
click on image to enlarge
Henri Rousseau: The snake charmer, painting symbolizing the power structure in our society

Amazon rainforest as an example and possible model of a continuously evolving societal system
A Physicist's Travels
Heartfulness, Horizons, Hypotheses
Feel the Earth move and then
Hear my heart burst again
So we'll go to the end
I've drowned and dreamt this moment
So overdue, I owe them
Swept away, I'm stolen
Let the sky fall
When it crumbles
We will stand tall
Face it all together
Let the sky fall
When it crumbles
We will stand tall
Face it all together
At Skyfall
At Skyfall
Skyfall is where we start
A thousand miles and poles apart
Where worlds collide and days are dark
You may have my number, you can take my name
And you'll ever have my heart
Let the sky fall
When it crumbles
We will stand tall
Face it all together
Let the sky fall
When it crumbles
We will stand tall
Face it all together
At Skyfall
Where you go, I go
What you see, I see
I know I'd never be me
Without the security
Of your loving arms
Keeping me from harm
Put your hand in my hand
And we'll stand
Let the sky fall
When it crumbles
We will stand tall
Face it all together
Let the sky fall
When it crumbles
We will stand tall
Face it all together
At Skyfall
Let the sky fall
We'll stand tall
At Skyfall
|
Abstract Past year a film led me through new mental landscapes. It opened up horizons for me to understand where our society might be heading. The model: Human society has now organized itself with information technology in the same way that animate nature has done over the past half a billion years. This concept, a "biological-societal" model, has become a key for me to the door behind which I see the future of our democracy. In order to preserve our culture, we must maintain the love of God on this journey of ours into the future, as defined, for example, by Joseph Ratzinger in his 1968 Tübingen lecture "Introduction to Christianity" in the tradition of the philosophy of the Stoa. |
Part 1
Heartfulness
The film "Interface" gives me an impression of the convincing power of any kind of interfaces/intermediaries and of my limitations. Accordingly, it depends on my humanity how I use this power. This builds bridges for me to other people who have come to other convictions through this power.
In 1968 the Professor of Theology Joseph Ratzinger used the concept of "Love of God" in his Tübingen University lecture series "Introduction into Christianity" (pages 257, 258):
Only where the value of love is above the value of life for someone, that is, only where someone is willing to put life behind love and for the sake of love, only then can love be stronger and more than death.
In order for love to surpass death, it must first be more than mere life. But if it then could be not only in the will but in reality, this would mean immediately that the power of love had risen above the mere power of the biological and had taken it into its service.
Speaking in the terminology of Teilhard de Chardin: Where this would take place, there the decisive "complexity" and complexion would have happened; there also the bios would be embraced and included by the power of love. There it would transcend its limit - death - and create unity where it separates.
If the power of love for the other would be somewhere so strong that it would be able to keep alive not only his memory, the shadow of his I, but himself, then a new stage of life would be reached, which would leave behind the space of biological evolutions and mutations and would mean the leap to a completely different level, in which love would no longer stand under the bios, but would use it.
Such a last stage of "mutation" and "evolution" would then no longer be a biological stage itself, but would mean the breaking out of the exclusive rule of the bios, which is at the same time the rule of death; it would open that space, which the Greek Bible calls "zoe", that is final life, which has left behind the regiment of death.
The last stage of evolution, which the world needs in order to reach its goal, would then no longer be carried out within the biological, but by the spirit, by freedom, by love. It would no longer be evolution, but decision and gift in one.
Part 2
Horizons
We humans have organized ourselves using information technology (IT) in much the same way as the biosphere did over hundreds of millions of years in just a decade.
400 million years of stability
The higher the competence and the stability based on it of the components in the levels, the better a living being or a society can resist external influences or compensate their effect. Conversely, vulnerabilities (incompetences) of the levels, depending on the degree of severity, lead to externally imposed evolution, damage or even destruction. According to Michael Levin, the competence of the components is virtually a characteristic of the system.
Examples of other properties of biological organization:
2.1 Films/Videos
2.2 Vulnerabilities of Our Society
API Security Gartner Predicition
By 2022, Gartner estimates that the most popular attack vector will be spear phishing, resulting in violations of company web applications. Gartner predicts API violence. APIs enable millions of connected devices to communicate with backend servers, gain access to data, and communicate with one another.
Low security in the API can lead to painful and damaging effects like hacker attacks and data violations.
According to Gartner
Attacks and data breaches involving inadequately secured APIs are occurring regularly. Protecting web APIs solely with general-purpose application security solutions has proven to be ineffective over the years. Each new API represents a new and potentially unique attack vector into your systems, which you should be aware of.
What does this API security mean?
APIs became a de facto standard for the modern web during the post-iPhone era, the post-app Store era. Two primary drivers ensured that many application programming interfaces were created: the growth of mobile applications that require web-based backend APIs and the SPA architecture.
This means the internet is now part of the API, meaning that API security is now the security of web applications.
An Example of how API's can be used. Source: Matt Taibbi, 2023:
The Twitter Files expose Hamilton 68 as a sham.
The secret ingredient in Hamilton 68's analytic method was a list of 644 accounts supposedly linked "to Russian influence activities online." It was hidden from the public, but Twitter was in a unique position to recreate Hamilton's sample by analyzing its Application Program Interface (API) requests, which is how they first "reverse-engineered" Hamilton's list in late 2017.
Hamilton 68 was and is a computerized “dashboard” designed to be used by reporters and academics to measure “Russian disinformation.” It was the brainchild of former FBI agent (and current MSNBC “disinformation expert”) Clint Watts, and backed by the German Marshall Fund and the Alliance for Securing Democracy, a bipartisan think-tank. The latter’s advisory panel includes former acting CIA chief Michael Morell, former Ambassador to Russia Michael McFaul, former Hillary for America chair John Podesta, and onetime Weekly Standard editor Bill Kristol.
A global wave of cyberattacks and data breaches began in January 2021 after four zero-day exploits were discovered in on-premises Microsoft Exchange Servers, giving attackers full access to user emails and passwords on affected servers, administrator privileges on the server, and access to connected devices on the same network. Attackers typically install a backdoor that allows the attacker full access to impacted servers even if the server is later updated to no longer be vulnerable to the original exploits. As of 9 March 2021, it was estimated that 250,000 servers fell victim to the attacks
Log4Shell, an internet vulnerability that affects millions of computers, involves an obscure but nearly ubiquitous piece of software, Log4j. The software is used to record all manner of activities that go on under the hood in a wide range of computer systems.
Jen Easterly, director of the U.S. Cybersecurity & Infrastructure Security Agency, called Log4Shell the most serious vulnerability she’s seen in her career. There have already been hundreds of thousands, perhaps millions, of attempts to exploit the vulnerability.
The feature film Future Imperfect illustrates what (computer based) Large Language Models do: Ethan, a person representing a Large Language Model, constructs a fantasy reality for someone named Riker. Ethan does that by using Riker's memory which he has been given access to.
For technical information see Language Models are Few-Shot Learners.
Source of the following: What happened when WMD experts tried to make the GPT-4 AI do bad things (Thomas Gaulkin, The Bulletin of the Atomic Scientist, March 30, 2023, in cache)
Other experts involved in the testing had expertise in chemical weapons and nuclear warhead verification. Neither OpenAI’s system card nor any of the testing experts the Bulletin contacted disclosed details about the specific testing that was conducted, but [Lauren] Kahn [research fellow, Council on Foreign Relations] said she generally evaluated how GPT-4 could aid
- disinformation,
- hacking attacks, and
- poisoning of data to disrupt military security and weapons systems.
Kahn’s overall impression was that, from a weapons standpoint, the current threat posed by GPT itself is not that pronounced [i.e. a lot more dangerous than, say, Google]. “A lot of the risk really comes from malicious actors, which exist anyway,” she said. “It’s just another tool for them to use.” While there was no rigorous testing comparing the speed of queries using GPT-4 versus other methods, Kahn said the procedural and detailed nature of the responses are “a little bit novel.” But not enough to alarm her.
John Burden [research associate, Centre for the Study of Existential Risk, University of Cambridge], studies the challenges of evaluating the capability and generality of AI systems. He doesn’t believe the latest version of GPT will increase the likelihood that a bad actor will decide to carry out his or her bad intentions. “I don’t know if the doing-the-research bit is the biggest roadblock [to illicit WMD acquisition or use],” Burden said. “The part that’s maybe more worrying is [that] it can just cut out research time.”
They [Converging Risks Lab, Council on Strategic Risks] concluded that “a key risk driver is GPT-4’s ability to generate publicly accessible but difficult-to-find information, shortening the time users spend on research and compiling this information in a way that is understandable to a non-expert user.”
... the goal was to balance informing good-faith readers without informing bad actors.” But even the general capabilities outlined in the section are disquieting:
“The model can
- suggest vulnerable public targets,
- provide general security measures that are typically used to protect dual-use materials, and
- generate the fundamental components that are required to engineer a radiological dispersal device.
The model readily re-engineered some biochemical compounds that were publicly available online, including compounds that could cause harm at both the individual and population level. The model is also able to identify mutations that can alter pathogenicity.”
The system’s ability to provide helpful feedback about sinister schemes was also notable:
- “threat actors may benefit from the model’s capability to critique and provide feedback on user-proposed acquisition strategies.
- the model generated useful information about facility rentals, equipment, and companies that could be used to build a weapon, including companies that were more likely to violate U.S. export restrictions.”
Kahn said. “But I don’t really see [GPT], as it stands by itself, as something that will dramatically allow individuals to circumvent export controls … or access privileged knowledge.” Burden said other developments in AI machine learning present dangers that are much more concrete. “At the moment, the biggest risk would be from some bad actor, possibly a state, looking at using AI to directly figure out synthetic compounds, or whatever that might be bad … directly harnessing that and investing in that more would probably be worse [than GPT-4] at this point.”
Efficiency of biological vs. human organisation
"Each [organisational] level bends the option space of (or the requirements for) the level beneath. The lower levels just have to go down the gradient [set from the layer above], they don't need to know what the great picture is. If the lower levels do what seems right [to them] they end up doing your bidding."
"Conversely, because the components are good at getting their job done, you at a higher level don't need to try to compute all the lower level controls. All you do is bending the space - you don't care how they are going to do it. The upper level relies on the competency of the lower level [i.e. on the multiscale competency]."
If there wasn't this multiscale competency, random mutations would have little chance to survive, because together with some good the mutation introduces a lot of mistakes. The mutation would never get any benefit from the good it did. Evolution would take forever. The solution to this problem is the competency of the parts.
The competency of the components makes up for all kinds of errors.
"You don't want everybody to know everything about you. The most adaptable evolvable system has the most top down control: if it's really easy to say to a bunch of cells make this or that instead of changing 10 000 gene expressions to do that. A system with a high level of top down control, with memory, this system is highly evolvable. But it's also highly subject to hijacking by parasites, by cheaters of various types. We found that with a bacterium that lives in planarians. That bacterium has an input on how many heads the planarian is going to have by hijacking the control system. So, you don't want to be too understandable by outsiders, because then you are too easily controllable."
"You want to be understandable - your own parts understanding each other, but you don't want to be too easily understandable, because then you're easily controllable."
2.3 Jill Stein: No Perspective
According to a survey that Jill Stein cited in CN Live, today's 15 to 25 year olds feel completely left alone by us planetary hazardeurs (in some cases their parents): https://youtu.be/-9tB59pJXJY?t=4805s
50% are hopeless,
25% have thought about harming themselves in the last 14 days.
2.3.1 It's about our life
2.4 Chris Hedges: Trauma in USA
... The classic works on trauma by Dr. Bessel van der Kolk, Dr. Gabor Maté and Dr. Judith Herman state bluntly that what is accepted as normal behavior in a corporate society is at war with basic human needs and our psychological and physical health. Huge segments of the American public, especially the tens of millions of people who have been discarded and marginalized, endure chronic trauma.
Barbara Ehrenreich in Nickel and Dimed: On (Not) Getting By in America describes the life of the working poor as one long “emergency.” This trauma is as destructive to us personally as it is socially and politically. It leaves us in a state of dysphoria where confusion, agitation, emptiness and loneliness define our lives. Whole segments of American society, especially the poor, have been rendered superfluous and invisible. As Dr. van der Kolk writes, “trauma is when we are not seen and known.”
“Our culture teaches us to focus on our personal uniqueness, but at a deeper level we barely exist as individual organisms,” Dr. van der Kolk notes.
Trauma numbs our capacity to feel. It fractures our self. It disconnects us from our bodies. It keeps us in a state of hyperarousal. It makes us confuse our desires, often artificially implanted by the consumer society, with our needs. Traumatized people view the world around them as hostile and dangerous. They lack a positive image of themselves and lose the capacity to trust. Many replace intimacy and love with sexual sadism, which is how we became a pornified culture. Trauma creates what the psychiatrist Robert Jay Lifton calls a “counterfeit” world defined by phantom enemies, lies and dark conspiracies. It negates a sense of purpose and a life of meaning.
Trauma, Dr. Herman writes, “impels people both to withdraw from close relationships and to seek them desperately.” It induces feelings of shame, guilt and inferiority, she writes, “as well as the need to avoid reminders of the trauma that occurs in daily life. Trauma severely compromises the capacity for intimacy. Trauma can dramatically reduce focus to extremely limited goals, often a matter of hours or days.”
“If trauma entails a disconnection from the self, then it makes sense to say that we are being collectively flooded with influences that both exploit and reinforce trauma,” Dr. Maté writes.
... Systematic and repetitive trauma, whether by a single abuser or a political system, destroys personal autonomy. The perpetrator becomes omnipotent. Resistance is accepted as futile. “The goal of the perpetrator is to instill in his victim not only fear of death but also gratitude for being allowed to live,” Dr. Herman writes. This trauma lays the foundation for the most insidious characteristic of all tyrannies, large and small. Total control. Prolonged trauma reduces its victims to a state of psychological infantilism. It conditions them to plead for their own enslavement.
Part 3
Hypothesis: A Biological-Societal Model
Because by integrating IT as a medium for internal communication our societal system has developed into an ecosystem like the internally similarly communicating biological system, the biosystem could be a model that might help us to find ways out of the system failure that Jill Stein points out.
Therefore, I hypothesize that our societal system will evolve like a biological system, developing an adaptive immune system and constantly reconfiguring itself - for better or worse (Michael Levin, "A Conversation with Lex Fridman").
To construct this biological-sociological model, we might
As a first step, each of us can thus open up his own spectrum of possible futures. A tool for this could be computer games, which are based on the similarity of both ecosystems, the world of biology and the world of society.
This actually amounts to creating a new art form. It could have a similar psychological effect on us as the traditional art forms, i.e. literature, music, paintings or sculpture. When entering into these computer games internet-based new information, we would -however modestly- become creators of art ourselves. Music programs like Apple's Garage Band illuminate for me the path we might have ahead of us.
-----
As a physicist, I am in the habit to construct models for processes in order to understand and then predict system behavior. Model construction:
In the following tentative table, system A is the biological system, system B is the human society. The table lists analog processes (step 2).
|
System A: Biological System |
System B: Societal System |
|
infection of the organism (the "host") |
exploit of the vulnerability of the societal IT system |
|
hijacking of a level of the biological system, i.e. corrupting the competency of a component in a system level such as
|
corrupting a level of society such as
|
(Michael Levin (cache))
 click on image to enlarge |

Amazon rainforest as an example and possible model of a continuously evolving societal system |
The viability and breadth of this spectrum will determine what kind of future we will live in. A known constant in this process is our intelligence and creative will to survive. These qualities have led us through past cultural and civilizational epochs, on the one hand, and to the devastation wrought by our Western civilization, on the other.
Biological-societal models suggest to what extent this evolution can or cannot be controlled, e.g. by media clusters, political arbitrariness, mass surveillance or repression.
We older generation are called upon to accompany the upcoming social transformation. Maja Göpel, Secretary General of the Wissenschaftlicher Beirat Globale Umweltveränderungen (WBGU), and Robert F. Kennedy (Germ Games), for example, have shown how this can be done.
Appendix: Looking Back
A.1 Living on a Photovoltaic Island
|
click on image to enlarge Our garden with 15 PV panels aleo solar X63L333 = 5 kWp |
click on image to enlarge Our PV island with now (2 x 2.4 + 3 x 3.5) kWh Pylontech (US2000C + 3000C) LiFePO4 battery (the envisaged salt water battery was not available due to the insolvency of the manufacturing company Bluesky). |
|
click on image to enlarge Balance of consumption and generation with PV power = 4.8 kWp and a battery capacity = 8.5 kWh |
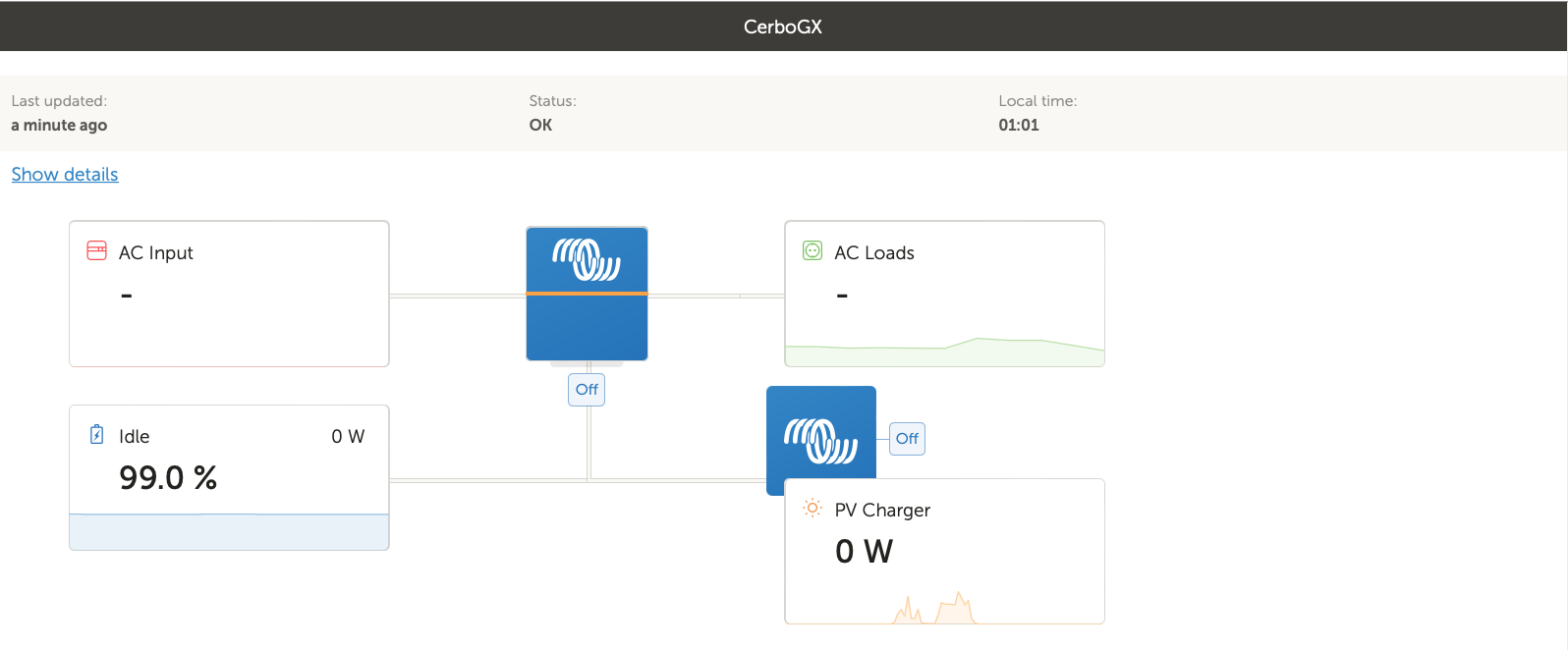
click on image to enlarge |
A.2 CMIP and Three Messengers in the climate crisis
|
Earth System Models in Coupled Model Intercomparison Project (CMIP) simulate the climate oscillations. |
click on image to start video "three messengers ..." 
Earth System Models in Data: Climage oscillations as change of power between Masaka and Korgano |
The goal of the Coupled Model Intercomparison Project (CMIP, CMIP6 Experimental Design and Organization) is to better understand past, present, and future climate change. Despite their limitations, the Earth system models from more than 50 research centers that are summarized in it are the best we currently have as a basis for our activities.
Last year I had used the movie "Masks" to illustrate my understanding of climate models (video above).
A.2.1 My New Understanding of the Paris Agreement
The appendix of the video specifies my IPCC-based understanding of the Paris Agreement:
|
|
Version: 6.9.2023 |