Dickicht der Politisierung des Netzes zu schlagen.
Begonnen haben wir mit einer Community-Befragung. Wir haben gefragt: Was ist die Geburtsstunde der Netzpolitik? Wie und warum wurde das Netz politisch? Was wir bekommen haben, sind viele Geschichten: von BTX-Hacks, dem Bundespost-Monopol auf Modems, einem Unbehagen mit der Sicherheitspolitik nach 09/11 oder einer zensierenden Ursula von der Leyen.
Im Wildwuchs der Antworten lassen sich Muster erkennen, die wir erklären und zur Diskussion stellen wollen - im Vergleich mit Entwicklungen in Politik und Gesellschaft.
Wir stellen also unterschiedliche Geschichten der Netzpolitik vor - und in einen Zusammenhang - und erklären, was uns diese Geschichten über die Entwicklung und Strukturierung eines Politikfeldes Netzpolitik erzählen können.
LEXAR_8GB - re:publica 2014
Wie ich lernte, die Überwachung zu lieben
Felix Schwenzel
KURZTHESE:
Die fiktionale Figur Andrew (Ender) Wiggins sagt in Orson Scott Cards Buch (und Film) Das große Spiel: "In dem Moment in dem ich meinen Feind verstehe, ihn gut genug verstehe um ihn zu schlagen, in genau diesem Moment liebe ich ihn auch." Hilft uns diese pop-philosophische Erkenntnis möglicherweise den Überwachungsstaat zu schlagen und zu überwinden und wieder mehr Grundrechte garantiert zu bekommen?
BESCHREIBUNG:
Die fiktionale Figur Andrew (Ender) Wiggins sagt in Orson Scott Cards Buch (und Film) Das große Spiel:
In dem Moment, in dem ich meinen Feind verstehe, ihn gut genug verstehe um ihn zu schlagen, in genau diesem Moment liebe ich ihn auch.
Hilft uns diese pop-philosophische Erkenntnis möglicherweise den Überwachungsstaat zu schlagen und zu überwinden und wieder mehr Grundrechte garantiert zu bekommen?
Oder ist die überbordende staatliche Überwachung, die mit Hilfe von Edward Snowden aufgedeckt wurde, nicht einfach nur eine weitere Disruption, die uns die Vernetzung, das Internet gebracht haben? Ist das was Amazon mit dem Buchmarkt, das Internet mit dem stationären Einzelhandel macht, vergleichbar mit dem was die Geheimdienste der Welt mit unserer Privatsphäre anstellen?
Warum heissen wir die Disruption etlicher Wirtschaftszweige durch das Internet willkommen und fordern Veränderung und Anpassung an die neuen Gegebenheiten, weigern uns aber, unser Bild von Privatsphäre an die neuen Gegebenheiten anzupassen?
Anders gefragt, sind wir von glühenden Internet-Fans zu Fortschrittsskeptikern geworden, weil wir uns plötzlich persönlich vom Fortschritt bedroht fühlen - oder ist die Lage wirklich ernst?
LEXAR_8GB - re:publica 2014
The Architecture of Invisible Censorship: How Digital and Meatspace Censorship Differ
Pranesh Prakash
KURZTHESE:
We often believe that the Internet routes around censorship; at the same time we often feel the same rules that should apply to offline speech (e.g., not being removed without a court order, etc.) should apply to online speech as well; we often understand that there are differences between offline and online censorship, but what are the implications of the intermediated digital lives that we lead on how we engage in and combat against censorship? He probes the idea of "invisible censorship" as the dominant mode of modern digital censorship, in a break from previous forms of social, private, or state-directed censorship which were mostly visible and hence challengeable, and presents tentative thoughts on what we do legally, technologically, and socially to uncloak invisible censorship.
INTENSO#1 - re:publica 2014
Mit Sicherheit scheitern: the End of One-Internet
Andreas Schmidt
KURZTHESE:
Eighteen years ago, John Perry Barlow derided the "weary giants of flesh and steel" - today, they control the Internet. The idea of a communicational one-world has been superseded by the giants' power-grabbing approach. This talk discusses different types of possible Internet security institutions, their viability, and their ability to achieve traditional Internet values embedded in open source ideas. The choice between technological cosmopolitanism, a fire brigades-design, an Internet government, informational hegemony, and noospheric empire fundamentally influences which values the Internet can yield.
BESCHREIBUNG:
Security saves it all, breaks it all. A sovereign is she who calls the shot in a crisis. Label any contested policy a security issue, and you'll get a green light for applying whatever it takes. Yet, the design of security and its institutions has only played a minor role in Internet discourses off the beaten track of security circles.
The need for security institutions is apparent: The human species is a "group of persons who can't do without peaceful togetherness and yet can't help but constantly loathe one another". Immanuel Kant, the source of the previous words, thought mankind could achieve its civic norms: it only had to follow the guiding principle of the idea of a cosmopolitan society. Therein, citizens set up, ensure, and enforce their own civic rules. The ensuing 250 years haven't quite followed this model. The cosmopolitan model, the ideals of one-world have failed to sustainably shape world politics. Ideas of perfect global political institutions have been shattered by political realities, then adapted to these political realities, and thereby slowly dismantled from their initial normative impetus. This pattern also applies to the Internet and thinking thereof.
This talk elaborates on different designs of security institutions, among them the fire brigade-approach, an Internet government, technological cosmopolitanism, the evil noosphere empire, and benevolent informational hegemony. These models of security are contrasted with popular ideas and values of Internet fans such as openness, distributiveness, and socialness. In addition, the viability of any model differs substantially given political and economic interests in today's world.
As living on the Internet now has aspects of life in the Truman Show, the question arises whether there is any chance to revert the status quo of the existing landscape of Internet security institutions. Hope springs eternal, but reason tells a new dominant thinking on the Internet and the values it shell foster is on the rise.
--
P.S.: A hint for English speakers regarding the title of this talk. "Mit Sicherheit scheitern" translates as both "failing for sure" and "failing with security".
LEXAR_8GB - re:publica 2014
Networked Consent: Dreaming and Desire in the 21st Century
Laurie Penny
KURZTHESE:
Changes in communications technology allow us to think in new ways about consent, desire and the nature of power. There are important parallels between the backlash against rape culture and innovations in digital politics. What does that mean for the consent of the governed?
BESCHREIBUNG:
This talk is about how the internet is allowing women and queer people to question rape culture and change the conversation about what is 'done to' people and what we'll accept. Voting is a limited form of consent: it allows you to say yes or no, just once, to a contract whose terms you don't get to see until you've signed. Who is speaking back to power? Is it possible to enthusiastically consent to capitalism? Can we create a new formula for 'consent of the governed'? What links liquid democracy with #everydaysexism? All this and more will be hashed out.
LEXAR_8GB - re:publica 2014
Gate keeping, old and new. How freedom of the press is threatened by the companies that themselves depend on it.
Matthias Spielkamp, Jillian York, Alexa O'Brian
KURZTHESE:
Some Internet giants exhibit double standards: They rely on constitutional freedom of speech guarantees (i.e. the First Amendment) as a basis for their business models but at the same time deprive their users of these freedoms. This is especially problematic in cases of journalistic content because of the role journalism has in society - as an essential force in allowing public debate and forming public opinion. Constituting, in short, a society's conversation with itself. We urgently need new models and ideas to resolve this situation.
BESCHREIBUNG:
Amazon cut off Wikileaks when it was asked to do so by a US senator. Apple didn't need anyone to ask them to block an app from their store that sends users a notice whenever a US drone kills someone - it just rejected it as "objectionable and crude". Facebook erased posts critical of the Catholic church by a German talk show host because someone doesn't like what he said, but does not say who it was and for what reason. And Google has never sufficiently corrected its "real name only" policy that either prevents citizen journalists from using the platform altogether or puts them at risk when they do.
Examples that show the Internet giants' double standards: they rely on constitutional freedom of speech guarantees (i.e. the First Amendment) as a basis for their business models but at the same time deprive their users of these freedoms.
This is especially problematic in cases of journalistic content because of the role journalism has in society - as an essential force in allowing public debate and forming public opinion. Constituting, in short, a society's conversation with itself.
At the same time, many publishers have never been shy of using their own publications for their political aims and economic gains. Now some of them are turning into content distribution platforms themselves. So are they living in glass houses, throwing stones?
LEXAR_8GB - re:publica 2014
Crowdsourcing Design: The Good, the Bad and the Ugly
Florian Alexander Schmidt
KURZTHESE:
This talk looks at the ethics and aesthetics of the crowdsourcing industry, its dark side and silver linings, with a focus on the crowdsourcing of design. What distinguishes the crowd design from micro tasking? And is crowdsourcing inherently exploitative or can it be done in a way that is sustainable for all stakeholders?
BESCHREIBUNG:
Crowdsourcing Design: The Good, the Bad and the Ugly Once merely one of these buzzwords, crowdsourcing has developed into a rapidly growing global industry. Today's sweatshops are "in the cloud" and a plethora of crowd based projects reaching from the weird to the worrisome calls for a differentiated analysis and critique.
Crowdsourcing is a very controversial concept, especially because it is now applied to so many fields. The crowd has become the source for a great variety of tasks and the incentives are heterogenous as well. The lack of boundaries between work and play makes it so difficult to evaluate crowdsourcing and it gets particularly tricky when the projects are profit-oriented.
For some, crowdsourcing is "just like Wikipedia, but with everything" - a seemingly utopian idea. However, when the so called wisdom of the crowds turns into precarious crowd-labour, with all risks being outsourced to the workers, it becomes indistinguishable from exploitation. While a large section of the crowdsourcing industry is organised the way that workers get micro-payment for mirco-tasks, the crowdsourcing of design is characteristically organised through contests.
In this model, the platform providers take a forty percent cut upfront from the money paid by external clients while the designers compete, with a chance of one in a hundred, to eventually get paid for the work they have done beforehand. But there are also platforms that try to organise crowdsourcing in a way that is fair for all stakeholders.
weitere re:publica 2014 Vorträge
http://re-publica.de/session/social-engineering-sozialen-netzwerken-angriffsszenarien-und-moeglichkeiten-des-digitalen
http://re-publica.de/session/security-and-privacy-private-cloud-environments
http://re-publica.de/session/alex-pitchcube
http://re-publica.de/session/history-repeating-wenn-nerds-geschichte-schreiben
http://re-publica.de/session/hashtags-politics-europawahl-2014
http://re-publica.de/session/shannon-snowden-human-target-information-theory-beginning-until-today
http://re-publica.de/session/lets-visualize-it-making-sense-globalization-through-data-visualization
http://re-publica.de/session/anmeldepflichtig-could-should-would-urbane-zukunft-und-digitale-moeglichkeitsraeume
http://re-publica.de/session/buchvorstellung-ueberwachtes-netz
http://re-publica.de/session/how-do-we-know-tech-hubs-make-difference-crash-course-evaluation-innovation-ecosystems
http://re-publica.de/session/netzpolitikorg-treffen-redaktion
http://re-publica.de/session/data-dealer-ueberwachung-datenhandel-spiel
http://re-publica.de/session/big-small-open-my-data
http://re-publica.de/session/fighting-prism-distributed-and-federated-net
http://re-publica.de/session/data-gone-wild-frei-darf-datenvisualisierung-sein
http://re-publica.de/session/warum-acta-jugendliche-bewegt-hat-und-prism-kaum-spurensuche
http://re-publica.de/session/o-europa-where-art-thou-quiz-fuer-eu-nerds
http://re-publica.de/session/big-small-open-my-data
http://re-publica.de/session/me-you-and-everyone-we-dont-know-yet-building-diversity-workshop
LEXAR 8GB - Interviews
Ed Murrow: A Conversation with J. Robert Oppenheimer
See It Now - Season 4, Episode 18, 4 Jan. 1955 (on IMDb)
"Work is so hard and failure is -I guess- an unevitable condition of success."
"[The purpose of us -the Princeton Institute of Advanced Study- is] to help men who are creative and deep and active and struggling scholars and scientists, to get the job done that it is their destiny to do. This is a big order, and we take a corner of that, we do the best we can, we suffer from limits of money, of wisdom, of space. And we know if we get big, we will spoil everything, because the kind of intimacy, the kind of understanding, the kind of comradeship that is possible in a place of this size is hard to maintain in a place ten times as big. But we are here as an institution, I don't mean in our individual capacities. And as an institution we are here to take away from them the cares, the pleasures, that are their normal excuse for not following the rugged road of their own life and need and destiny."
LEXAR 8GB - Interviews
/Edelman
Gerald Edelman talks to Basil Gelpke: Simple words and deep meanings
Zeitpunkt: 37 Minuten, 27 Sekunden seit dem Anfang des Videos)
Unser Gehirn funktioniert durch Selektion nach darwinistischem Prinzip, arbeitet also auf einer anderen Basis als die wissenschaftlich-technische Welt.
Technische Systeme versagen, wenn sie in sich widersprüchlich sind. Widersprüche in unserem Bewusstsein dagegen eröffnen uns im besten Fall neue Horizonte. Im schlimmsten Fall sind wir uns ihrer nicht bewusst. Wir sind im Alltag eingebettet in exakte Wissenschaft und Technik und glauben daher, unser Denken könne ebenso fehlerfrei sein.
Nach Gerald Edelman funktioniert unser Gehirns prinzipiell ähnlich wie unser Immunsystem.
Letzteres arbeitet mit einem Netzwerk von Cytokinen, T- und B-Zellen (einfache Beispiele: 1, 2). Der Zustand des Netzwerks wird durch Eindrücke von außen (z.B. Bakterien) verschoben, die Eindrücke werden also im Netzwerk abgebildet. Die Verschiebungen des Netzwerks sind die Bilder, die unser Immunsystem von den Eindrücken hat. Mit ihnen erkennt es beispielsweise, um welches Bakterium es sich handelt, Verschiebung und Bakterium, Eindruck und Wirklichkeit sind fürs Immunsystem das Gleiche.
INTENSO#2 - Gerald Edelman
brain_dynamics_IBM
Gerald Edelman: From Brain Dynamics to Consciousness: A Prelude to the Future of Brain-Based Devices
Lecture 1 of 12 of IBM Research's Almaden Institute Conference on Cognitive Computing, June 2006
brain_dynamics_UCLA
Gerald M. Edelman: From Brain Dynamics to Consciousness: How Matter Becomes Imagination
University of California at Los Angeles, February 2005, viewgraphs invisible
History of Neuroscience
Society for Neuroscience archival interview with American biologist Gerald M. Edelman, March 2004. He successfully constructed a precise model of an antibody, a protein used by the body to neutralise harmful bacteria or viruses, and it was this work that won him the Nobel Prize in Physiology or Medicine in 1972 jointly with Rodney R Porter. He then turned his attention to neuroscience, focusing on neural Darwinism, an influential theory of brain function.
/WebofStories (July 2005)
4.37 The theory of neural Darwinism
In the first place, what is the theory presumed to say? Well, what it presumes to say is to turn the problem on its head and say, instead of being like a Turing machine...
which is what a computer is, a finite state automaton with a program with a tape head that can read or write a zero or a one and then move one step or move in the other direction one step and change its program again, and in fact even expunge a zero and one and replace it, which Turing showed, in fact. If you have an effective, unambiguous algorithmic procedure, you can have a universal Turing machine; you can show mathematically that there is not problem you can't solve except certain ones which he showed were insoluble. So this idea pervaded; I mean, people still in cognitive science consider this the central idea: namely, if that's what you can do with a computer, then why not the brain as a computer?
Well, it turns out, when you look at the actual biology and you go back, and there is a suggestion here to embryogenesis, things happen uniquely. And then you have the problem of... well, that means you have a kind of ambiguous situation, you have mistakes, so-called. Now what do you do with a computer when it makes mistakes? Well, you put in error correcting programs. But when you look at the biology, the number of possible error corrections would become unbelievably large. So this theory, which was called the theory of neuronal group selection or neural Darwinism in honor of the great man, said the following.
That there were three fundamental stages:
the first was the stage in which you lay down the neuroanatomy which was following those kinds of rules I mentioned about in morphogenesis, namely you have cell division, cell motion, cell adhesion, cell death, and... and the interaction amongst different parts, embryonic induction, in which one set of cells influences another by signaling. All of this is true in the nervous system, but you have to remember the nervous system is made of very special kinds of cells which are extremely polar, which have long processes called axons which go from one cell to connect to another through a synapse or connection, and also have other kinds of processes called dendrites which receive that connection from axons. When you look at it, it sort of scares you. The numbers are truly scary. Let me give you a feeling for that.
The cortex of the brain has about 30 billion neurons. It has a million, billion connections. If you count one second... one connection per second you will just finish counting 32 million years later. That's just counting them. If you calculate how many different ways they can connect, it's ten followed by a million zeros. There are ten followed by 83 zeros, give or take, of particles in the known universe. Gives you a lot of respect. So here you have this problem, that in each embryo, when you're making the nervous system and its connections and its neuroanatomy, it's true that these genes we mentioned before, Hox genes and Pax genes, constrain the fact that say it's a human brain rather than a chimp brain. But in very short order the whole process becomes epigenetic; it becomes that neurons that are connected, even at a distance, that fire together will... will influence which neurons wire together. That first step has to necessarily introduce variation. So even though all brains are alike in the way the faces are alike, they're also different in the way faces are different, even in twins.
The second step is related to the first: namely that, even after you have the anatomy, that there is differences in the strengths of the connections. There are differences in the strengths of the connections. So that the influence of particular events on a synapse are such as either weaken it or strengthen it. That's essentially like putting a traffic cop on each of the highway points, to let it go through fast, to let it go through slow, or to stop it completely. And neurons come in two flavors excitatory and inhibitory and all of the things I'm mentioning refer to both. The fact is this second process is occurring right now in our brains and is the basis, in large extent, a necessary basis at least, for things like memory, learning and what have you. So that is the second stage.
So the first stage is what I call developmental selection, where you change amongst the different embryonic processes;
the second stage is experiential selection, because obviously your experience of the input to the various neurons changes which ones fire together and wire together. But neither of those really covers the essential point that you... you're faced with when you give up the idea of a computer. A computer works by logic and a clock. Now I've given up logic and I've given up a clock, and I've said brains don't work that way they work by pattern recognition so what gives you the equivalent of time and space? The answer to that is the hard part of the theory, I'm afraid to say.
(added by J. Gruber)
Logic, space and time are foreign to our consciousness
Our consciousness does not work on logical principles and it does not have a clock. Our brain represents logic and time. They are the result of models our brain forms while we grow up.
Oliver Sacks in Awakenings, pages 339 - 348:
"We may first take a brief historical look at notions of 'space'. An essential difference (one might almost say, the essential difference) between the philosophies of Newton and of Leibniz hinges on their differing notions and uses of the word 'space' - the Newtonian concept of 'motion' versus the Leibnizian one of 'action'.
- For Newton space and time were absolutes - absolute media in which motion occurred; they were not hypotheses (Hypotheses non fingo), or, as we would say now, frames-of-reference.
- For Leibniz, in contrast, 'space' and 'time,' and all such notions of continuity and extension, were simply ways of speaking, ways of picturing and measuring the size of actions: they were concrete and actual, not absolute and abstract, i.e. they were convenient (or conventional) constructions or 'models,' figurative language (albeit of a very special sort). (These essentially relativistic concepts of Leibniz are fully spelled out in his correspondence with Clark - a correspondence interrupted only by Leibniz's death, and not published until many years later.)
The notion of 'space' as a way of speaking and looking at the world, rather than as a Euclidean or Newtonian absolute, was revived by Gauss in his famous papers on the possible curvatures of possible spaces, and then by the great Russian geometers in their 'alternative geometries.' These, then, combined with Maxwellian dynamics, were the intellectual antecedents of Einstein's thought, his notions of coordinate systems in motion relative to each other, of the possibility of countless, individual, variable space-times ...")
4.38 The idea of re-entry
Third Step
This is called re-entry and I suppose I can convey the idea by an analogy and also by setting up some structure. In your brain there are vast parts of, say, the cortex of your brain that wrinkled structure I mentioned before which are connected back and forth by parallel fibers, massively parallel fibers. They're also connected side to side. For example, your right cortex is connected to your left and vice versa though something called the corpus colosum. The corpus colosum has about 200 million axons going back and forth in both directions, mapping maps that are similar but not identical on each side of your brain. So when inputs come to those they send inputs back to the other side of your brain.
Well, imagine all these things happening at once and never staying still. Well, this is quite different than what you have, say, in this camera in some of the electronic devices. It's not feedback. Feedback is when you try to put an error signal in, after you've put an input in back to the original case with a correction; say, if you put in a sine wave and you want an amplified sine wave, if it's an error you send back the error and correct it, etc. In this case nothing of the sort is possible because we've assumed it's not a computer, it's not an electronic circuit; it's a selectional system. So when inputs come in to the two sides of your brain and they send inputs to each other over this massively parallel set of fibers, what's happening? Well, it's re-entry.
Re-entry is a recursive process of changing synaptic strengths across massively parallel connections in different parts of the brain. And what it tends to do is synchronize the circuits that connect these things in such a way that, out of the myriad numbers, certain ones are picked over others so they're selected. So here we have a kind of analogy with immunology; but we have to be careful here because the analogy's also with evolution. All of these selectional processes have three steps:
- the first step is the origin of diversity you have to have some way of making differences.
- Second, you have to poll that which is going to be recognised by the recognizer or vice versa.
- And third, you have to get some form of differential amplification of ones that fit the past.
In evolution you get the diversifier by mutation; you get the circling from behavior and competition in the environment, and, finally, in the third case, you get differential reproduction of the progeny of those animals that are more fit.
In immunology you have this process of somatic variation I talked about, where you make a whole bunch of different antibody combining cells, each 10¹¹ of them 10 followed by 11 zeros of different cells, each with a different antibody, one each. And then you pick those that bind a particular foreign molecule, even one that never existed before, and you stimulate the production of those cells, so that the next time around you see more antibodies of that kind.
Well, in the brain what is it? Well, in the brain it is that a developmental and experiential selection cause an enormous repertoire of variant dynamic circuits. But here it's much harder. You have to think of the whole thing as very dynamic because there are signals flying back and forth all over the place in this closely coupled anatomy. And what seems to hold the whole thing together is this business of re-entry namely... and we've tested this here in a series of theoretical models, namely the idea that, through re-entry and constant correction you will get synchronous circuits that work to be part of that repertoire and are selected. How are they selected? Because the synaptic strengths are increased mutually.
4.39 The idea of value
Well, there's one thing I've left out and it's a very important thing philosophically speaking or morally speaking... I don't know how to put it. And that is the so-called idea of value. All of this occurs somatically in an individual according to this theory but it can't occur unless you've already inherited something that we call value. Let me illustrate that by a concept... how do I put it? By... by saying there are, there are anatomical structures in the brain, about six of them, called value systems.
For instance if I go like this, your locus coeruleus which is a set of little blue spots about 6000 neurons each, release noradrenalin all over your brain through a leaky hose. If I have you tested and you're trying to perform something for a reward, you release dopamine through another set of signals coming from parts of the ventral tegmentum and also something called the basal ganglia. If I go to other parts of the brain, it's acetylcholine. There are these diffuse ascending systems that you are born with that have been selected by evolution to give you rewards or punishments if you will, according to your behavior. Those condition the selection I mentioned in this ternary relationship, developmental, experiential and re-entry. So you have this system working together and that was the gist of the theory I put together in Zurich.
Well, since then it's been elaborated much more completely and, indeed, in 1987 I published a book called Neural Darwinism. Well, that released a bit of a storm and I found out that, independent of its merits, if you want to have a lot of disturbance around you, theorize in biology. There's no doubt that it's a little bit different than in physics. In any case the book gave a much more extensive analysis of the situation from more points of view and of the developing theory, and it also of course looked for evidence to support the theory. Now, as you know, there's no way you can prove a theory in science; there's only a way you can perhaps disprove it. And so far I'm happy to report the theory hasn't been disproven. I personally believe it is terribly important to have that theory because, unlike the other organs that develop, as complex as they are; say the kidney or the liver, the brain is after all giving rise to these amazing properties of knowledge, consciousness, all of the philosophical notions etc., etc., epistemology, how you know, how it all goes together, language. So how does this all go together in this disparate mess? There are so many different levels of organization in that brain that you're struck through with awe when you really look at the complexity of it.
Well, the position I took on the theory was this: that maybe we can't prove it, because you can't do that with a scientific theory, but at least we can show it's self-consistent. And so, as a result of that, my colleagues and I have run a series of brain models. We've made models of these different processes that I talked about, and shown that at least the theory is self-consistent. If you try to express a theory like this just in words, the complexity is not embedded. You've got to go into details and see how that goes, and in a series of publications we did just that. Again you notice the word "we" because in fact I've been fortunate to be joined by a number of people, particularly at this institute, who are interested in this issue.
4.40 Reentry and synchrony: response to criticism of "Neural Darwinism"
I mentioned that one of ways in which you can get fervor and sometimes negative fervor, is to produce a... produce a theory in biology, especially a global one, because you're accused of hubris, of extraordinary overarching ambition, even though it isn't ambition it's more like aspiration and seeking to understand. But there is something else about it and I respond by saying that, in addition to its range, this book Neural Darwinism that I wrote was considered to be hair-raisingly dense in fact, one famous neurobiologist said to me, "I put in on my night table and I try to read one page, and it's like trying to read a whole book; haven't you got any mercy? Can't you open this thing up? And it's true that there was an extraordinary amount of consideration of dense subjects. But I, in fact, told this chap that, when I finished writing this book, even this book, never mind the one that I did way back in 1977 or [197]8... when I finished writing this I felt like a Roman centurion at the time of the Caesars, battling each other, and I came home, they said what was it like and I was full of blood and mud and all kinds of things that were not at all resolved and that involved enormous amounts of struggle. Because what my chief motivation was in writing this book was the idea that a theory in biology above all, even if it can't be predictive, should relate disparate findings. They should make understanding possible. And it seemed to me the things that I was considering were not held mutually. In fact, I considered that the field was in crisis. What do I mean by that?
Well, crisis in biology is not the same as crisis in physics. In physics for instance you had that famous one that took all of classical physics down called The Ultraviolet Catastrophe, that Planck first addressed, when you had a black body radiator and you increased its temperature according to the so-called Wien law, what happened as you approached the ultraviolet is the solution became infinite and it was a catastrophe and only by assuming the energy was put forth in quanta could you solve the problem of radiation from a black body and that began quantum mechanics. And you had to take down all of physics at that point.
Well, in biology you can always blame the other guy, and I say there's a crisis in cognitive science but, thank God, not in anatomy, or there's a crisis in neurophysiology but, thank God, not in cognitive science, etcetera. And here I was trying this very effortful thing and I admit that, to this very day, it has a flavor of... the sense of an ending is not fully there. And so you have to be a little more careful about what it is you're saying and you can't look back retrospectively with the same kind of satisfaction as you can, say, with the antibody problem. And that came out very clearly to me and it's still true... it's uppermost in my mind right now. But I did feel there was one thing about this theory that did depend on the others, not on me, and that was to get a group of people at the Neuroscience Institute particularly to do these models which are based on the theory and show that they work. So, for example, one of the hardest things to show, and one of the hardest things to understand, is this problem of re-entry.
Well, we actually made models of re-entry, and maybe the best way of conveying what entry... re-entry is doing in a selectional system and a brain theory like neural Darwinism is to use the analogy of a string quartet. Consider that you have a string quartet consisting of four very stubborn individual players. And each one decides he's going to play in the meter he wants and in the melodic system that he wants, diatonic or otherwise, and when you listen you hear just a discordant mess. Now supposing some genie comes along and hooks up every part of the body of every player with minute, almost invisible threads, so that when a violinist leans forward to do X and a cellist moves backward, that's conveyed to the other guys. Well, pretty soon you will notice that what happens is they tend to play more and more in synchrony, they tend then to approach each other at least in partial forms to create circles of what I'll call the re-entry. That's the closest I can come, because in fact it is sitting still is one thing, it's not a solution like in physics, for feedback, you have something called first order lag with dead time; you send a correction function back on one circuit and you fix it so your sine wave is now more accurate. Here it's this incredible complexity. But gradually, as a result of dynamic interactions and simultaneity and in the nervous system changing the synaptic strengths, you get coherency, you get simultaneity, and it's those things that act as part of the repertoire that you're going to put out that is selection on your behavior.
4.41 Michael Merzenich and stroke patients: brain adjusts (neuroplasticity) - neurodarwinism
There is one more very important point to make, and that is that in neural modeling above all, you can't just do many models abstractly and expect to get deep answers and that's because of the following: the brain is embodied and the body is embedded. What do I mean by that? I mean... well, let's take the example I love the most, for example, as a violinist... when you play the violin, it's a rather unnatural position; your elbow's all the way over here and the other one has got to be, at least according to the Russian schools, that you move in a plane and you don't lift your shoulder too high or knock your elbow down too low. When you look at that you... you have to convey that there's... there's a considerable problem and the problem is this: that if I, for instance, had an octopus tentacle or a squid tentacle that was extremely good at certain kinds of things, I could never play the violin, no matter what. And the reason is I have no joints, and if I want to play so-called spiccato or staccato and I have to have this kind of almost digital change in emphasis on the bow, having something without a joint will never work. Well, if I did put one in, my brain would change. And that's an important point that I want to mention.
And the reason I want to mention it is the work of Michael Merzenich at the University of California, San Francisco, was the first piece of work that I felt configured a real support for the idea of neural Darwinism. What he showed was that if he had a monkey tapping, say on a table, and he measured the response of neurons in the part of the brain called the somatosensory cortex, which is responsible for getting the messages about tapping and touch, he found an astonishing thing;
- namely that if he tapped on different fingers it would be a map that was individual for that monkey. So digit one would have this map for the smooth side of the hand, digit two another, third, etc, and you could make that map and no two monkeys were alike.
- But if, in fact, you had the monkey tap a lot, say with one finger, that the map responding to that finger would take other neurons away from the ones that are neighboring. Indeed, some would even take so-called face neurons away and make them hand neurons.
- And when you cut the nerve to the hand, one nerve, the so-called median nerve, that serves this part of the thumb and the first part of this, this finger and the first part of this finger on the smooth side, when you cut that the whole system rearranges its borders and smoothly.
Well, the only way you can really explain that result is through something like neural Darwinism, that these neuronal groups are competing to grab hold of other neurons in such a way as to make a new kind of map. And that was a very satisfactory finding. Indeed, it's been reported ever since that violinists have an incredible large map for their left hand.
And this all fits this notion of neural Darwinism very well. So the brain is altered by what kind of bodily reactions you have and, indeed, if I wanted to get very much more severe about it... I'll say it another way. It is so strong that even cognitively a patient will react differently to what happens in his body with his brain. Perhaps I should use that example. There is a disease, in a field called neuropsychology. Neuropsychology studies in large measure things that happen to you for example when you have a stroke. Now if you have a stroke on the right side of your brain... in the part of your brain called the parietal cortex, right over here above your ear, a little more posterior, you have what they call hemineglect: you do not see one half of the opposite part of the world. So if it's on your right cortex, where it usually is, you don't see the left half. So when you look at a clock you see from six to 12 or from 12 to six, either way depending on how you're looking at it, and not the other side.
4.42 Anosognosia
Well, there's another kind of disease related to that which is that, if you have a more extensive stroke, you have something called anosognosia, in which you don't even realize that you're paralyzed on your left side. So let me tell you the story of the neuropsychologist and neurologist Bisiach in Milan.
We had a patient of this kind who had anosognosia, had a massive stroke on the right side and he (Bislach) came up and said,
'Look, I've got these two cubes, they're identical; I'm going to put this one in your left hand and will take it in my left hand the other one. Now copy what I've done.' And he moved his hand around.
The patient said, 'There, Doc, I've done it.'
He said, 'No, you haven't.'
He (patient) said, 'Sure I have.'
He (Bislach) took the patient's hand and put it in his right visual field and said, 'Whose hand is this?'
And the patient said, 'Yours.'
And he (Bislach) said, 'I can't have three hands.'
And the patient said, 'Doc, it stands to reason, if you've got three arms you have to have three hands.'
Now, that theory is a very deep theory that would explain that, and we don't really have that theory yet. It would be almost like what Freud said... would be the equivalent of what he called Anna O, a kind of paradigm case that, if you explain that, you have the whole picture. So the brain is embodied and it depends in its dynamics on the kind of body you have. But the second thing is: the brain and the body are in the world, and the signals that go to your brain, unlike what we do in our laboratories, are enormously diverse and complex.
If you came in this room ten times and I changed the chairs or the... the table, you don't really believe that you keep every single detail of the last time in your mind, yet the number and diversity of different kinds of inputs, even at the same place, is absolutely astonishing.
So how can you put a brain theory together unless you consider all of these things?
INTENSO#1 - Oliver Sacks
Oliver Sacks (#75 - Ende ), 2011
WebofStories
Biography
Oliver Sacks was born in England in 1933.
Having obtained his medical degree at Oxford University, he moved to the USA. There he worked as a consultant neurologist at Beth Abraham Hospital where in 1966, he encountered a group of survivors of the global sleepy sickness of 1916-1927.
Sacks treated these patients with the then-experimental drug L-Dopa producing astounding results which he describes in his book Awakenings. Further cases of neurological disorders have been described by Sacks with exceptional sympathy in another major book entitled 'The Man Who Mistook His Wife For A Hat' which became an instant best seller on its publication in 1985.
His other books draw on his rich experiences as a neurologist gleaned over almost five decades of professional practice.
Sacks's work has been recognized by prestigious institutions which have awarded him numerous honours and prizes. These include the Lewis Thomas Prize given by Rockefeller University, which recognizes the scientist as poet. He is an honorary fellow of both the American Academy of Arts and Letters and the American Academy of Arts and Sciences, and holds honorary degrees from many universities, including Oxford, the Karolinska Institute, Georgetown, Bard, Gallaudet, Tufts, and the Catholic University of Peru.
look into Wikipedia
INTENSO#1 - Yehudi Menuhin
Yehudi Menuhin, Baron Menuhin, OM, KBE (22 April 1916 - 12 March 1999) was an American-born violinist and conductor who spent most of his performing career in the United Kingdom. He became a citizen of Switzerland in 1970, and a British subject in 1985. He is widely considered one of the greatest violinists of the 20th century
Music of Man (1979)
- The Quiver of Life
- The Flowering of Harmony (Roots of Music: Voices)
- New Voices (Italian Renaissance, Venice Opera, Corelli, Monteverdi, African Ceremonial Music, Ireland, Stradivari, Guaneri, Purcell)
- The Age of the Composer (Haydn, Mozart, Beethoven, ...)
- The Age of the Individual (Romantic)
- The Parting of the Ways (American and European Music)
- The Known and the Unknown (20th Century)
- Sound or Unsound
INTENSO#1 - Leonard Bernstein
The Making of West Side Story (1985)
Leonard Bernstein conducts West Side Story
Rehearsals of West Side Story with Leonard Bernstein, Kiri Te Kanawa, Jose Carreras, Tatjana Troianos, Kurt Ollmann, Nina und Alexander Bernstein ... (full cast)
The Unanswered Question (Norton Lectures 1973)
At the beginning of his first Norton Lecture, Leonard Bernstein explained the importance of "inter-disciplinary values - that the best way to 'know' a thing is in the context of another discipline." In these six lectures, Bernstein communicated his ideas of the universality of musical language through wide-ranging analogies to linguistics, aesthetic philosophy, acoustics as well as music history. However, while many of his ideas are intellectually challenging, the great achievement of the lectures is that through their breadth they make complex musical concepts accessible to a general audience.
Bernstein based much of the lectures on the linguistic theories Noam Chomsky set out in his book, "Language and Mind." In the first 3 lectures (Classical Period), Bernstein analyzed music in
- linguistic terms phonology (sound),
- syntax (structure) and
- semantics (meaning)
- In the 4th lecture ("The Delights and Dangers of Ambiguity"), Bernstein looked at music from the Romantic period, with its heightened harmonic uncertainties and structural freedoms.
- The 5th lecture ("The Twentieth Century Crisis") outlined the movement toward atonality and the crisis provoked by this crucial change in our musical language. Charles Ives' "The Unanswered Question," one of the primary musical examples, became Bernstein's title for the entire series of lectures.
- The 6th lecture ("The Poetry of the Earth") concentrated on the work of Igor Stravinsky, whom Bernstein thought had found a musical answer to "the unanswered question," one that kept tonality at its center.
- The series ended with Bernstein's artistic and philosophical "credo," an essentially optimistic and celebratory statement of beliefs.
INTENSO#1 - Jacob Bronowski
The Ascent of Man
- Lower than the Angels - Evolution of man from proto-ape to 400,000 years ago.
- The Harvest of the Seasons - Early human migration, agriculture and the first settlements, war.
- The Grain in the Stone - Tools, development of architecture and sculpture.
- The Hidden Structure - Fire, metals and alchemy.
- Music of the Spheres - The language of numbers.
- The Starry Messenger - Galileo's universe.
- The Majestic Clockwork - Explores Newton and Einstein's laws.
- The Drive for Power - The Industrial Revolution.
- The Ladder of Creation - Darwin and Wallace's ideas on the origin of species.
- World within World - The story of the periodic table.
- Knowledge or Certainty - Physics and the clash of absolute knowledge, the oppressive state, and its misgivings realizing the result of its terrible outcome.
- Generation upon Generation - Life, genetics, and the cloning of identical forms.
- The Long Childhood - Bronowski's treatise on the commitment of man.
INTENSO#1 - Oppenheimer
Father of the Atomic Bomb
Written by Peter Prince, directed by Barry Davis (1980)
- Episode 1 - First years: Berkeley, Pasadena.
- Episode 2 - Autumn 1942. Groves chooses Oppenheimer. Hakon Chevalier.
- Episode 3 - Initial chaos in Los Alamos. Ed Condon leaves over quarrels with Groves. Jean Tatlock's suicide. Groves signs Oppenheimer's security clearance for Manhatten Project. Oppenheimer names Hakon Chevalier Christmas 1944.
- Episode 4 - James Tuck proposes, Edward Teller, Hans Bethe favor implosion lenses. George Kistiakowsky takes charge of Implosion. Objections from Chicago Lab, Oppenheimer: "I think these people in Chicago are naive." Teller: "It's a terrible responsibility." Death of Roosevelt.
- Episode 5 - Decision to drop A-Bomb on Japan. Trinity - Kistiakowsky blamed for implosion test failure. Oppenheimer: "I have become death."
- Episode 6 - Late 1940s, 7. June 1949: Oppenheimer summoned before closed session of House Unamerican Activities Committee, Frank Oppenheimer fired from his position at U Minnesota, Russian A-Bomb, Teller pro hydrogen bomb ("Super"): "We can see no limit to the potential destructive power of the hydrogen." Atomic Energy Commission General Advisory Commission (GAC) meeting, Lewis Strauss approves investigation into Oppenheimer, Teller tries to find scientists to work on Super, Oppenheimer declines: "It will be insatiable!". Oppenheimer's candid talk at Los Alamos about Strategic Air Command's (Curtis LeMay) paranoid war philosophy, his security clearance revoked, investigation doubts Oppenheimer's truthfulness. In the Matter of J. Robert Oppenheimer (in cache)
- Episode 7 - 1954 Hearings, Teller's testimony, late life in Princeton.
INTENSO#2 - Molecular Biology
Secret Universe - The Hidden Life of the Cell (2012)
Director: Michael Davis (as Mike Davis)
Writers: Patrick Makin, Adam Rosenthal
full cast and crew
Our Secret Universe - Resources
Secret Universe - Das verborgene Leben der Zelle (2012)
INTENSO#2 - Dokus - Eine Maschine verändert die Welt
Eine Maschine verändert die Welt
- Teil 1 - Wie die Computer rechnen lernten.
Ein Jahr nach dem 2. Weltkrieg wurde der erste Großrechner um eine Summe von 3 Millionen Dollar gebaut. Dieser Großrechner hatte die Kapazität eines heutigen Taschenrechners, war aber trotzdem eine bahnbrechende Erfindung.
In wenigen Jahrzehnten entwickelte sich der Computer zur wichtigsten Maschine unserer Zeit und wurde für die Menschen, ob zu Hause oder in der Berufswelt, allgegenwärtig. Doch wie kam man überhaupt auf die Idee, eine solche Maschine zu bauen. Der erste Mensch, der sich mit der Idee befasste, eine solche Maschine zu bauen, war Charles Babbage, um Rechenprozeduren von Fehlern zu befreien. Zu seiner Zeit gab es noch sogenannte "Rechenknechte", deren Aufgabe es war, langwierige Rechenoperationen auszuführen, die für die Industrie und die Schifffahrt (Navigation) sehr wichtig waren.
1822 erfand Babbage die erste Rechenmaschine, die aber noch mechanisch arbeitete und nichts mit den heutigen Computern gemeinsam hatte. Seine "Differenzmaschine", mit Dampf betrieben, funktionierte jedoch nie. Bald schon merkte der Professor für Mathematik an der Universität in Cambridge, dass eine solche Maschine zu einseitig war, und versuchte eine variablere Maschine herzustellen. Erste Heimcomputer kamen mit einem ROM, der das Betriebssystem beinhaltete.
Damit war ein Update nur durch Austausch dieses (seinerzeit teuren) Bausteins möglich. Auch standen nicht immer ROMs mit ausreichender Speicherkapazität zur Verfügung. Daher ging man dazu über, die Computer mit einer Firmware auszuliefern, die das Betriebssystem von einem externen Speichermedium lädt. Da der IBM-PC - im Gegensatz zu seinen damaligen Konkurrenzerzeugnissen - ausschließlich mit handelsüblichen Komponenten aufgebaut war, führte dies zu zahlreichen Nachbauten.
Der IBM-PC entwickelte sich zu einem inoffiziellen Industriestandard, weil er ohne Lizenzierung von IBM nachgebaut werden konnte.
- Teil 2 - Die Computerindustrie entsteht.
- Teil 3 - Computer für alle
- Teil 4 - Künstliche Intelligenz
INTENSO#1 - Feynman
No Ordinary Genius
Richard Feynman - Los Alamos From Below
Richard Feynman - Best Mind Since Einstein
INTENSO#1 - Einstein
E = m c2 - Einsteins Big Idea
INTENSO#1 - Club of Rome
2052 - A Global Forecast for the Next Forty Years Launch in Rotterdam Part 1
2052- A Global Forecast for the Next Forty Years Launch in Rotterdam Part 2
INTENSO#1 - PBS
NIKOLA TESLA (1856 - 1941) - MASTER OF LIGHTNING - Discovery-Science-History (documentary)
PBS Space Documentary - Welcome to Mars
Wernher von Braun, Missile to the moon (documentary) PBS, 2012
INTENSO#1 - BBC
Nelson Mandela
BBC - History - Nelson Mandela 1918-2013 by David Dimbleby
Rolihlahla Mandela was born in Transkei, South Africa on 18 July 1918 and was given the name of Nelson by one of his teachers. His father Henry was a respected advisor to the Thembu royal family.
ANC involvement
Mandela was educated at the University of Fort Hare and later at the University of Witwatersrand, qualifying in law in 1942. He became increasingly involved with the African National Congress (ANC), a multi-racial nationalist movement trying to bring about political change in South Africa. In 1948, the National Party came to power and began to implement a policy of 'apartheid', or forced segregation on the basis of race. The ANC staged a campaign of passive resistance against apartheid laws.
In 1952, Mandela became one of the ANC's deputy presidents. By the late 1950s, faced with increasing government discrimination, Mandela, his friend Oliver Tambo and others began to move the ANC in a more radical direction. In 1956, Mandela went on trial for treason. The court case lasted five years, and ended with Mandela being acquitted
Sharpeville
In March 1960, 69 black anti-apartheid demonstrators were killed by police at Sharpeville. The government declared a state of emergency and banned the ANC. In response, the organisation abandoned its policy of non-violence and Mandela helped establish the ANC's military wing 'Umkhonto we Sizwe' or 'The Spear of the Nation'. He was appointed its commander-in-chief and travelled abroad to receive military training and to find support for the ANC.
Life imprisonment
On his return he was arrested and sentenced to five years in prison. In 1963, Mandela and other ANC leaders were tried for plotting to overthrow the government by violence. The following year Mandela was sentenced to life imprisonment. He was held in Robben Island prison, off the coast of Cape Town, and later in Pollsmoor Prison on the mainland. During his years in prison he became an international symbol of resistance to apartheid.
In 1990, the South African government responded to internal and international pressure and released Mandela, at the same time lifting the ban against the ANC. In 1991 Mandela became the ANC's leader.
A respected global statesman
He was awarded the Nobel Peace Prize together with FW de Klerk, then president of South Africa, in 1993. The following year South Africa held its first multi-racial election and Mandela was elected its first black president.
In 1998, he was married for the third time to Graça Machel, the widow of the president of Mozambique. Mandela's second wife, Winnie, whom he married in 1958 and divorced in 1996, remains a controversial anti-apartheid activist.
In 1997 he stepped down as ANC leader and in 1999 his presidency of South Africa came to an end. In 2004, Mandela announced his retirement from public life, although his charitable work continued. On 29 August 2007, a permanent statue to him was unveiled in Parliament Square, London.
INTENSO#1 - WBGU
INTENSO#1 - WBGU
Lectures 02 - Reinhold Leinfelder: Global Megatrends
LEXAR 8GB - Climate Change - WBGU
Lectures 03 - Stefan Rahmstorf: Climate Change
INTENSO#1 - WBGU
Lectures 08 - Claus Leggewie: Agents of Transformation
Transcripts of Episode 2
Parts of englisch transcript
Ausschnitte in deutscher Übersetzung
Gliederung
- Verständnis der Rolle von Menschen beim Herbeiführen von gesellschaftlichem Wandel
- Das Konzept des "Vermittlers (Agenten) des Wandels" (agent of change)
- Phasen der gesellschaftlichen Ausbreitung des Wandels
- Arten und Rollen der Agenten des Wandels (The role of agency)
- Zeitliche Dynamik und Aktionsniveaus
- Dynamik der Innovation und Verbreitung auf der Mikro-, Meso- und Makroebene
- Agenten des Wandels zur Niedrig-CO2-Wirtschaft
Zeitpunkt im Vortrag: 3:39
4.a Zeitliche Dynamik und Aktionsniveaus
Wenn wir es nicht in einem Zeitfenster von 10 Jahren (von heute an gemessen) schaffen, eine Niedrig-CO2- Gesellschaft zu werden, werden wir es überghaupt nicht mehr schaffen.
Zeitpunkt im Vortrag: 3:40
Damit das erreicht wird, muss der gegenwärtig bestehende Wille befördert, thematisch ausgefüllt und in Handeln umgesetzt werden. Dazu braucht es ein Netz von Akteuren und einen Staat, der Initiative ergreift.
In der Geschichte großer Aufstände gab es Einzelne oder kleine Gruppen, die dagegen rebellierten, was Georg Büchner den schrecklichen Fatalismus der Geschichte nannte. Es gelang ihnen, was schier unmöglich schien, und so wurden sie zu Pionieren des Wandels.
Zeitpunkt im Vortrag: 4:21
Die Geschichte der Aufklärung und Revolutionen ist ebenso ein Beweis dafür wie der Kampf der Kolonien um Unabhängigkeit, symbolisiert durch den friedlichen Widerstand eines Mahatma Gandhi, Nelson Mandela, die Samtene Revolution in den Ostblockstaaten, in der DDR, durch Menschen herbeigeführt wie Lech Walesa und Bärbel Boley, nicht zu vergessen Willy Brandt und Michail Gorbatschow und die Massen auf der Straße.
Zeitpunkt im Vortrag: 5:21
Menschen, die bereits -sei es bewusstoder unbewusst- Teilnehmer an der Umwandlung sind, Regierungs- und Nichtregierungsorganisationen, müssen nicht nur ihren Wirkungskreis erweitern, sie müssen vor allem Strukturen und Netzwerke schaffen, welche zu rascher und nachhaltiger Mobilisierung von Akteuren des Wandels führen.
Zeitpunkt im Vortrag: 5:45
Damit sage ich: Es handelt sich heute tatsächlich um etwas wie eine Revolution.
Die strukturellen Voraussetzungen zur Umsetzung einer diesbezüglichen Bereitschaft in Handlungen sind bereits auf geschichtlicher Basis ausgearbeitet worden.
Mein (J.G.) Kommentar: Auf dieser Basis widerspricht der Sozialwissenschaftler Leggewie einer Annahme, nur ein verschindend kleiner Bruchteil der Bevölkerung habe Interesse an einem Wandel und würde sich -bei passender Gelegenheit- einbringen. Diese Charakterisierung ist zu grob in dem Sinne, dass sie die Strukturen, die Leggewie aufzeigt, nicht berücksichtigt. Sie bewirken einen zeitlich nicht linearen Verlauf des Wandels, d.h. es gibt Momente, an denen sich die Geschwindigkeit des Wandels dramatisch ändert, der Wandel z.B. zur Revolution wird.
Claus Leggewie, Harald Welzer:
"Das Ende der Welt wie wir sie kannten: Klima, Zukunft und die Chancen der Demokratie", 2009 (im Cache)
"Dass sie [die Erde] [dann] so, wie wir sie kannten, nicht mehr wiederzuerkennen ist, liegt nicht an der Natur, die bei aller Gesetzlichkeit immer Sprünge gemacht hat, sondern an dem von Menschen verursachten Wandel des Klimas. Das Weltklima kann an tipping points mit unkalkulierbarer Dynamik gelangen und umkippen, wenn nicht rasch - genau genommen: im kommenden Jahrzehnt - radikal anders gewirtschaftet und umgesteuert wird. Die kurze Spanne bis 2020 - nur zwei, drei Legislaturperioden, einen kurzen Wirtschaftszyklus, zwei Sommerolympiaden weiter - entscheidet über die Lebensverhältnisse künftiger Generationen."
INTENSO#1 - WBGU
Speech given by Lord Nicholas Stern, International WBGU Symposium, 9 May 2012, Berlin, Germany
INTENSO#2 - Dokus - Climate Change
"Das Schönauer Gefühl - Die Geschichte der Stromrebellen aus dem Schwarzwald".
"Die mitreißende Geschichte der Stromrebellen" (Quelle)
"Der Förderverein für umweltfreundliche Stromverteilung und Energieerzeugung Schönau im Schwarzwald e.V. (FuSS e.V.) hat einen einstündigen Dokumentarfilm über die Schönauer Energie-Initiativen produziert. Der Film schildert die unglaubliche Geschichte der "Schönauer Stromrebellen" von der Reaktorkatastrophe in Tschernobyl im Jahre 1986 bis zum Jahrestag der zehnjährigen Stromnetzübernahme 2007. Er wurde produziert, um andere Menschen und Initiativen über die Schönauer Initiative zu informieren und zu bürgerschaftlichem Engagement zu motivieren."
"Die DVD des Films kann kostenlos über FuSS e.V. per Mailbestellung bezogen werden."
INTENSO#2 - Dokus - Climate Change
James Hansen: Climate Change a Scientific, Moral and Legal Issue
The past is the key to the future. Contrary to popular belief, climate models are not the principal basis for assessing human-made climate effects. Our most precise knowledge comes from Earth's paleoclimate, its ancient climate, and how it responded to past changes of climate forcings, including atmospheric composition. Our second essential source of information is provided by global observations today, especially satellite observations, which reveal how the climate system is responding to rapid human-made changes of atmospheric composition, especially atmospheric carbon dioxide (CO2). Models help us interpret past and present climate changes, and, in so far as they succeed in simulating past changes, they provide a tool to help evaluate the impacts of alternative policies that affect climate.
Humans lived in a rather different world during the last ice age, which peaked 20,000 years ago. An ice sheet covered Canada and parts of the United States, including Seattle, Minneapolis and New York City. The ice sheet, more than a mile thick on average, would have towered over today's tallest buildings. Glacial-interglacial climate oscillations were driven by climate forcings much smaller than the human-made forcing due to increasing atmospheric CO2 -- but those weak natural forcings had a long time to operate, which allowed slow climate feedbacks such as melting or growing ice sheets to come into play.
Paleoclimate data yield our best assessment of climate sensitivity, which is the eventual global temperature change in response to a specified climate forcing. A climate forcing is an imposed change of Earth's energy balance, as may be caused, for example, by a change of the sun's brightness or a human-made change of atmospheric CO2. For convenience scientists often consider a standard forcing, doubled atmospheric CO2, because that is a level of forcing that humans will impose this century if fossil fuel use continues unabated.
We show from paleoclimate data that the eventual global warming due to doubled CO2 will be about 3 degrees C when only so-called fast feedbacks have responded to the forcing. Fast feedbacks are changes of quantities such as atmospheric water vapor and clouds, which change as climate changes, thus amplifying or diminishing climate change. Fast feedbacks come into play as global temperature changes, so their full effect is delayed several centuries by the thermal inertia of the ocean, which slows full climate response. However, about half of the fast-feedback climate response is expected to occur within a few decades. Climate response time is one of the important 'details' that climate models help to elucidate.
We also show that slow feedbacks amplify the global response to a climate forcing. The principal slow feedback is the area of Earth covered by ice sheets. It is easy to see why this feedback amplifies the climate change, because reduction of ice sheet size due to warming exposes a darker surface, which absorbs more sunlight, thus causing more warming. However, it is difficult for us to say how long it will take ice sheets to respond to human-made climate forcing because there are no documented past changes of atmospheric CO2 nearly as rapid as the current human-made change.
Ice sheet response to climate change is a problem where satellite observations may help. Also ice sheets models, as they become more realistic and are tested against observed ice sheet changes, may aid our understanding. But first let us obtain broad guidance from climate changes in the 'recent' past: the Pliocene and Pleistocene, the past 5.3 million years.
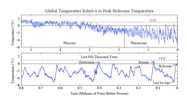
Surface temperatures for the past 5.3 million years
|
Figure 1 shows global surface temperature for the past 5.3 million years as inferred from cores of ocean sediments taken all around the global ocean. The last 800,000 years are expanded in the lower half of the figure. Assumptions are required to estimate global surface temperature change from deep ocean changes, but we argue and present evidence that the ocean core record yields a better measure of global mean change than that provided by polar ice cores.
|
"The mid Pliocene warm period is considered a potential analog of future climate. The intensity of the sunlight reaching the earth, the global geography, and carbon dioxide concentrations were similar to present. Furthermore many mid-Pliocene species are extant helping paleotemperature proxies calibration. Model simulations of mid-Pliocene climate produce warmer conditions at middle and high latitudes, as much as 10-20 degrees Celsius warmer than today above 70 degrees latitude north. They also indicate little temperature variation in the tropics. Model-based biomes are generally consistent with Pliocene paleobotanical data indicating a northward shift of the Tundra and Taiga and an expansion of Savanna and warm-temperate forest in Africa and Australia.[Salzmann, U.; Haywood, A. M.; Lunt, D. J. (2009). "The past is a guide to the future? Comparing Middle Pliocene vegetation with predicted biome distributions for the twenty-first century". Philosophical Transactions of the Royal Society A 367 (1886): 189-204. Bibcode:2009RSPTA.367..189S. doi:10.1098/rsta.2008.0200. PMID 18854302.]" (Source: Wikipedia
Civilization developed during the Holocene, the interglacial period of the past 10,000 years during which global temperature and sea level have been unusually stable. Figure 1 shows two prior interglacial periods that were warmer than the Holocene: the Eemian (about 130,000 years ago) and the Holsteinian (about 400,000 years ago). In both periods sea level reached heights at least 4-6 meters greater than today. In the early Pliocene global temperature was no more than 1-2 degrees C warmer than today, yet sea level was 15-25 meters higher.
The paleoclimate record makes it clear that a target to keep human made global warming less than 2 degrees C, as proposed in some international discussions, is not sufficient - it is a prescription for disaster. Assessment of the dangerous level of CO2, and the dangerous level of warming, is made difficult by the inertia of the climate system. The inertia, especially of the ocean and ice sheets, allows us to introduce powerful climate forcings such as atmospheric CO2 with only moderate initial response. But that inertia is not our friend - it means that we are building in changes for future generations that will be difficult, if not impossible, to avoid.
One big uncertainty is how fast ice sheets can respond to warming. Our best assessment will probably be from precise measurements of changes in the mass of the Greenland and Antarctic ice sheets, which can be monitored via measurements of Earth's gravitational field by satellites.
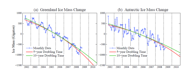
Greenland and Antarctic ice sheets are now losing mass at possibly increasing speed
|
Figure 2 shows that both Greenland and Antarctic ice sheets are now losing mass at significant rates, as much as a few hundred cubic kilometers per year. We suggest that mass loss from disintegrating ice sheets probably can be approximated better by exponential mass loss than by linear mass loss. If either ice sheet were to lose mass at a rate with doubling time of 10 years or less, multi-meter sea level rise would occur this century.
The available record (Figure 2) is too brief to provide an indication of the shape of future ice mass loss, but the data will become extremely useful as the record lengthens. Continuation of these satellite measurements should have high priority.
|
A copy of this web page is also available as a PDF document.
References
- Hansen, J., M. Sato, 2011: Paleoclimate implications for human-made climate change, Accepted for publication in "Climate Change at the Eve of the Second Decade of the Century: Inferences from Paleoclimate and Regional Aspects: Proceedings of Milutin Milankovitch 130th Anniversary Symposium" (A. Berger, F. Mesinger, and D. Sijaci, Eds.)
- Velicogna, I., 2009: Increasing rates of ice mass loss from the Greenland and Antarctic ice sheets revealed by GRACE, Geophys. Res. Lett., 36, L19503, doi:10.1029/2009GL040222.
Posted by James Hansen on Tuesday, 26 July, 2011
INTENSO#1 - Nicholas Stern
Sir Nicholas Stern: Meeting the climate challenge
Sir Nicholas Stern - The economics of climate change
A Conversation with Lord Nicholas Stern
INTENSO#2 - Dokus - Thor Heyerdahl
Kon-Tiki 1947
The Tangaroa-Expedition
Footage by Nordic World
All his life, Olav Heyerdahl had heard the stories of his grandfather: of how he crossed the Pacific in 1947 on a primitive raft made of balsa wood. Now at last, he got to experience it first hand.
As a tribute to his grandfather and the original Kon-tiki expedition, Olav and his team built a new raft in Peru and sailed it all the way to Raiatea in French Polynesia. When they arrived on the 24th of July 2006, after four months at sea, over a thousand people greeted them in a traditional Polynesian welcoming ceremony. This is a spectacular and unique documentary of the modern day voyage, with footage of the 1947 expedition setting the context. The 1947 Kon-tiki film won an Oscar, and Thor Heyerdahl's book has sold more the 50 millions copies worldwide. At the time, the whole world was amazed by this eccentric Norwegian explorer. The story continues to enthral 60 years later, only this time in colour.
INTENSO#2 - The Right Stuff
Tom Wolfe, Philip Kaufman, "The Right Stuff"
The Right Stuff is a 1983 American drama film that was adapted from Tom Wolfe's best-selling 1979 book of the same name about the Navy, Marine and Air Force test pilots who were involved in aeronautical research at Edwards Air Force Base, California, as well as the seven military pilots who were selected to be the astronauts for Project Mercury, the first attempt at manned spaceflight by the United States.
The search for the first Americans in space excludes Chuck Yeager, because he lacks a college degree. In spite of the fact that he was never selected as an astronaut, Colonel (later Brigadier General) Yeager was considered by many test pilots to be the best of them all.
Grueling physical and mental tests select the Mercury Seven astronauts, including John Glenn of the United States Marine Corps, Scott Carpenter, Alan Shepard, and Walter Schirra of the United States Navy, as well as Gordon Cooper, "Gus" Grissom and Donald K. "Deke" Slayton of the United States Air Force.
INTENSO#2 - Jeder stirbt für sich allein
Hans Fallada, Alfred Vohrer: "Jeder stirbt für sich allein"
Jeder stirbt für sich allein ist ein Film des Regisseurs Alfred Vohrer, gedreht im Jahr 1975 nach dem gleichnamigen Roman von Hans Fallada. Er basiert wie das Buch auf dem Leben des Berliner Ehepaars Otto Hermann Hampel und Elise Hampel.
Der Film spielt im Berlin von 1940 während des Zweiten Weltkriegs. Adolf Hitler steht auf dem Höhepunkt seiner Macht. Der Widerstand in Deutschland hat einen schweren Stand. Das Ehepaar Anna und Otto Quangel lebt in Berlin in einfachen Verhältnissen, ohne sich besonders für die Politik zu interessieren. Als jedoch ihr einziger Sohn Otto im Westfeldzug fällt, wächst mit der Trauer um den Sohn der innere Widerstand zum Nazi-Regime. Als auch eine jüdische Nachbarin zu Tode kommt, beschließt Anna, auch aktiven Widerstand zu betreiben. Sie schreibt ganz persönliche Flugblätter auf Feldpostkarten, die sie zunächst allein und später mit ihrem Mann an öffentlichen Plätzen auslegt und in Briefkästen in Berlin wirft. Die beiden werden jedoch entdeckt und kommen in Haft. Zum Ende werden sie zum Tode verurteilt. Otto Quangel tötet sich noch im Gerichtssaal mit einer Zyankalikapsel selbst; Anna wird zwei Monate später hingerichtet.
LEXAR_16GB - Filme - Der Aufstieg
Der Aufstieg - Ein Mann geht verloren.
Buch: Dieter Forte, Regie: Peter Patzak,
Darsteller: Ernst Schröder, Joachim Dietmar Mues, Ulrich Faulhaber, Ludwig Tiesen, Eberhard Busch, Marie-Luise Etzel, Gert Burkard, Ilsemarie Schnering,
Produktion: Peter Schulze-Rohr,
Produktion des Südwestfunks Baden-Baden, 1980
Ich glaube, in diesem Film zeigt Ernst Schröder eine seiner besten schauspielerischen Leistungen. Bemerkenswert finde ich die Verwandtschaft der Lebensumstände des Schauspielers Ernst Schröder vor und unmittelbar während des Filmens mit denen der von ihm dargestellten Person und die Ähnlichkeit des Filmendes mit dem Lebensende von Ernst Schröder, 14 Jahre später.
mein Kanal auf YouTube - meine Playlists
LEXAR_16GB - Filme - Jenseits von Schweden
Jenseits von Schweden
Buch und Regie: Carlheinz Caspari,
Darsteller (Personen): Karl Walter Diess (Hermann, der Professor), Christian Berkel (Dick, Sohn des Professors), Elisabeth Ackermann (Frau des Professors), Franz Rudnick (Egon, Bauunternehmer), Marianne Kehlau (Karin), Jörg-Peter Falkenstein (Kurt, persönlicher Referent des Professors), Günther Dockerill (Achim, Vertrauter des Professors), Ursula Vogel (Frau Zogelmann), David Anchondo (Gitarrist), Helga Bammert, Charlotte Bremer-Wolff, Jörg Christiansen, Heinz Dohmes, Günter Eisel, Rolf Jahncke, Wolfgang Kaven, Klaus-Hagen Latwesen, Thomas Meinhardt, Antje Mestern, Joachim Rake, Antj Reinkem, Charlie Rinn, Monica Rosenquist, Nikolaus Schilling, Günter Schulz, Uwe Steffen, Hans Peter Sternberg u.a.,
Produktion: Dieter Meichsner,
Norddeutscher Rundfunk Hamburg, 1979
Der politisch engagierte Carlheinz Caspari stellt die gesellschaftlich-politischen Verhältnisse der späten 1960er und frühen 1970er Jahre dar, ein Psychogramm eines Teils der damaligen Gesellschaft. Der Film ist eine Suche nach einer verlorenen Zeit, gefasst in den Begriff "Jenseits von Schweden". Der Film erinnert mich an Raul Ruiz' Film "Die wiedergefundene Zeit" nach Marcel Prousts Roman "La recherche du temps perdu".
Details:
Die Hauptperson (der Professor) ist frei nach dem charismatischen, einflussreichen Wirtschaftswissenschaftler, SPD-Minister und langjährigen Begleiter Willy Brandts, (Prof.) Karl Schiller, gestaltet, dessen Ideen einen wesentlichen Teil des Filminhalts bestimmen, z.T. als Antithese zu einem Desinteresse am eigenen Staat, wie es bei anderen Personen des Films erkennbar wird (Schnellbrief, in dem er die weitere Verschuldung der öffentlichen Hand als "stabilitätspolitisch nicht vertretbar" beschreibt). Sein Engagement für Deutschland hat Schiller in einem Brief zusammengefasst, den er bei seinem vorzeitigen Austritt aus der Regierung Brandt veröffentlicht hat: "Die Regierung hat die Pflicht, über den Tellerrand des Wahltermins hinauszublicken und dem Volk rechtzeitig zu sagen, was zu leisten ist und was zu fordern ist. Diese von mir mehrfach empfohlene Strategie ist bisher im Kabinett nicht einmal andiskutiert, geschweige denn akzeptiert worden." (Quelle: Karl Schiller, "Rücktrittsbrief des Bundesministers für Wirtschaft und Finanzen, 2. Juli 1972, Digitales Archiv, Marburg")
Teil 1 von 5, Teil 2 von 5, Teil 3 von 5, Teil 4 von 5, Teil 5 von 5
LEXAR_16GB - Filme - Clavigo
Johann Wolfgang von Goethe: Clavigo
Regie: Fritz Kortner,
Filmregie: Marcel Ophüls,
Thomas Holtzmann (Clavigo), Rolf Boysen (Carlos), Friedhelm Ptok (Beaumarchais), Krista Keller (Marie Beaumarchais), Kyra Mladek (Sophie), Hans Häckermann (Guilbert), Knut Hinz (Buenco), Horst Reckers (Saint George), Hans Irle (Diener des Clavigo)
Deutsches Schauspielhaus Hamburg, Norddeutscher Rundfunk, 1970
INTENSO#2 - Filme/Der Preis
Arthur Miller: Der Preis
Studio-Inszenierung des ZDF (1977) nach Arthur Millers Theaterstück "The Price" (1968). Personen (Darsteller): Victor Franz (Wolfgang Kieling), Esther Franz (Xenia Pörtner), Walter Franz (Rolf Henninger), Gregory Salomon (Werner Hinz), Regie: Thomas Fantl
Der Preis spielt im Dachgeschoss eines abbruchreifen Hauses, in dem das Mobiliar der Familie Franz aufbewahrt ist. Dieses Mobiliar soll nun verkauft werden. Dieser Verkauf lässt die beiden Brüdern Victor und Walter Franz nach langer, freiwillig gesuchter Trennung noch einmal aufeinandertreffen.
Der Vater der beiden war ein angesehener, reicher Mann, der bei einem großen Börsenkrach sein Vermögen verlor und wegzog, nachdem auch seine Frau gestorben war. Victor verzichtete auf sein Studium und wurde Polizist, um sich um seinen Vater zu kömmern. Walter beendete sein Studium, schickte monatlich 5 Dollar Zuschuss und wurde ein erfolgreicher Chirurg. Als die beiden Brüder beim Verkauf des Mobiliars an den jüdischen Makler Salomon aufeinandertreffen, müssen sie erkennen, dass eine Versöhnung nicht mehr möglich ist.
Liebe und Verantwortung sind die beiden Grundpfeiler, um die es geht. Victor beschuldigt Walter des Egoismus. Walter beweist, dass Victor vom Vater nur ausgenutzt wurde. Dieser aber will sich nicht eingestehen, dass er sein Leben einer Illusion gewidmet habe. Die vielen Jahre Trennung lassen sich nicht wieder gut machen. Walters Versuch scheitert. Er verzichtet auf die Hälfte des Erlöses und geht ohne Abschied. Esther, Victors Frau steht zwischen den beiden; sie anerkennt die Motive Walters und hält doch auch wieder zu ihrem Mann. Eine Lösung gibt es auch für sie nicht.
Theatertexte.de
LEXAR_16GB - Filme - Der Koenig und sein Narr
Frank Beyer: Der König und sein Narr
Regie: Frank Beyer
Drehbuch: Ulrich Plenzdorf, Martin Stade (Roman), Frank Beyer
1981 (Sender Freies Berlin (SFB), UFA Fernsehproduktion GmbH)
Wolfgang Kieling (Jacob Paul von Gundling), Götz George (Friedrich Wilhelm I.)
Fernsehfilm über die Rolle des Historikers und Gelehrten Jacob Paul von Gundling (1673 - 1731) am Hof des Soldatenkönigs Friedrich Wilhelm I. (1688 - 1740), über den Beitrag von engagierten Intellektuellen zur Entwicklung des frühen Preußen. Am Ende stirbt Gundling einen frühen Tod, was auf die Belastungen am preußischen Hof zurückgeführt wird. Letztendlich mündeten Gundlings Erfolge in die Stein-Hardenberg-Reformen (1807 - 1815). Deshalb ist das Filmende nach meinem Gefühl unangemessen düster.
LEXAR_16GB - Filme - Le Joueur de Violon
Charles van Damme: Le Joueur de Violon
Regie: Charles van Damme, Belgien, 1994
Drehbuch nach dem Roman "Le joueur de violon" von Andre Hodeir
Sprache: Französisch mit koreanischen Untertiteln
Zusammenfassung (mehr)
Es ist eine "Orpheus"-Geschichte: die Erweckung der Menschen durch die Musik, und im Film ist diese Musik die Chaconne der 2. Partita in d-moll von Johann Sebastian Bach. Gidon Kremer spielt sie, und mit ihm wird der Film zu einer Projektion dieser Chaconne in unser aller Leben.
LEXAR_16GB - Filme - MAHATMA
Vithalbhai Jhaveri: MAHATMA - Life of Gandhi, 1869-1948 (Wikipedia)
This is a 5 hrs. 10 min. documentary biography of Mohandas Mahatma Gandhi. All events and principles of Gandhi's life and thought are viewed as integrated parts of his truth-intoxicated life depicting permanent and universal values.
The purpose of the film is to tell the present and the future generations "that such a man as Gandhi in flesh and blood walked upon this earth", to acquaint them with his life and work and to spread his message of peace and universal brotherhood to the war-weary and fear-stricken world. The film brings together a mass of visual record not only of 78-year life of Gandhi but also of an important period of India's history.
The aim of the film being education and not entertainment, there is no attempt at dramatization of those exciting times. The story is told with an eye to truthful documentation of the main events within the limits of available documentary visual material...
Read more about the film (in cache)
Film id: mahatma_full_640x480
Courtesy: GandhiServe Foundation -- Mahatma Gandhi Research and Media Service
Contact for personal, institutional and commercial
The Gandhi National Memorial Fund
Script: Vithalbhai Jhaveri
Commentary: Vithalbhai Jhaveri
Direction: Vithalbhai Jhaveri
Voice: Romesh Thapar
Digital Mastering: Peter Ruhe
LEXAR_8GB - Interviews - LeCorbusier
Jacques Barsac: Le Corbusier
Part 3 of the 3 part 1987 film portrait "Le Corbusier" by Jacques Barsac, (dubbed in German).
(Co-) Production: Cine Service Technique, INA, Gaumont, Fondation Le Corbusier, La Sept, Antenne 2, Mission Cable, Channel Four, RTSR, Thomson Technique de Communication.
Internet: France-Diplomatie, "L'urbanisme du XXème siècle vu par Le Corbusier"
INTENSO#2 - Arts
Matisse
Simon Schama: Turner
Joseph Mallord William "J. M. W." Turner, RA (23 April 1775 -- 19 December 1851) was a British Romantic landscape painter, water-colourist, and printmaker. Turner was considered a controversial figure in his day, but is now regarded as the artist who elevated landscape painting to an eminence rivalling history painting.[1] Although renowned for his oil paintings, Turner is also one of the greatest masters of British watercolour landscape painting. He is commonly known as "the painter of light"[2] and his work is regarded as a Romantic preface to Impressionism.
Turner's talent was recognised early in his life. Financial independence allowed Turner to innovate freely; his mature work is characterised by a chromatic palette and broadly applied atmospheric washes of paint. According to David Piper's The Illustrated History of Art, his later pictures were called "fantastic puzzles." However, Turner was recognised as an artistic genius: the influential English art critic John Ruskin described him as the artist who could most "stirringly and truthfully measure the moods of Nature."
Turner placed human beings in many of his paintings to indicate his affection for humanity on one hand (note the frequent scenes of people drinking and merry-making or working in the foreground), but its vulnerability and vulgarity amid the 'sublime' nature of the world on the other. 'Sublime' here means awe-inspiring, savage grandeur, a natural world unmastered by man, evidence of the power of God--a theme that artists and poets were exploring in this period. The significance of light was to Turner the emanation of God's spirit and this was why he refined the subject matter of his later paintings by leaving out solid objects and detail, concentrating on the play of light on water, the radiance of skies and fires. Although these late paintings appear to be 'impressionistic' and therefore a forerunner of the French school, Turner was striving for expression of spirituality in the world, rather than responding primarily to optical phenomena.
Rain, Steam and Speed -- The Great Western Railway painted (1844)
His early works, such as Tintern Abbey (1795), stayed true to the traditions of English landscape. However, in Hannibal Crossing the Alps (1812), an emphasis on the destructive power of nature had already come into play. His distinctive style of painting, in which he used watercolour technique with oil paints, created lightness, fluency, and ephemeral atmospheric effects.
In his later years he used oils ever more transparently, and turned to an evocation of almost pure light by use of shimmering colour. A prime example of his mature style can be seen in Rain, Steam and Speed - The Great Western Railway, where the objects are barely recognizable. The intensity of hue and interest in evanescent light not only placed Turner's work in the vanguard of English painting, but exerted an influence on art in France; the Impressionists, particularly Claude Monet, carefully studied his techniques. As many of the day, Turner was a habitual user of snuff; in 1838 the King of France, Louis-Philippe presented a gold snuffbox to him. Two other snuffboxes, an agate and silver example bears Turner's name - the other, made of wood was collected along with his spectacles, magnifying glass and card case by an associate house keeper.
The first American to buy a Turner painting was James Lenox of New York City, a private collector. Lenox wished to own a Turner and in 1845 bought one unseen through an intermediary, his friend C. R. Leslie. From among the paintings Turner had on hand and was willing to sell for 500 pounds, Leslie selected and shipped the 1832 atmospheric seascape Staffa, Fingal's Cave. Worried about the painting's reception by Lenox, who knew Turner's work only through etchings, Leslie wrote to Lenox that the quality of Staffa, "a most poetic picture of a steam boat" would become apparent in time. On receiving the painting Lenox was baffled, and "greatly disappointed" by what he called the painting's "indistinctness". When Leslie was forced to relay this opinion to Turner, Turner said "You should tell Mr Lenox that indistinctness is my forte." Staffa, Fingal's Cave is now owned by the Yale Center for British Art.
The Power of Art - Turner (BBC Documentary, Simon Schama)
Quelle: wikipedia
entered on 21 October 2014:
INTENSO#2 - Angela Richter
Assassinate Assange - Vienna-Berlin-Trailer
entered on 21 October 2014:
INTENSO#2 - Angela Richter
Assassinate Assange - Reloaded - Theater Schauspiel Köln
"Im Juli 2011 treffen Angela Richter und Julian Assange zum ersten mal aufeinander: Mit etwas Glück ersteigerte sich die Regisseurin über Ebay die Eintrittskarte zu einem Essen, dessen Gastgeber eben der Initiator und Sprecher von Wikileaks war. Was folgte, waren nicht nur ein Artikel im Spiegel, in dem die Regisseurin ihre Eindrücke über jenes illustre 'Ebay-Lunch' schildert, sondern auch ein erneutes Treffen in London. Diesmal brauchte es allerdings nicht Glück, sondern Zeit. In einem vierstündigen Gespräch konnte Angela Richter Julian Assange dafür gewinnen, ihr Interviews zu geben, die später das Gerüst des Theaterstücks ASSASSINATE ASSANGE werden sollten.
Die ersten Treffen fanden im Sommer 2012 in der Botschaft von Ecuador in London statt, nachdem Ecuador Julian Assange politisches Asyl gewährt hat. Das Ergebnis der sehr intensiven Gespräche ist ein Textkonvolut aus 300 Seiten. ASSASSINATE ASSANGE hatte im September 2012 in Hamburg Premiere. Später folgten Aufführungen in Wien und Berlin. Angela Richter ist auch nach der Premiere mit Julian Assange in Verbindung geblieben und besucht ihn seither regelmäßig in der ecuadorianischen Botschaft, wo er sich inzwischen seit über 500 Tagen aufhält.
Anlässlich der Kölner Vorstellungen fuhr sie Ende Oktober 2013 nach London. Auf diesem Treffen drehte sich das Gespräch vor allem um die jüngsten Entwicklungen im NSA Spionage Skandal, Merkels Handy und die Flucht und das Asyl Edward Snowdens in Russland, an denen Julian Assange sowie seine Mitarbeiterin Sarah Harrison maßgeblich beteiligt waren. In Köln sehen Sie nun die neue, überarbeitete Fassung."
see also Angela Richter, "Die Avantgarde der Nerds" (im Cache)
"Sie haben Know-how, sind engagiert und kreativ - dennoch stoßen Netzaktivisten wie Julian Assange in der Kunstwelt auf Ablehnung. Ihre Vorreiterrolle wird nicht erkannt. "
entered on 21 October 2014:
INTENSO#2 - Angela Richter
Netzkultur: Einspruch! Freundschaft zwischen Avantgarde und Nerdtum
Datum 18. Januar 2014
Beginn 18:00 Uhr, Ende 19:00 Uhr
Veranstaltung: Berliner Festspiele, Gespräch (in englischer Sprache)
Mit Angela Richter (Regisseurin), Joseph Farrell (WikiLeaks-Botschafter), Allegra Searle-LeBel (Tänzerin, Internetfreiheitsaktivistin), Anjana Shrivastava (Moderation)
"Sind die Nerds und Hacker, die Computerspezialisten, die wahre Avantgarde des 21. Jahrhunderts? Sie stehen an der Speerspitze von weltweiten Bewegungen wie Anonymous und WikiLeaks, sie haben Zugang zu Informationen, die der "Normalbürger" nicht hat, und sie formen unser Verständnis von Öffentlichkeit und digitaler Gesellschaft aktiv mit. Die Theaterregisseurin Angela Richter arbeitet seit zwei Jahren eng mit WikiLeaks-Aktivisten zusammen und "bringt zwei Welten zusammen", die Kunst- und die IT-Szene, die sich oft kritisch beäugen. Im Juli 2011 luden der WikiLeaks-Gründer Julian Assange und der slowenische Philosoph Slavoj Zizek acht Personen zu einem exklusiven Lunch ein, deren Plätze man auf Ebay ersteigern konnte. Angela Richter war darunter, filmte alles und verwendete danach in ihrem Stück "Assassinate Assange" Originalmitschnitte von späteren Treffen mit dem Aktivisten. Seitdem steht sie in engem, auch künstlerischem Kontakt mit einer Reihe von Assange-Mitarbeitern. Ein Gespräch über Selbstzensur und klandestine Arbeitstreffen. Und über das, was man hinter sich lässt und lassen muss, wenn man Aktivist wird - und was man stattdessen dazugewinnt."
Quelle: Netzkultur: Einspruch! Freundschaft zwischen Avantgarde und Nerdtum (im Cache)
LEXAR_16GB - Interviews - Gropius
Walter Gropius im Gespräch mit Friedrich Luft
Sender Freies Berlin, 1965
LEXAR_16GB - Interviews - Max Plancks Selbstdarstellung 1942
Max Planck: Selbstdarstellung aus dem Jahre 1942
150 Jahre Max Planck,
Archiv der Berlin-Brandenburgischen Akademie der Wissenschaften, CD/DVD-Sammlung, Nr. 32
"Das Glück der Forschers besteht nicht darin, eine Wahrheit zu besitzen, sondern die Wahrheit zu erringen." Der Film "Geheimrat Max Planck", in dem der 84-jährige Planck in Form eines Selbstportraits über sein Leben und Werk berichtet, entstand am 15.12.1942 im Auftrag des Reichspropagandaministeriums. Er wurde nicht für die aktuelle Propaganda des Dritten Reichs eingesetzt, sondern war Teil einer Serie von Portraits, die zusammen ein "Filmarchiv der Persönlichkeiten" bilden sollten. Der Film wurde erst 1983 wiederentdeckt.
Dies ist ein Teil der Playlist "Max Planck und die Quantenphysik"
LEXAR_16GB - Interviews - HughThompson2
BBCWorld HARDtalk with Tim Sebastian - Guest: Hugh Thompson, Jr.
T. Sebastian: At some point you asked your men to train their guns on the American soldiers who were doing this [slaughtering].
H. Thompson: Yes, Sir, -we didn't have any choice. We'd tried -I'd almost say- to be nice and friendly. You know, we'd asked, .... and it was the only way, I could think of, to get it to stop. ... I thank God -to this day and a lot of days in between- that everybody played it cool and nobody started shooting because I really hate to have that on my conscience. We didn't volunteer to do it, it was -the only way out, and I felt we had to take it. "
T. S.: It's been hard to you to carry around.
H. Thompson: No, it's life, you get to do it, life goes on.
T.S.: Can you ever forgive the people who did that?
H. Thompson: No, ... no, I can't. I don't think I'm man enough to. I know the pain and suffering they inflicted ... for no reason, no reason whatsoever. There was no threat. There was no enemy.
T.S.: ... you went back to My Lai, you went back upon the 30. anniversary. You'd been the only official representative of the American government. ... You met one of them who survived. What did they say to you?
H. Thompson: Thanked me. One of them - came from out of nowhere - an interpreter brought her up, and she said "I want to meet Mr. Thompson." Everybody was kind of shocked, ... and Mr. Wallace said "Here is Mr. Thompson." ... I couldn't answer "Sorry I couldn't help her". Because - I had always wondered in my mind, did somebody there know that not all Americans were crazy and went mad that day. I wondered if anybody ever knew somebody was trying to help. And, boy, I was really happy when she knew I was trying to help. And she thanked me and I go "Sorry, I couldn't help her that day". And then ... with an interpreter it is real difficult because they only say like half a sentence at a time, and she asked, you know, why didn't the people that had done the killing come back with us? And, God, - I lost it, you know. I can hardly answer this, you know. And I was getting ready to - and then she finished her sentence and said "so we could forgive them." Oh, my god, it was, it was a riff for me right then, because it tore me up. These people, my enemies, have that much forgiveness in their hearts, and I'm not man enough to forgive my own people who did it. Can't do it.
Source
siehe auch: YouTube
Falling Walls, 2013 #3
Dunkle Materie, Gehirn-Computer und die Krise der Computer-Simulation - auf der "Falling Walls"-Konferenz (International Conference on Future Breakthroughs in Science and Society) am 9. Nov. 2013 in Berlin hat Philip Banse Interviews mit Wissenschaftlern gemacht.
LEXAR_8GB - Interviews - Philip Banse - Falling Walls 2013 #1
- Higgs und die Folgen: Rolf-Dieter Heuer, General-Direktor des CERN, erklärt Philip Banse, was die Entdeckung des Higgs-Boson für Menschen bedeutet und warum dunkle Materie und Energie weiterhin Rätsel bleiben.
- Die Simulationsfalle: Michael M. Resch, Leiter des Zentrums für High Performance Computing an der Universität Stuttgart, erklärt Philip Banse, warum Wolken nicht zu simulieren sind - und warnt, dass Computersimulationen von Klima, Knochen-Operationen und Meeresströmungen leiden könnten, weil niemand die teure Software schreiben will.
LEXAR_16GB - Interviews - Philip Banse - Falling Walls 2013 #3
- Künstliches Laub: Daniel G. Nocera, Chemiker und Harvard-Professor, erklärt Philip Banse, wie seine künstlichen Blätter die Welt aus der Energiekrise führen können.
INTENSO#2 - Philip Banse - Falling Walls 2013 #2
- Urknall und Expansion: Robert P. Kirshner, Astrophysiker und Harvard-Professor, erklärt Philip Banse warum sich das Universum nicht nur ausdehnt, sondern diese Ausdehnung sich sogar immer weiter beschleunigt.
- Das Gehirn als Bausatz: Karlheinz Meier, Professor für experimentelle Physik an der Universität Heidelberg und Co-Direktor des Human Brain Project, erklärt Philip Banse, wie er das menschliche Gehirn mit elektrischen Bauteilen nachbaut - und wie weit er damit bisher gekommen ist. Literatur: Human Brain Project (Report to the European Commission, April 2012, im Cache), Appendix 1, August 2013 (im Cache)
The Human Brain Project should pursue four goals, each building on existing work, and acting as a catalyst for new research.
1. Data: generate strategically selected data essential to seed brain atlases, build brain models and catalyse contributions from other groups.
2. Theory: identify mathematical principles underlying the relationships between dierent levels of brain organisation and their role in the brain ability to acquire, represent and store information.
3. ICT platforms: provide an integrated system of ICT platforms providing services to neuroscientists, clinical researchers and technology developers that accelerate the pace of their research.
4. Applications: develop first draft models and prototype technologies demonstrating how the platforms can be used to produce results with immediate value for basic neuroscience, medicine and computing technology.
- Facebook bremst Innovation: Mark Pagel, Professor für Evolutionsbiologe an der Universität Reading, erläutert, wie Kreativität entsteht und warum soziale Medien wie Facebook Innovation behindern.
- Elektronik aus Papier: Elvira Fortunato, Professor für Material-Wissenschaft an der Universität Lissabon, erklärt, wie sie elektronische Bauteile aus Papier herstellt und wie ihre durchsichtigen Displays funktionieren.
(Quelle: Philip Banse, dctp tv)
INTENSO#2 - Dokus - The Human Brain Project
Henry Markram, Promotional Video
Henry Markram (École Polytechnique Fédérale de Lausanne, EPFL), co-director, The Human Brain Project
The goal of the Human Brain Project is to pull together all our existing knowledge about the human brain and to reconstruct the brain, piece by piece, in supercomputer-based models and simulations. The models offer the prospect of a new understanding of the human brainand its diseases and of completely new computing and robotic technologies. On January 28, the European Commission supported this vision, announcing that it has selected the HBP as one of two projects to be funded through the new FET Flagship Program. Federating more than 80 European and international research institutions, the Human Brain Project is planned to last ten years (2013-2023). The cost is estimated at 1.19 billion euros.The project will also associate some important North American and Japanese partners. It will be coordinated at the Ecole Polytechnique Fédérale de Lausanne (EPFL) in Switzerland, by neuroscientist Henry Markram with co-directors Karlheinz Meier of Heidelberg University, Germany, and Richard Frackowiak of Centre Hospitalier Universitaire Vaudois (CHUV) and the University of Lausanne (UNIL).
A scientific portrait of the Human Brain Project
The Human Brain Project will provide new tools to help understand the brain and its fundamental mechanisms and to apply this knowledge in future medicine and computing. Central to the Human Brain Project is Information and Computing Technology (ICT). The project will develop ICT platforms for neuroinformatics, brain simulation and supercomputing that will make it possible to federate neuroscience data from all over the world, to integrate the data in unifying models and simulations of the brain, to check the models against data from biology and to make them available to the world scientific community. The ultimate goal is to allow neuroscientists to connect the dots leading from genes, molecules and cells to human cognition and behavior.
A novel medical informatics platform will federate clinical data from around the world, allowing medical researchers to unlock the clinically valuable information they contain and to incorporate it in computer models of disease. The goal is to develop techniques for the objective diagnosis of the brain diseases, to understand their underlying mechanisms and to speed up the search for new treatments.
Finally, the HBP will build new platforms for neuromorphic computing and neurorobotics, allowing researchers to develop new computing systems and robots based on the architecture and circuitry of the brain. The new systems will use detailed knowledge of the brain to address critical problems facing future computing technology: energy efficiency, reliability, the huge difficulties involved in programming very complex computing systems. The HBP will fund independent scientists to use the new platforms for their own research, reserving a substantial part of its budget for this purpose. In brief, the HBP will create a CERN for the brain.
The Swiss Contribution
Switzerland plays a vital role in the Human Brain Project. Henry Markram and his team at EPFL will coordinate the project and will also be responsible for the development and operation of the project Brain Simulation Platform. Richard Frackowiak and his team will be in charge of the project medical informatics platform; the Swiss Supercomputing Centre in Lugano will provide essential supercomputing facilities.
Many other Swiss groups are also contributing to the project. Through the ETH Board, the Swiss Federal Government has allocated 75 million CHF (approximately 60 million Euros) for the period 2013-2017, to support the efforts of both Henry Markram laboratory at EPFL and the Swiss Supercomputing Center in Lugano. The Canton of Vaud will give 35 million CHF (28 million Euros) to build a new facility called Neuropolis for in silico life science, and centered around the Human Brain Project. This building will also be supported by the Swiss Confederation, the Rolex Group and third-party sponsors.
History
The selection of the Human Brain Project as a FET Flagship is the result of more than three years of preparation and a rigorous and severe evaluation by a large panel of independent, high profile scientists, chosen by the European Commission. In the coming months, the partners will negotiate a detailed agreement with the Community for the initial first two and a half year ramp-up phase (2013-mid 2016). The project will begin work in the closing months of 2013.
Alton Parrish "Human Brain Project"
INTENSO#2 - Dokus - Clay Shirky
Clay Shirky
The power law distribution
Clay Shirky: Power Laws, Weblogs and Inequality
A persistent theme among people writing about the social aspects of weblogging is to note (and usually lament) the rise of an A-list, a small set of webloggers who account for a majority of the traffic in the weblog world. This complaint follows a common pattern we've seen with MUDs, BBSes, and online communities like Echo and the WELL. A new social system starts, and seems delightfully free of the elitism and cliquishness of the existing systems. Then, as the new system grows, problems of scale set in. Not everyone can participate in every conversation. Not everyone gets to be heard. Some core group seems more connected than the rest of us, and so on.
Prior to recent theoretical work on social networks, the usual explanations invoked individual behaviors: some members of the community had sold out, the spirit of the early days was being diluted by the newcomers, et cetera. We now know that these explanations are wrong, or at least beside the point. What matters is this: Diversity plus freedom of choice creates inequality, and the greater the diversity, the more extreme the inequality.
In systems where many people are free to choose between many options, a small subset of the whole will get a disproportionate amount of traffic (or attention, or income), even if no members of the system actively work towards such an outcome. This has nothing to do with moral weakness, selling out, or any other psychological explanation. The very act of choosing, spread widely enough and freely enough, creates a power law distribution.
Power law distributions, the shape that has spawned a number of
catch-phrases like the 80/20 Rule and the Winner-Take-All Society, are
finally being understood clearly enough to be useful. For much of the
last century, investigators have been finding power law distributions
in human systems.
LEXAR 8GB - Breitband: Audio-Beiträge (vom LEXAR 8GB abrufen über "Music")
Kommunikationswissenschaftler Stephan Weichert
"Wäre ein transparenterer Umgang mit Daten über die Stadt- und Regionsentwicklung ein Schlüssel zu mehr Akzeptanz politischer Projekte? Darum geht es im Gespräch mit dem Kommunikationswissenschaftler Stephan Weichert" (im Cache).
Quelle: breitband, Demokratie und Öffentlichkeit, Deutschlandradio Kultur, 2.10.2010
Gespräch mit Micah Sifry
Ein Gespräch mit Micah Sifry. Der US-Politblogger ist Mitbegründer des Personal Democracy Forums und gilt als Demokratie- und Netzexperte. In Kürze erscheint sein Buch “WikiLeaks and the Age of Transparency”. Das ungeschnittene, englischsprachige Gespräch mit Micah Sifry" (im Cache, Transskript, deutsche Übersetzung)
Quelle: breitband, The revolution will be facebooked, Deutschlandradio Kultur, 12.2.2011
INTENSO#2 - Dokus - Breitband: Audio-Beiträge (vom INTENSO#2 abrufen über "Music")
Schwerpunktinterview mit dem Wissenschaftler Thomas Gebel
"Politikverdrossenheit war gestern. Das Netz hat neue und sehr einfache Möglichkeiten der Bürgerbeteiligung geschaffen. Bricht ein Zeitalter der digitalen Basisdemokratie an? Und wie kann politische Teilhabe tatsächlich organisiert werden? Wir sprechen im Schwerpunktinterview mit dem Wissenschaftler Thomas Gebel" (im Cache).
Quelle: breitband, Topic, Deutschlandradio Kultur, 13.11.2010
Carne Ross
Carne Ross ("Independent Diplomat") on a new discourse on responsibilities of knowledge, minutes 42:33 - 49:30 in "Wikileaks and Internet Freedom", PdF Leaks I, Part 1 - 12/11/10", Personal Democracy Forum, New York, 2010.
more pdf Leaks, 2010
See also Carne Ross on Diplomacy and Wikileaks, 2013 International Niels Bohr Conference: An Open World.
INTENSO#1 - Breitband: Audio-Beiträge (vom INTENSO#1 abrufen über "Music")
Der offene Code - Wieso wir freie Software brauchen
So gut wie überall spielt Software eine wachsende Rolle. Das macht Code und Coder mächtig. Die Idee freier Software setzt Transparenz und Offenheit dagegen. FOSS, kurz für Free and Open-Source Software steht für Programmcode, der sich frei verwenden, weitergeben, verstehen und verändern lässt. Es geht um Freiheit im Sinne von Redefreiheit, nicht von Freibier, die Worte des FOSS-Pioniers Richard Stallman sind heute berühmt.
Aber was steckt wirklich hinter Open Source und freier Software? Ist das eine nerdige Gesellschaftsutopie, ein schön verpacktes Geschäftsmodell, eine Netz-Ideologie oder doch einfach nur kapitalistische Wertschöpfung mit anderen Mitteln? Was sind Vor- und Nachteile freier Software, wie und von wem wird sie entwickelt und wer schmückt sich mit dem Label?
Software is just the beginning, open source is doing for mass innovation what the assembly line did for mass production. Get ready for the era when collaboration replaces the corporation. (Wired 2003)
Philip Banse (siehe auch Falling Walls, 2013) spricht im Talk mit drei Gästen:
-
Claudia Rauch arbeitet für KDE e.V., eine nichtkommerzielle Organisation, die eines der größten internationalen Programmpakete für freie Software unterstützt. Dort ist sie unter anderem zuständig für Öffentlichkeitsarbeit, Kommunikation und die Arbeit mit der Community und organisiert internationale Konferenzen zum Thema Free Software. Twitter @frankfurtine
- Harald Welte ist Programmierer und Open-Source-Aktivist. Mit dem Projekt gpl-violations.org wies er auf Verstöße gegen die GNU General Public License hin und setzte sich gerichtlich dagegen durch. Dafür wurde er mit dem Free Software Advancement Award 2007 der Free Software Foundation ausgezeichnet. Er hat in der Vergangenheit am Betriebssystem Linux mitgearbeitet und entwickelt heute als Initiator von Osmocom freie Software für Mobilfunknetze. Twitter @LaF0rge
-
Leonhard Dobusch ist Juniorprofessur für Organisationstheorie im Fachbereich Wirtschaftswissenschaft und BWL an der Freien Universität Berlin. In seiner Promotion verglich er die Betriebssysteme Windows und Linux. Er forscht zu den Themen Innovation, Standardisierung und private Regulierung, vor allem zu Urheberrechtsmärkten. Links: Vortrag von Dobusch über Open Source | Twitter @leonidobusch
Quelle: Breitband, Deutschlandradiokultur, 21. März 2014
INTENSO#2 Hanna Reitsch
Interview
Hanna Reitsch kam als zweites von drei Kindern des Arztes Willy Reitsch, der eine Augenklinik leitete, und seiner Frau Emy (geb. Helff-Hibler von Alpenheim) zur Welt. Sie träumte bereits als Kind von der Fliegerei; die Jugendliche gab als Traumberuf "fliegende Missionsärztin" an. Wenn sie schulfrei hatte, fuhr sie mit dem Rad nach Grunau zum Segelflugplatz. Dort lernte sie Anfang der 1930er Jahre auch den jungen Wernher von Braun kennen, mit dem sie eine lebenslange Freundschaft verband. 1931 absolvierte sie ihr Abitur, anschließend besuchte sie die "Koloniale Frauenschule" in Rendsburg. Ab 1932 studierte sie Medizin in Berlin und Kiel.
Neben ihrem Studium erwarb die nur 1,50 Meter große Frau 1932 den Segel- und den Motorflugschein auf dem Flugplatz Berlin-Staaken. Noch im selben Jahr stellte sie ihren ersten Rekord auf: den Dauer-Segelflugrekord für Frauen (5,5 Stunden in der Luft). 1933 wurde Hanna Reitsch von Wolf Hirth gebeten, als Fluglehrerin an seiner neuen Segelfliegerschule auf dem Hornberg bei Schwäbisch Gmünd zu arbeiten. Von 1933 bis 1934 nahm sie an einer Forschungsexpedition in Brasilien und Argentinien teil und brach ihr Medizinstudium nach vier Semestern zugunsten der Fliegerei ab. 1936 stellte sie mit 305 Kilometern einen neuen Streckenweltrekord im Segelflug der Frauen auf. Weitere Rekorde folgten (siehe Abschnitt: Fliegerische Leistungen).
Als Versuchs- und Erprobungspilotin
Vom Juni 1934 an arbeitete Hanna Reitsch als Versuchspilotin für die "Deutsche Forschungsanstalt für Segelflug" in Griesheim. Dabei arbeitete sie eng mit dem bekannten Konstrukteur und DFS-Abteilungsleiter Hans Jacobs zusammen. Als erste Frau der Welt wurde sie 1937 von Ernst Udet zum Flugkapitän ehrenhalber ernannt und im September 1937 als Versuchspilotin an die Flugerprobungsstelle der Luftwaffe Rechlin berufen. Dort erprobte sie Stukas, Bomber und Jagdflugzeuge. Von 1937 an flog sie den von Henrich Focke gebauten Hubschrauber Focke-Wulf Fw 61 (später umbenannt in Fa 61, nach dem Firmen-Mitinhaber und ehemaligen Kunstflieger und Testpiloten Gerd Achgelis), mit dem sie im Oktober desselben Jahres mit einem 109-km-Flug einen Streckenweltrekord für Hubschrauber aufstellte. 1938 führte Reitsch diesen Hubschrauber in der Deutschlandhalle in Berlin beim ersten Hubschrauber-Hallenflug der Welt vor. Auch ein Flug mit dem Motorsegler und Nur-Flügler Horten H II (Kennung D-11-187) der Brüder Horten in der Nähe von Berlin im November 1938 ist durch einen ihrer Testberichte dokumentiert, in dem sie u. a. vermerkt, dass sie den Fahrwerkshebel auf Grund ihrer zu kurzen Arme nicht bedienen konnte.
Als Versuchspilotin flog Reitsch zusammen mit Erich Klöckner 1939 den für die deutschen Luftlandetruppen vorgesehenen Großsegler DFS 230 ein und am 8. März 1941, 11 Tage nach dem Erstflug, den Lastensegler Me 321.
Mit der Dornier Do 17 und der Heinkel He 111 flog sie Versuche, um herauszufinden, ob die Stahlseile britischer Ballonsperren mit einem vor dem Bug des Flugzeuges angebrachten Gerät zerschnitten werden konnten. 1942 flog Reitsch in Augsburg das Raketenflugzeug Messerschmitt Me 163 - allerdings lediglich im reinen Schleppflug in einer antriebslosen Zelle der Me 163 ohne den hochexplosiven Zwei-Komponenten-Raketen-Treibstoff. Dies war Reitsch aufgrund ihrer damaligen Bedeutung für die NS-Propaganda ausdrücklich untersagt worden, da man das damit verbundene hohe Risiko eines schweren (Start-)Unfalls, wie er nicht selten war, nicht eingehen wollte. Zudem nahm sie an Versuchen mit der bemannten Fieseler V1 ("Reichenberg") teil. Bei ihrer Erprobungstätigkeit wurde Hanna Reitsch mehrmals schwer verletzt. Für ihren Einsatz erhielt sie unter anderem das Eiserne Kreuz zweiter und erster Klasse (das EK I als einzige Frau der deutschen Geschichte) und das Flugzeugführer- und Beobachterabzeichen in Gold mit Brillanten (Melitta Schenk Gräfin von Stauffenberg und Reitsch waren die einzigen so ausgezeichneten Frauen).
Ab dem Winter 1943/1944 setzte Reitsch sich für die Entwicklung der "Selbstopfer"-Flugzeuge ein. Dieses Projekt, das sie am 28. Februar 1944 Adolf Hitler vorschlug, sah bemannte Bomben vor, bei denen der Tod des Piloten in Kauf genommen wurde, ähnlich dem japanischen "Kamikaze". Das Projekt stieß in der Luftwaffenführung auf erheblichen Widerstand und wurde nicht realisiert. Am 26. April 1945 flog sie mit dem Generaloberst Robert Ritter von Greim mit einem Fieseler Storch in das von der Roten Armee bereits eingeschlossene Berlin, wo Hitler von Greim bei gleichzeitiger Beförderung zum Generalfeldmarschall zum Nachfolger Görings als Oberbefehlshaber der Luftwaffe ernannte.
Quelle: Wikipedia
INTENSO#2 Shock and Awe
Shock and Awe, The Story of Electricity
Jim Al-Khalili charts the history of mankind's attempt to understand and harness the power of electricity. He begins by exploring the writings and theories of scientific innovators including Humphrey Davy and Stephen Gray, and examines the methods they used to create and control electrical forces. He also tells the story of the battery, the first major breakthrough in the human race's battle to use electricity for its own ends.
Teil 1: Elektrostatik
Wie kam der Mensch hinter die Geheimnisse der Stromerzeugung und -speicherung - bis hin zur Erfindung eines bahnbrechenden kleinen Gegenstands: der Batterie. Im 18. und zu Beginn des 19. Jahrhunderts machten Physiker in England, im niederländischen Leiden, in den Vereinigten Staaten, in Marly bei Paris, in Bologna und Padua mit viel Intuition, einer Portion Glück und unter dem Druck der Konkurrenz eine Entdeckung nach der anderen. Der Zuschauer erfährt von der Erfindung des elektrostatischen Motors, des Blitzableiters, der ersten Elektrobatterie, der Voltaikbatterie und der allerersten Bogenlampe.
Im Mittelpunkt dieser Dokumentation stehen prägende Persönlichkeiten wie Isaac Newton, Francis Hawksbee, Pieter van Musschenbroeck, Benjamin Franklin, George-Louis Leclerc und Thomas-François Dalibard, Henry Cavendish, Luigi Galvani, Alessandro Volta, Humphry Davy, Giovanni Aldini und andere.
Teil 2: Magnetismus
Vor nur 200 Jahren entdeckten Wissenschaftler, dass die Elektrizität von einer großen Kraft der Natur abhängt: dem Magnetismus. In diesem Teil, der zu Beginn des 19. Jahrhunderts einsetzt, erläutert Jim Al-Khalili, wie der Mensch das Zusammenwirken der beiden Kräfte zu nutzen lernte. Auf einmal konnte eine unbegrenzte Menge an Elektrizität erzeugt werden, um Maschinen zu betreiben, zwischen Kontinenten zu kommunizieren und Räume mittels Lampen zu beleuchten. Der Zuschauer sieht, wie Forscher, Ingenieure und Unternehmer hinter die Geheimnisse der Elektrizität kamen und damit den Telegrafen, das erste transatlantische Kabel, die Glühlampe und den Wechselstrom erfanden. Diese technischen Neuerungen ermöglichten die Beleuchtung von Manhattan, den Bau erster Kraftwerke, wie beispielsweise das erste Wasserkraftwerk in der Nähe der Niagarafälle, und die Erfindung des elektrischen Stuhls. Im Mittelpunkt dieser Folge stehen wegweisende Persönlichkeiten wie Michael Faraday, Humphry Davy, Hans Christian Oersted, William Sturgeon, Joseph Henry, Samuel Morse, Thomas Alva Edison, Joseph Wilson Swan, George Westinghouse, Nikola Tesla und Harold P. Brown.
Teil 3: Null. Eins
Von der Vernetzung der Welt durch Radioübertragung und Datenverarbeitungsnetze sowie der endgültigen Erschließung der Elektrizität auf atomarer Ebene. Die Dokumentation beginnt im England des späten 19. Jahrhunderts und stellt Oliver Joseph Lodge, James Clerk Maxwell, Henrik Hertz, Guglielmo Marconi, Jagadish Chandra Bose, Heinrich Geißler, William Crookes, Joseph John Thomson und Ernest Rutherford vor. Weitere Themen der Sendung sind die Entdeckung der Radiowellen, die Wimshurstmaschine, die erste Radiofabrik, die revolutionären Supraleiter, die Entdeckung des Elektrons und des Mikrochips sowie der Aufstieg des Silicon Valley.
Title: Shock and Awe: The Story of Electricity -
- Episode 01: Spark
- Episode 02: The Age of Invention
- Episode 03: Revelations and Revolutions
Producer: BBC, Steve Crabtree, Tina Fletcher-Hill, Tim Usborne, Jim Al-Khalili (presenter)
Category: Science, Shock and Awe: The story of Electricity
INTENSO#2 IT
The Moment of Truth: Glenn Grenwald, Kim Dotcom, Edward Snowden, Julian Assange, recorded on September 15, 2014.
INTENSO#2 IT
Lawrence Lessig Interviews Edward Snowden, Harvard Law School, October 20, 2014.
INTENSO#2 IT
Katrina vanden Heuvel and Stephen F. Cohen, "Edward Snowden: A 'Nation' Interview, October 28, 2014. (in cache)
In a wide-ranging conversation, he discusses the surveillance state, the American political system and the price he's paid for his understanding of patriotism.
Excerpts
"One concern I had while I was working actively in the intelligence community - being someone who had broad access, who was exposed to more reports than average individuals, who had a better understanding of the bigger picture - was that the post-World War II, post-Cold War directions of societies were either broadly authoritarian or [broadly] liberal or libertarian.
Has the center of gravity shifted such that all governments have greater powers and fewer restrictions than they ever had, and are empowered by technology in a way that no government ever was in the past? How do we preserve our civil rights, our traditions as a liberal democracy, in a time when government power is expanding and is more and more difficult to check?
There is more action in some other countries. In Germany, they've called for a very serious inquiry that's discovering more and more. They've just discovered a significant violation of the German Constitution that had been concealed from the Parliament.
We are a representative democracy. But how did we get there? We got there through direct action. And that's enshrined in our Constitution and in our values. We have the right of revolution. Revolution does not always have to be weapons and warfare; it's also about revolutionary ideas. It's about the principles that we hold to be representative of the kind of world we want to live in. A given order may at any given time fail to represent those values, even work against those values. I think that's the dynamic we're seeing today. We have these traditional political parties that are less and less responsive to the needs of ordinary people, so people are in search of their own values. If the government or the parties won't address our needs, we will. It's about direct action, even civil disobedience.
"Occupy Wall Street" had an impact on consciousness. It was not effective in realizing change. But too often we forget that social and political movements don't happen overnight. They don't bring change immediately - you have to build a critical mass of understanding of the issues. But getting inequality out there into the consciousness was important. All these political pundits now talking about the 2014 and 2016 elections are talking about inequality.
The surveillance revelations are critically important because they revealed that our rights are being redefined in secret, by secret courts that were never intended to have that role - without the consent of the public, without even the awareness of the majority of our political representatives. However, as important as that is, I don't think it is the most important thing. I think it is the fact that the director of national intelligence gave a false statement to Congress under oath, which is a felony. If we allow our officials to knowingly break the law publicly and face no consequences, we're instituting a culture of immunity, and this is what I think historically will actually be considered the biggest disappointment of the Obama administration. ... There was a real choice when he became president. It was a very difficult choice - to say, "We're not going to hold senior officials to account with the same laws that every other citizen in the country is held to," or "This is a nation that believes in the rule of law." And the rule of law doesn't mean the police are in charge, but that we all answer to the same laws.
The Nation: Do you think people on the congressional intelligence committees knew more than other senators and representatives? That they knew they were being told falsehoods and they remained silent?
Snowden: The chairs absolutely do. They're part of the "Gang of Eight." They get briefed on every covert-action program and everything like that. They know where all the bodies are buried. At the same time, they get far more campaign donations than anybody else from defense contractors, from intelligence corporations, from private military companies.
I would say the first key concept is that, in terms of technological and communication progress in human history, the Internet is basically the equivalent of electronic telepathy. ... We can now communicate all the time through our little magic smartphones with people who are anywhere, all the time, constantly learning what they're thinking, talking about, exchanging messages. And this is a new capability even within the context of the Internet. When people talk about Web 2.0, they mean that when the Internet, the World Wide Web, first became popular, it was one way only. People would publish their websites; other people would read them. But there was no real back and forth other than through e-mail. Web 2.0 was what they called the collaborative web - Facebook, Twitter, the social media. What we're seeing now, or starting to see, is an atomization of the Internet community. Before, everybody went only to a few sites; now we've got all these boutiques. We've got crazy little sites going up against established media behemoths. And increasingly we're seeing these ultra-partisan sites getting larger and larger readerships because people are self-selecting themselves into communities. I describe it as tribalism because they're very tightly woven communities. Lack of civility is part of it, because that's how Internet tribes behave. We see this more and more in electoral politics, which have become increasingly poisonous.
All this is a blessing and a curse. It's a blessing because it helps people establish what they value; they understand the sort of ideas they identify with. The curse is that they aren't challenged in their views.
It's like a fashion trend, and becomes a sign of a lack of sophistication. On the other hand, the Internet is there to fill needs that people have for information and socialization. We get this sort of identification thing going on nowadays because it's a very fractious time. We live in a time of troubles.
Look at the reactions of liberal governments to the surveillance revelations during the last year. In the United States, we've got this big debate, but we've got official paralysis - because they're the ones who had their hand caught most deeply in the cookie jar. And there are unquestionable violations of our Constitution. Many of our ally states don't have these constitutional protections - in the UK, in New Zealand, in Australia. They've lost the right to be free from unreasonable search and seizure without probable cause. All of those countries, in the wake of these surveillance revelations, rushed through laws that were basically ghostwritten by the National Security Agency to enable mass surveillance without court oversight, without all of the standard checks and balances that one would expect. Which leads us inevitably to the question: Where are we going to reject that easy but flawed process of letting the intelligence services do whatever they want? It's inevitable that it will happen. I think it's going to be where Internet businesses go.
For example, Microsoft is in a court battle with the Department of Justice. The DOJ is saying, "We want information from your data center in Ireland. It's not about a US citizen, but we want it." Microsoft said, "OK, fine. Go to a judge in Ireland. Ask them for a warrant. We have a mutual legal-assistance treaty. They'll do it. Give that to us, and we'll provide the information to you in accordance with Irish laws." The DOJ said, "No, you're an American company, and we have access to your data everywhere. It doesn't matter about jurisdiction. It doesn't matter about who it's regarding." This is a landmark legal case that's now going through the appeals process. And it matters because if we allow the United States to set the precedent that national borders don't matter when it comes to the protection of people's information, other countries are watching. They're paying attention to our examples and what is normative behavior in terms of dealing with digital information.
... So the question becomes what does, for example, the government in the Democratic Republic of Congo or China do the next time they've got a dissident Nobel Peace Prize nominee and they want to read his e-mail, and it's in an Irish data center? They're going to say to Microsoft, "You handed this stuff over to the DOJ; you're going to hand the same thing over to us." And if Microsoft balks, they'll say, "Look, if you're going to apply different legal standards here than you do there, we're going to sanction you in China. We're going to put business penalties on you that will make you less competitive." And Microsoft will suffer, and therefore our economy will suffer.
... constitutionally, only Congress can declare war, and that is routinely ignored. Not NATO or the UN, but Congress has to authorize these endless wars, and it isn't.
The Bush administration marked a very serious and profoundly negative turning point - not just for the nation, but for the international order, because we started to govern on the idea of "might makes right." And that's a very old, toxic and infectious idea. ... A reaction in many ways to 9/11, but also to the Dick Cheney idea of the unitary executive. They needed a pretext for the expansion of not simply federal power, but executive power in particular.
... Richard Nixon got kicked out of Washington for tapping one hotel suite [Watergate]. Today we're tapping every American citizen in the country, and no one has been put on trial for it or even investigated. We don't even have an inquiry into it.
... That's the key - to maintain the garden of liberty, right? This is a generational thing that we must all do continuously. We only have the rights that we protect. It doesn't matter what we say or think we have. It's not enough to believe in something; it matters what we actually defend. So when we think in the context of the last decade's infringements upon personal liberty and the last year's revelations, it's not about surveillance. It's about liberty. When people say, "I have nothing to hide," what they're saying is, "My rights don't matter." Because you don't need to justify your rights as a citizen - that inverts the model of responsibility. The government must justify its intrusion into your rights. If you stop defending your rights by saying, "I don't need them in this context" or "I can't understand this," they are no longer rights. You have ceded the concept of your own rights. You've converted them into something you get as a revocable privilege from the government, something that can be abrogated at its convenience. And that has diminished the measure of liberty within a society.
The Nation: Every president - and this seems to be confirmed by history - will seek to maximize his or her power, and will see modern-day surveillance as part of that power. Who is going to restrain presidential power in this regard?
Snowden: That's why we have separate and co-equal branches. Maybe it will be Congress, maybe not. Might be the courts, might not. But the idea is that, over time, one of these will get the courage to do so. One of the saddest and most damaging legacies of the Bush administration is the increased assertion of the "state secrets" privilege, which kept organizations like the ACLU - which had cases of people who had actually been tortured and held in indefinite detention - from getting their day in court. The courts were afraid to challenge executive declarations of what would happen. Now, over the last year, we have seen - in almost every single court that has had this sort of national-security case - that they have become markedly more skeptical. People at civil-liberties organizations say it's a sea change, and that it's very clear judges have begun to question more critically assertions made by the executive. Even though it seems so obvious now, it is extraordinary in the context of the last decade, because courts had simply said they were not the best branch to adjudicate these claims - which is completely wrong, because they are the only nonpolitical branch. They are the branch that is specifically charged with deciding issues that cannot be impartially decided by politicians. The power of the presidency is important, but it is not determinative. Presidents should not be exempted from the same standards of reason and evidence and justification that any other citizen or civil movement should be held to.
The Nation: About this secretive deep state, are you hopeful? Your revelations are so sweeping, people might think there's nothing we can do. Or they could lead to actions that challenge, even dismantle, these anti-democratic forces.
Snowden: There's definitely a deep state. Trust me, I've been there.
Well, we've already seen, in practically every country around the world where these issues have been covered, that the general public has recoiled at the ideology behind these programs.
OK, let me clarify. When I talk about the polling, I'm talking about the principles. It shows these officials are knowingly attempting to shift public opinion, even though they know what they say is not factual. It's clear it's public opinion, because elite opinion ... I mean, The New York Times and The Guardian came out and said, "Hey, clemency for Snowden." But for me, the key - and I've said this from the beginning: it's not about me. I don't care if I get clemency. I don't care what happens to me. I don't care if I end up in jail or Guantánamo or whatever, kicked out of a plane with two gunshots in the face. I did what I did because I believe it is the right thing to do, and I will continue to do that. However, when it comes to political engagement, I'm not a politician - I'm an engineer. I read these polls because civil-liberties organizations tell me I need to be aware of public opinion. The only reason I do these interviews - I hate talking about myself, I hate doing this stuff - is because incredibly well-meaning people, whom I respect and trust, tell me that this will help bring about positive changes. It's not going to cause a sea change, but it will benefit the public.
The Nation: Say there was a national Gallup poll formulating the question like this: "Mr. Snowden has revealed gross violations of your personal liberties and rights through surveillance by the American government. The American government argues it does so to keep you safe from terrorists." Do you think there would be a majority opinion in your favor? You've raised perhaps the most vital issue of our time, but for most Americans, who really are having a harder economic time than they should be having, your issue probably is not high on their list of concerns.
Snowden: ... From the very beginning, I said there are two tracks of reform: there's the political and the technical. I don't believe the political will be successful, for exactly the reasons you underlined. The issue is too abstract for average people, who have too many things going on in their lives. And we do not live in a revolutionary time. People are not prepared to contest power. We have a system of education that is really a sort of euphemism for indoctrination. It's not designed to create critical thinkers. We have a media that goes along with the government by parroting phrases intended to provoke a certain emotional response - for example, "national security." Everyone says "national security" to the point that we now must use the term "national security." But it is not national security that they're concerned with; it is state security. And that's a key distinction. We don't like to use the phrase "state security" in the United States because it reminds us of all the bad regimes. But it's a key concept, because when these officials are out on TV, they're not talking about what's good for you. They're not talking about what's good for business. They're not talking about what's good for society. They're talking about the protection and perpetuation of a national state system.
... Since the revelations, we have seen a massive sea change in the technological basis and makeup of the Internet. One story revealed that the NSA was unlawfully collecting data from the data centers of Google and Yahoo.
They were intercepting the transactions of data centers of American companies, which should not be allowed in the first place because American companies are considered US persons, sort of, under our surveillance authorities. They say, "Well, we were doing it overseas," but that falls under a different Reagan-era authority: EO 12333, an executive order for foreign-intelligence collection, as opposed to the ones we now use domestically. So this one isn't even authorized by law. It's just an old-ass piece of paper with Reagan's signature on it, which has been updated a couple times since then.
So what happened was that all of a sudden these massive, behemoth companies [Google, Yahoo, Facebook, ...] realized their data centers - sending hundreds of millions of people's communications back and forth every day - were completely unprotected, electronically naked. ... So what they [the government] did was just get out of the protected part [the transmission paths] and they went onto the back network. They went into the private network of these companies.
Companies did not know it. They said, "Well, we gave the NSA the front door; we gave you the PRISM program. You could get anything you wanted from our companies anyway - all you had to do was ask us and we're gonna give it to you." So the companies couldn't have imagined that the intelligence communities would break in the back door, too - but they did, because they didn't have to deal with the same legal process as when they went through the front door. When this was published by Barton Gellman in The Washington Post and the companies were exposed, Gellman printed a great anecdote: he showed two Google engineers a slide that showed how the NSA was doing this, and the engineers "exploded in profanity."
Another example - one document I revealed was the classified inspector general's report on a Bush surveillance operation, Stellar Wind, which basically showed that the authorities knew it was unlawful at the time. There was no statutory basis; it was happening basically on the president's say-so and a secret authorization that no one was allowed to see. When the DOJ [Department of Justice] said, "We're not gonna reauthorize this because it is not lawful," Cheney - or one of Cheney's advisers - went to Michael Hayden, director of the NSA, and said, "There is no lawful basis for this program. DOJ is not going to reauthorize it, and we don't know what we're going to do. Will you continue it anyway on the president's say-so?" Hayden said yes, even though he knew it was unlawful and the DOJ was against it. Nobody has read this document because it's like twenty-eight pages long, even though it's incredibly important.
The big tech companies understood that the government had not only damaged American principles, it had hurt their businesses. They thought, "No one trusts our products anymore." So they decided to fix these security flaws to secure their phones. The new iPhone has encryption that protects the contents of the phone. This means if someone steals your phone - if a hacker or something images your phone - they can't read what's on the phone itself, they can't look at your pictures, they can't see the text messages you send, and so forth.
- But it does not stop law enforcement from tracking your movements via geolocation on the phone if they think you are involved in a kidnapping case, for example.
- It does not stop law enforcement from requesting copies of your texts from the providers via warrant.
- It does not stop them from accessing copies of your pictures or whatever that are uploaded to, for example, Apple's cloud service, which are still legally accessible because those are not encrypted.
- It only protects what's physically on the phone. This is purely a security feature that protects against the kind of abuse that can happen with all these things being out there undetected.
In response, the attorney general and the FBI director jumped on a soap box and said, "You are putting our children at risk."
This is the controversy that the attorney general and the FBI director were trying to create. They were suggesting, "We have to be able to have lawful access to these devices with a warrant, but that is technically not possible on a secure device. The only way that is possible is if you compromise the security of the device by leaving a back door". We've known that these back doors are not secure. I talk to cryptographers, some of the leading technologists in the world, all the time about how we can deal with these issues. It is not possible to create a back door that is only accessible, for example, to the FBI. And even if it were, you run into the same problem with international commerce: if you create a device that is famous for compromised security and it has an American back door, nobody is gonna buy it.
Anyway, it's not true that the authorities cannot access the content of the phone even if there is no back door. When I was at the NSA, we did this every single day, even on Sundays. I believe that encryption is a civic responsibility, a civic duty.
...I spoke with Tim Berners-Lee, the guy who invented the World Wide Web. We agree on the necessity for this generation to create what he calls the Magna Carta for the Internet. We want to say what "digital rights" should be. What values should we be protecting, and how do we assert them? What I can do - because I am a technologist, and because I actually understand how this stuff works under the hood - is to help create the new systems that reflect our values. Of course I want to see political reform in the United States. But we could pass the best surveillance reforms, the best privacy protections in the history of the world, in the United States, and it would have zero impact internationally. Zero impact in China and in every other country, because of their national laws - they won't recognize our reforms; they'll continue doing their own thing. But if someone creates a reformed technical system today - technical standards must be identical around the world for them to function together.
... you are also asked to take an oath, and that's the oath of service. The oath of service is not to secrecy, but to the Constitution - to protect it against all enemies, foreign and domestic. That's the oath that I kept, that James Clapper and former NSA director Keith Alexander did not.
... As for labeling someone a whistleblower, I think it does them - it does all of us - a disservice, because it "otherizes" us. Using the language of heroism, calling Daniel Ellsberg a hero, and calling the other people who made great sacrifices heroes - even though what they have done is heroic - is to distinguish them from the civic duty they performed, and excuses the rest of us from the same civic duty to speak out when we see something wrong, when we witness our government engaging in serious crimes, abusing power, engaging in massive historic violations of the Constitution of the United States. We have to speak out or we are party to that bad action.
... It also comes down to parenting. It is important to know what your beliefs are, and that you have to stand up for them or you don't really believe in them. You know, my father and mother - in fact, every member of my immediate family - have worked for the federal government. Sometimes misunderstood is that I didn't stand up to overthrow the system. What I wanted to do was give society the information it needed to decide if it wanted to change the system.
There's a real danger in the way our representative government functions today. It functions properly only when paired with accountability. Candidates run for election on campaign promises, but once they're elected they renege on those promises, which happened with President Obama on Guantánamo, the surveillance programs and investigating the crimes of the Bush administration. These were very serious campaign promises that were not fulfilled. I considered bringing forward information about these surveillance programs prior to the election, but I held off because I believed that Obama was genuine when he said he was going to change things. I wanted to give the democratic process time to work.
... When governments go too far to punish people for actions that are dissent rather than a real threat to the nation, they risk delegitimizing not just their systems of justice, but the legitimacy of the government itself. Because when they bring political charges against people for acts that were clearly at least intended to work in the public interest, they deny them the opportunity to mount a public-interest defense. The charges they brought against me, for example, explicitly denied my ability to make a public-interest defense. There were no whistleblower protections that would've protected me - and that's known to everybody in the intelligence community. There are no proper channels for making this information available when the system fails comprehensively.
... Going all the way back to Daniel Ellsberg, it is clear that the government is not concerned with damage to national security, because in none of these cases was there damage. At the trial of Chelsea Manning, the government could point to no case of specific damage that had been caused by the massive revelation of classified information. The charges are a reaction to the government's embarrassment more than genuine concern about these activities, or they would substantiate what harms were done. We're now more than a year since my NSA revelations, and despite numerous hours of testimony before Congress, despite tons of off-the-record quotes from anonymous officials who have an ax to grind, not a single US official, not a single representative of the United States government, has ever pointed to a single case of individualized harm caused by these revelations. This, despite the fact that former NSA director Keith Alexander said this would cause grave and irrevocable harm to the nation. Some months after he made that statement, the new director of the NSA, Michael Rogers, said that, in fact, he doesn't see the sky falling. It's not so serious after all.
The Nation: [Sakharov] was the co-creator of the Soviet hydrogen bomb, a nuclear scientist. He began to worry about what he'd created, and eventually began to protest government policies. But he didn't prefer the word "dissident" because, like you, he said: "First, the Soviet Constitution says I have every political right to do what I am doing. And second, the Soviet government is violating its own Constitution, while the people do not know what the government is doing in its name."
Snowden: [laughs] Wow, that sounds familiar. It's interesting that you mention Sakharov's creative axis - he had produced something for the government that he then realized was something other than he intended. That's something [NSA whistleblower] Bill Binney and I share. Binney designed ThinThread, an NSA program that used encryption to try to make mass surveillance less objectionable. It would still have been unlawful and unconstitutional. Binney will argue with you all day about it, but his idea was that it would collect everything about everybody but be immediately encrypted so no one could read it. Only a court could give intelligence officials the key to decrypt it. The idea was to find a kind of a compromise between [privacy rights and] the assertion that if you don't collect things as they happen, you won't have them later - because what the NSA really wants is the capability of retrospective investigation. They want to have a perfect record of the last five years of your life, so when you come to their attention, they can know everything about you. I'm not down with that, but Binney was trying to create something like that.
The Nation: You also remind us of [Manhattan Project physicist] Robert Oppenheimer - what he created and then worried about.
Snowden: Someone recently talked about mass surveillance and the NSA revelations as being the atomic moment for computer scientists. The atomic bomb was the moral moment for physicists. Mass surveillance is the same moment for computer scientists, when they realize that the things they produce can be used to harm a tremendous number of people.
It is interesting that so many people who become disenchanted, who protest against their own organizations, are people who contributed something to them and then saw how it was misused. When I was working in Japan, I created a system for ensuring that intelligence data was globally recoverable in the event of a disaster. I was not aware of the scope of mass surveillance. I came across some legal questions when I was creating it. My superiors pushed back and were like, "Well, how are we going to deal with this data?" And I was like, "I didn't even know it existed." Later, when I found out that we were collecting more information on American communications than we were on Russian communications, for example, I was like, "Holy shit."
Being confronted with the realization that work you intended to benefit people is being used against them has a radicalizing effect.
If I had to guess what the future's going to look like for me - assuming it's not an orange jumpsuit in a hole - I think I'm going to alternate between tech and policy. I think we need that. I think that's actually what's missing from government, for the most part. We've got a lot of policy people, but we have no technologists, even though technology is such a big part of our lives. It's just amazing, because even these big Silicon Valley companies, the masters of the universe or whatever, haven't engaged with Washington until recently. They're still playing catch-up.
As a technologist, I see the trends, and I see that automation inevitably is going to mean fewer and fewer jobs. And if we do not find a way to provide a basic income for people who have no work, or no meaningful work, we're going to have social unrest that could get people killed. When we have increasing production - year after year after year - some of that needs to be reinvested in society. It doesn't need to be consistently concentrated in these venture-capital funds and things like that. I'm not a communist, a socialist or a radical. But these issues have to be addressed.
Version: 19.4.2017
Address of this page
Home
Jochen Gruber